
Teleport
Database Access with Microsoft SQL Server with Active Directory authentication
- Version 17.x
- Version 16.x
- Version 15.x
- Version 14.x
- Older Versions
How to Connect to Microsoft SQL Server Remotely Using Teleport
Length: 36:23
Teleport can provide secure access to Microsoft SQL Server via the Teleport Database Service. This allows for fine-grained access control through Teleport's RBAC.
In this guide, you will:
- Configure your Microsoft SQL Server database with Active Directory authentication.
- Add the database to your Teleport cluster.
- Connect to the database via Teleport
This guide will focus on Amazon RDS for SQL Server using AWS-managed Active Directory authentication.
How it works
The Teleport Database Service joins the same Active Directory domain as the SQL Server database and uses the Kerberos protocol to authenticate with SQL Server. When a user connects to SQL Server via Teleport, the Database Service obtains a service ticket from Active Directory, then uses a long-term key for the database user to decrypt the ticket and connect to SQL Server. At that point, the Database Service forwards user traffic to the database.
Prerequisites
-
A running Teleport cluster version 16.1.0 or above. If you want to get started with Teleport, sign up for a free trial or set up a demo environment.
-
The
tctladmin tool andtshclient tool.Visit Installation for instructions on downloading
tctlandtsh.
- A SQL Server database with Active Directory authentication enabled.
- A SQL Server network listener configured with a Certificate using Subject Alternative Names
- A Windows machine joined to the same Active Directory domain as the database.
- A Linux node joined to the same Active Directory domain as the database. This guide will walk you through the joining steps if you don't have one.
- To check that you can connect to your Teleport cluster, sign in with
tsh login, then verify that you can runtctlcommands using your current credentials.tctlis supported on macOS and Linux machines. For example:If you can connect to the cluster and run thetsh login --proxy=teleport.example.com --user=[email protected]tctl statusCluster teleport.example.com
Version 16.1.0
CA pin sha256:abdc1245efgh5678abdc1245efgh5678abdc1245efgh5678abdc1245efgh5678
tctl statuscommand, you can use your current credentials to run subsequenttctlcommands from your workstation. If you host your own Teleport cluster, you can also runtctlcommands on the computer that hosts the Teleport Auth Service for full permissions.
Step 1/7. Create a Teleport user
To modify an existing user to provide access to the Database Service, see Database Access Access Controls
Create a local Teleport user with the built-in access role:
tctl users add \ --roles=access \ --db-users="*" \ --db-names="*" \ alice
Create a local Teleport user with the built-in access and requester roles:
tctl users add \ --roles=access,requester \ --db-users="*" \ --db-names="*" \ alice
| Flag | Description |
|---|---|
--roles | List of roles to assign to the user. The builtin access role allows them to connect to any database server registered with Teleport. |
--db-users | List of database usernames the user will be allowed to use when connecting to the databases. A wildcard allows any user. |
--db-names | List of logical databases (aka schemas) the user will be allowed to connect to within a database server. A wildcard allows any database. |
Database names are only enforced for PostgreSQL, MongoDB, and Cloud Spanner databases.
For more detailed information about database access controls and how to restrict access see RBAC documentation.
Step 2/7. Join the Linux node to Active Directory
You can skip this step if you already have a Linux node joined to the same Active Directory domain as your SQL Server instance.
The Linux node where the Database Service will run must be joined to the same Active Directory domain as the SQL Server database.
Note that in order to be able to join, the Linux node must be able to resolve your Active Directory fully-qualified domain name. For example, for AWS-managed AD, use nameservers provided under "Networking details" on the directory's overview page.
Install necessary packages:
sudo apt-get updatesudo apt-get -y install sssd realmd krb5-user samba-common packagekit adcli
sudo yum -y updatesudo yum -y install sssd realmd krb5-workstation samba-common-tools
Edit /etc/krb5.conf to disable reverse DNS resolution and set the default
realm. Make sure that the [realms] section contains your domain definition
and has admin_server and kdc fields set pointing to the domain controllers:
[libdefaults]
default_realm = EXAMPLE.COM
rdns = false
[realms]
EXAMPLE.COM = {
kdc = example.com
admin_server = example.com
}
Join the realm:
Note that the realm name in [email protected] must be capital case,
otherwise the node might not be able to join.
