How to Access and Monitor IoT Devices Securely
Uncover effective strategies for managing IoT devices remotely at scale. Our comprehensive guide provides security teams with solutions for secure and efficient IoT device control.
Article Contents
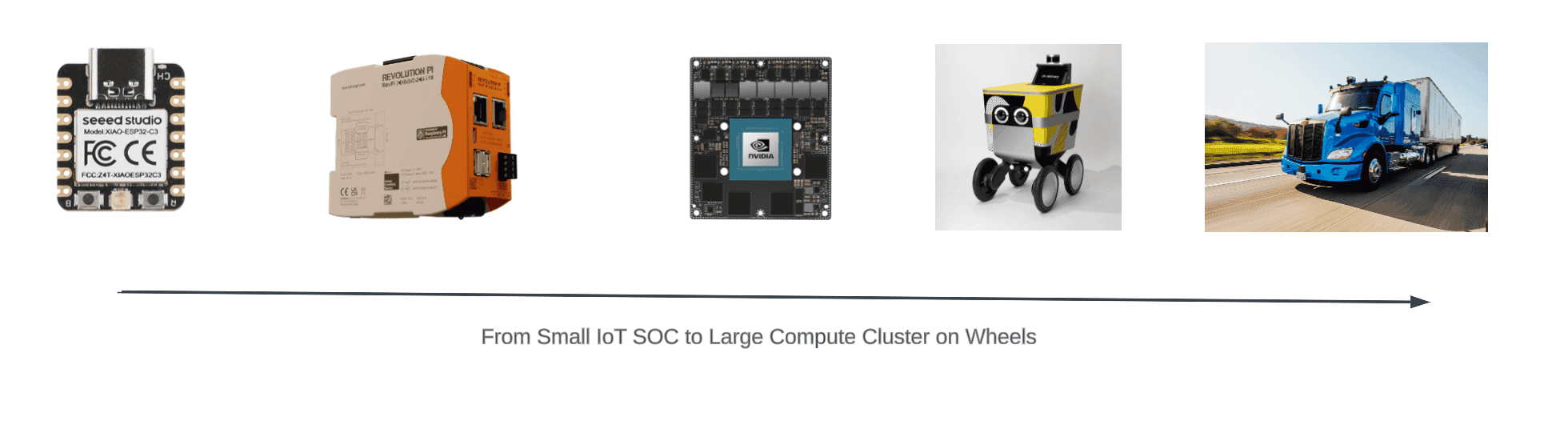
In this article, we’ll cover how to securely access and monitor IoT devices. IoT (the Internet of Things) has seen a 23% YoY increase in devices that can range from tiny embedded devices to trucks. Consumers are often familiar with IoT devices and the problems they present.
This article is focused on industrial usages of IoT, such as Retail & Hospitality, Transportation & Logistics, OEM and Manufacturing. It addresses teams that deploy large amounts of IoT devices and devices at the edge to help with automation — with a focus on industry usage and methods of remote access. Consumer IoT devices can fit into this, but often they’ll communicate over a specific API/protocol back to a central server.
What is IoT remote monitoring and device management?
As industries roll out IoT devices, there will often be a large amount of them. IoT is a broad term, but for the sake of simplicity, we’ll define it as an isolated compute that can connect to the internet. These use cases can range from an industrial ARM Raspberry Pi to a full-blown supercomputer piloting a self-driving truck.
IoT remote monitoring and device management strategies are almost always required due to the distributed, and transient nature of IoT devices, which can be deployed across multiple sites and might even be moving. This means connectivity might be spotty, resulting in difficulty patching or updating firmware or software.
Most small IoT devices communicate with central servers using MQTT, as it’s designed for low-bandwidth, high-latency, unreliable networks. This makes it perfect for IoT applications where network bandwidth is often at a premium. As IoT deployment scales, it’s common in the industrial domain to require access to IoT devices. This will be the core topic of this post.
Protocols for remotely accessing IoT devices
Companies deploy a range of methods and tools for accessing IoT devices. In 2023, there are many tools available to streamline setup of IoT devices that support configuration and access. AWS offers a range of IoT offerings, but people not using AWS can take a more traditional approach of using SSH with a VPN or Proxy Connection.
AWS IoT Core
Device Gateway: This provides a communication layer for devices to connect to the internet and interact with AWS services. It supports MQTT, HTTP, and WebSockets protocols to accommodate various types of devices and their requirements.
Windows 10 IoT Core Device
Microsoft systems are the least popular IoT devices, since IoT devices are often Linux based. It’s rare to use RDP to access IoT devices. Microsoft does offer a few tools to make accessing IoT devices easy: Windows 10 IoT Core Device. Windows 10 IoT Core is a version of Windows 10 that is optimized for smaller devices with or without a display that run on both ARM and x86/x64 devices. This version of Windows is designed for IoT devices and provides a scaled-back, minimal Windows environment that can run a single application, typically one created with Universal Windows Platform (UWP).