To confirm the node has joined the realm, use the realm list command:
sudo realm listexample.com type: kerberos realm-name: EXAMPLE.COM domain-name: example.com configured: kerberos-member server-software: active-directory client-software: sssd ...
Step 3/7. Create keytab file
Teleport requires a keytab file to obtain Kerberos service tickets from your
Active Directory for authentication with SQL Server. The easiest way to generate
it is to use the adutil Linux CLI utility.
Install adutil on the Linux node you have joined to your Active Directory
domain:
curl https://packages.microsoft.com/keys/microsoft.asc | sudo apt-key add -sudo curl https://packages.microsoft.com/config/ubuntu/18.04/prod.list | sudo tee /etc/apt/sources.list.d/msprod.listsudo apt-get updatesudo ACCEPT_EULA=Y apt-get install -y adutil
sudo wget -qO /etc/apt/trusted.gpg.d/microsoft.asc https://packages.microsoft.com/keys/microsoft.ascsudo curl https://packages.microsoft.com/config/ubuntu/20.04/prod.list | sudo tee /etc/apt/sources.list.d/msprod.listsudo apt-get updatesudo ACCEPT_EULA=Y apt-get install -y adutil
sudo curl -o /etc/yum.repos.d/msprod.repo https://packages.microsoft.com/config/rhel/8/prod.reposudo ACCEPT_EULA=Y yum install -y adutil
Log in to Active Directory using the kinit command:
kinit [email protected]
Use the adutil keytab create command to generate keytab entries for each
Active Directory user that will be connecting to the SQL Server database:
adutil keytab create teleport.keytab aliceadutil keytab create teleport.keytab bob
You will be prompted to enter each user's password. All keytab entries will
be merged into the same teleport.keytab file.
For the adutil keytab create command to work, each user account must be
assigned a Service Principal Name, otherwise the command will not be able
to determine its kvno (key version number).
To check if the user has any SPNs assigned, run the following command on the Windows machine joined to your Active Directory domain:
setspn -L alice
To assign an SPN to a user account, use the following command:
setspn -s user/alice alice
You can verify entries in the keytab file using klist command:
klist -ke teleport.keytabKeytab name: FILE:teleport.keytabKVNO Principal---- -------------------------------------------------------------------------- 5 [email protected] (aes256-cts-hmac-sha1-96) 2 [email protected] (aes256-cts-hmac-sha1-96)
You must update the keytab file after updating a user's password to avoid authentication failures.
Step 4/7. Set up the Teleport Database Service
The Database Service requires a valid join token to join your Teleport cluster.
Run the following tctl command and save the token output in /tmp/token
on the server that will run the Database Service:
tctl tokens add --type=db --format=textabcd123-insecure-do-not-use-this
Install Teleport on your Linux server:
-
Assign edition to one of the following, depending on your Teleport edition:
Edition Value Teleport Enterprise Cloud cloudTeleport Enterprise (Self-Hosted) enterpriseTeleport Community Edition oss -
Get the version of Teleport to install. If you have automatic agent updates enabled in your cluster, query the latest Teleport version that is compatible with the updater:
TELEPORT_DOMAIN=example.teleport.comTELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"Otherwise, get the version of your Teleport cluster:
TELEPORT_DOMAIN=example.teleport.comTELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/ping | jq -r '.server_version')" -
Install Teleport on your Linux server:
curl https://goteleport.com/static/install.sh | bash -s ${TELEPORT_VERSION} editionThe installation script detects the package manager on your Linux server and uses it to install Teleport binaries. To customize your installation, learn about the Teleport package repositories in the installation guide.
Teleport Database Service must run on a Linux server joined to the same Active Directory domain as the SQL Server.
Configure the Teleport Database Service. Make sure to update --proxy to
point to your Teleport Proxy Service address and --uri to the SQL Server
endpoint.
sudo teleport db configure create \ -o file \ --token=/tmp/token \ --proxy=teleport.example.com:443 \ --name=sqlserver \ --protocol=sqlserver \ --uri=sqlserver.example.com:1433 \ --ad-keytab-file=/path/to/teleport.keytab \ --ad-domain=EXAMPLE.COM \ --ad-spn=MSSQLSvc/sqlserver.example.com:1433 \ --labels=env=dev
Configure the Teleport Database Service. Make sure to update --proxy to
point to your Teleport Cloud tenant address and --uri to the SQL Server
endpoint.
sudo teleport db configure create \ -o file \ --token=/tmp/token \ --proxy=mytenant.teleport.sh:443 \ --name=sqlserver \ --protocol=sqlserver \ --uri=sqlserver.example.com:1433 \ --ad-keytab-file=/path/to/teleport.keytab \ --ad-domain=EXAMPLE.COM \ --ad-spn=MSSQLSvc/sqlserver.example.com:1433 \ --labels=env=dev
Provide Active Directory parameters:
| Flag | Description |
|---|---|
--ad-keytab-file | Path to Kerberos keytab file generated above. |
--ad-domain | Active Directory domain (Kerberos realm) that SQL Server is joined. |
--ad-spn | Service Principal Name for SQL Server to fetch Kerberos tickets for. |
Service Principal Name
You can use ldapsearch command to see the SPNs registered for your SQL
Server. Typically, they take a form of MSSQLSvc/<name>.<ad-domain>:<port>.
For example, an AWS RDS SQL Server named sqlserver and joined to an AWS managed
Active Directory domain EXAMPLE.COM will have the following SPNs registered:
ldapsearch -x -h example.com -D admin -W -b DC=example,DC=com servicePrincipalName...EC2AMAZ-4KN05DU, RDS, AWS Reserved, example.com
dn: CN=EC2AMAZ-4KN05DU,OU=RDS,OU=AWS Reserved,DC=example,DC=comservicePrincipalName: MSSQLSvc/sqlserver-rds.example.com:1433servicePrincipalName: MSSQLSvc/EC2AMAZ-4KN05DU.example.com:1433servicePrincipalName: MSSQLSvc/EC2AMAZ-4KN05DU.example.com...
Alternatively, you can look SPNs up in the Attribute Editor of the Active Directory Users and Computers dialog on your AD-joined Windows machine. The RDS SQL Server object typically resides under the AWS Reserved / RDS path:
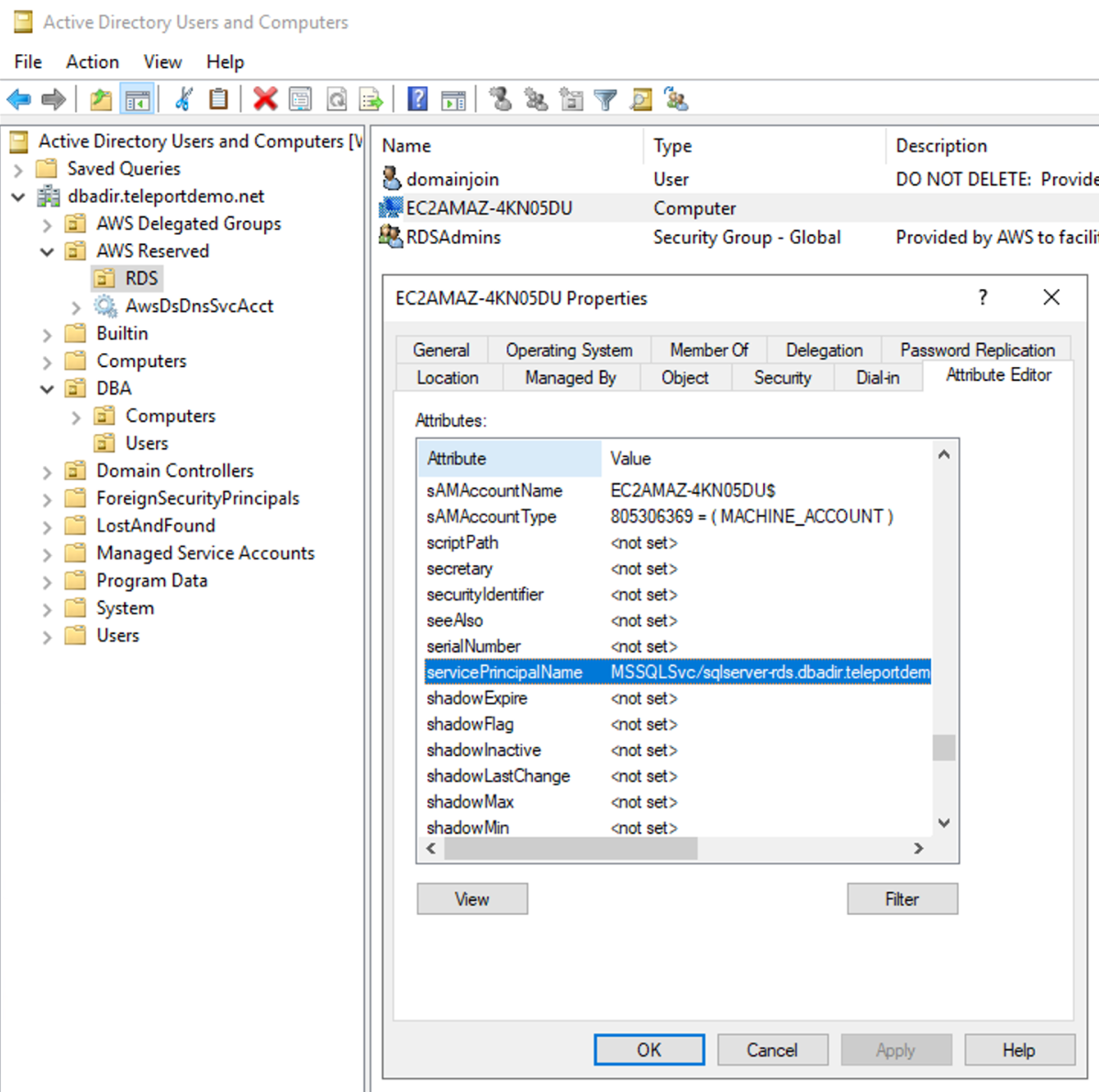