VPN
A Virtual Private Network (VPN) can be a secure way to remotely connect to Internet of Things (IoT) devices, especially when these devices are behind a firewall or a private network. In more professional or industrial settings where IoT devices may be handling sensitive data or where direct remote access to devices is required, the use of VPNs can be more common. IT professionals might use a VPN to access an IoT device on a remote network securely or to ensure secure communication between devices on different networks.
A downside that Teleport solves is the ability to terminate connections after a period of time automatically. Since Teleport uses short-lived certificates, access is scoped for one day. If the user needs to access the network again, they’ll need to authenticate again.
SSH
Hobbyists are likely to be very familiar with using SSH to access IoT devices, it’s simple to use and can be quickly deployed to setup Headless (no monitor needed) hobby devices such as Raspberry Pi, and other single-board computers (SBCs) such as the Jetson Nano or Intel Edison. More robust industrial Systems may use specific operating systems, such as ROS - Robot Operating System to connect over SSH. If using SSH, you may need to set up port forwarding. This should be done cautiously, however, as it can expose your device, and potentially your entire network, to the internet, creating potential security risks.
SSH is Secure Shell Protocol, and there is a range of SSH tooling. The most common is OpenSSH, but other open-source options exist. Two great ones are Dropbear SSH which is only 110kb, or Teleport SSH, which can access servers using certificates for short-lived and secure access.
Physical access
In the industrial setting, it’s common for people to obtain physical access to devices for troubleshooting. This can range from serial interfaces, console ports, or simply direct wired connections with an ethernet cable. Unless there is a critical bug or major maintenance is required, physical access will be the last option.
Framework for access
Networks & firewalls
IoT devices are often put in the field (warehouse/hospital/factory) and the networks they are connected to may be untrusted or out of control of the end user. If a team has access to a firewall, it’s a common pattern to ask the team to open a connection for the firewall/router. This is a security anti-pattern since opening one-off IPs can easily become an attack vector into a network and it’s better to provide a reverse proxy to provide access.
A second problem is trying to figure out the IP Address of the IoT device. While in some controlled environments, it’s possible to keep an inventory of IPs, these often change.
Managing inventory
Maintaining an up-to-date inventory of IoT devices is crucial. Teams should seek systems that allow devices to send periodic "heartbeats" back to a centralized location. This heartbeat functionality ensures that the status and location of each IoT device are continuously tracked and recorded. By monitoring the heartbeat signals, the organization can stay informed about the presence and health of their IoT assets, enabling effective management and troubleshooting when necessary.
Managing multiple sites
It’s common for IoT devices to be deployed to multiple locations and/or on a mobile LTE connection. Keeping track of these devices requires another zero-trust approach. This can be helpful when trying to access a remote location.
Using Teleport to remotely access IoT devices
Teleport is an open-source secure access platform that can provide real-time access to IoT devices. It’s an IoT solution used by Worldcoin, Embark Truck and others. Worldcoin leverages Teleport to provide firmware updates with little disruption and minimal downtime.
Instead of relying upon VPNs, Teleport is a Zero-trust solution for secure remote access. This removes the need for dealing with Firewalls and Teleport can also keep an inventory of hosts.
Teleport provides a range of secure authentication methods, from hardware-backed tokens to SSO. The flexibility of an RBAC system can provide powerful authorization methods, for example only letting developers access robotics systems during specific maintenance hours.
He’s an example of how Teleport accesses remote IoT devices.
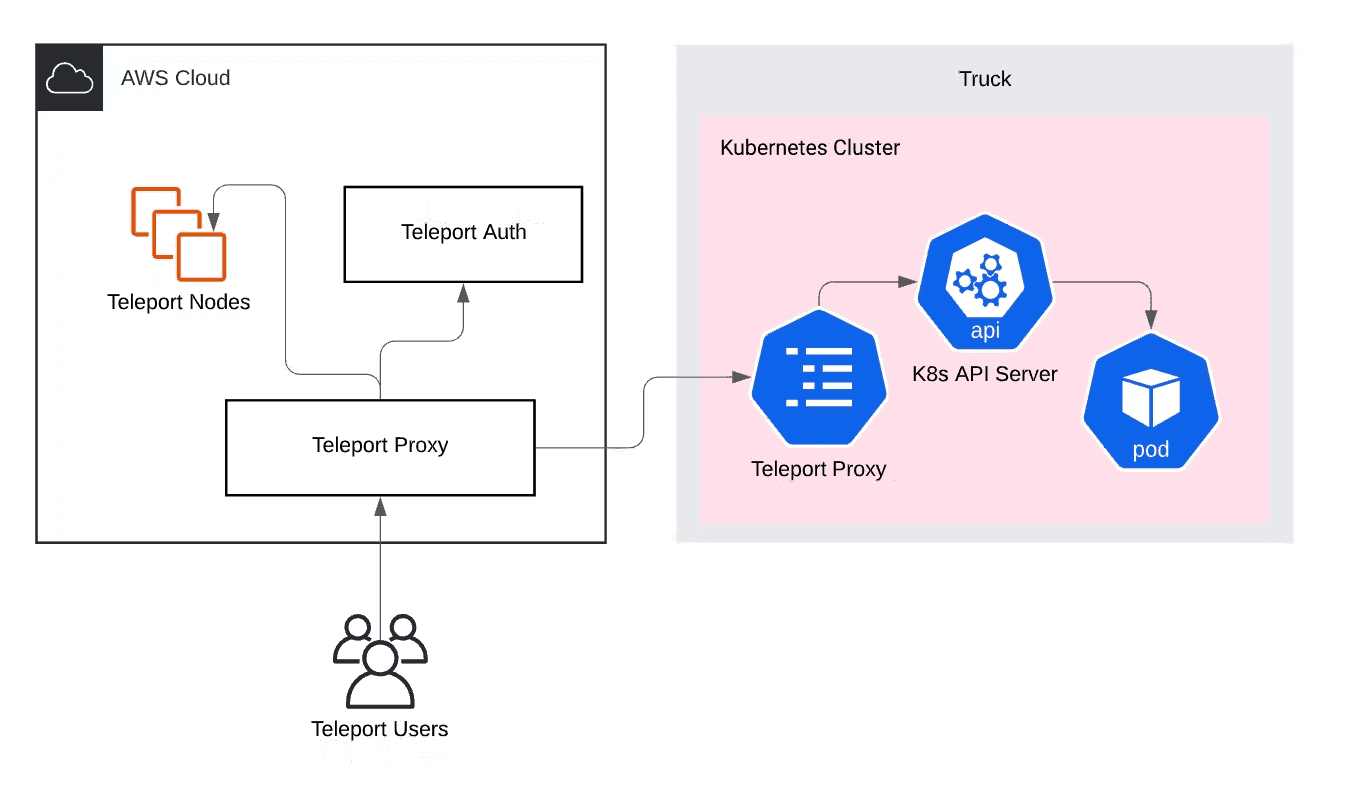
Image from How to SSH into a Self-Driving Vehicle
These are a few other benefits of using Teleport for IoT devices:
IoT Requirements
Teleport Feature
| IoT Requirement | Teleport Feature |
| The ability to manage a large amount of devices deployed to different environments. | IoT devices are often geographically distributed, requiring remote access capability. Teleport provides access to SSH servers and Kubernetes clusters anywhere, without requiring a VPN |
| Must support ARM/ARM32/ARM64. | Raspberry Pi, Nvidia Jetson and other ARM-based mini-computers operate the ARM operating system. Teleport provides a suite of open-source binaries that run on these operating systems. |
| Connectivity in restrictive environments. | IoT devices are often located behind restrictive proxies or firewalls. Along with IoT mode, Teleport can operate Trusted Clusters, which can be opened up to provide access to a site's cluster of IoT devices. |
IoT remote access conclusion
If you're looking to get real-time remote access to your IoT devices, from a Raspberry Pi to a self-driving supercomputer, Teleport might be a good solution for you. Teleport can be utilized as a cloud-based or self-hosted solution with a Teleport 14-day trial.
FAQ for Remote Access
What is IoT remote monitoring and device management?
IoT remote monitoring and device management involves controlling, updating, and troubleshooting IoT devices that are deployed across various sites or even moving locations.
What is IoT remote monitoring and device management?
IoT remote monitoring and device management involves controlling, updating, and troubleshooting IoT devices that are deployed across various sites or even moving locations.
What communication protocol do most small IoT devices use?
Most small IoT devices communicate with servers using MQTT, a protocol designed for low-bandwidth, high-latency or unreliable networks.
What are some methods and tools for accessing IoT devices remotely?
Companies use a range of methods and tools, including AWS IoT offerings, SSH, VPN, or a Proxy Connection. Each has its benefits and drawbacks depending on the situation.
What is AWS IoT Core?
AWS IoT Core is a cloud service that lets connected devices easily and securely interact with cloud applications and other devices. It provides a communication layer for devices to connect to the internet and interact with AWS services, supporting MQTT, HTTP and WebSockets protocols.
How does a virtual private network (VPN) help in IoT?
A VPN can provide a secure way to remotely connect to IoT devices, especially when these devices are behind a firewall or on a private network.
Why is SSH commonly used for accessing IoT devices?
SSH is simple to use and can be quickly deployed for setting up IoT devices without needing a monitor (headless devices). However, it does come with potential security risks when not used properly.
What is the role of physical access in managing IoT devices?
In industrial settings, it's common to obtain physical access to devices for troubleshooting purposes. This can include using USB cables, serial consoles, GPIO pins or development boards, among other tools.
Why is managing the inventory of IoT devices important?
Keeping track of your IoT devices is critical as these devices can be spread across multiple locations or even on mobile connections. It helps ensure that all devices are updated, secure, and functioning as intended.
What is Teleport and how can it help with IoT remote access?
Teleport is an open-source access platform that can provide real-time, secure access to IoT devices. It eliminates the need for dealing with firewalls, keeps an inventory of hosts, and offers flexible, powerful authorization methods.