If you don't see Attribute Editor tab, make sure that "View > Advanced Features" toggle is enabled.
Step 5/7. Start the Database Service
Configure the Teleport Database Service to start automatically when the host boots up by creating a systemd service for it. The instructions depend on how you installed the Teleport Database Service.
On the host where you will run the Teleport Database Service, enable and start Teleport:
sudo systemctl enable teleportsudo systemctl start teleport
On the host where you will run the Teleport Database Service, create a systemd service configuration for Teleport, enable the Teleport service, and start Teleport:
sudo teleport install systemd -o /etc/systemd/system/teleport.servicesudo systemctl enable teleportsudo systemctl start teleport
You can check the status of the Teleport Database Service with systemctl status teleport
and view its logs with journalctl -fu teleport.
Step 6/7. Create SQL Server AD users
You can skip this step if you already have Active Directory logins in your SQL Server.
Connect to your SQL Server as an administrative account (e.g. sa) and create
logins that will use Active Directory authentication:
master> CREATE LOGIN [EXAMPLE\alice] FROM WINDOWS WITH DEFAULT_DATABASE = [master], DEFAULT_LANGUAGE = [us_english];
Step 7/7. Connect
Log in to your Teleport cluster. Your SQL Server database should appear in the list of available databases:
tsh login --proxy=teleport.example.com --user=alicetsh db lsName Description Labels
--------- ------------------- -------
sqlserver env=dev
tsh login --proxy=mytenant.teleport.sh --user=alicetsh db lsName Description Labels
--------- ------------------- -------
sqlserver env=dev
To retrieve credentials for a database and connect to it:
tsh db connect --db-user=teleport sqlserver
Either the sqlcmd or mssql-cli command-line clients should be available in
PATH in order to be able to connect. tsh attempts to run sqlcmd first and,
if it's not present on the PATH, runs mssql-cli.
If you have neither command-line clients available on your system, you can run the following command to start a local proxy server that you can connect to with your SQL Server client:
tsh proxy db --db-user=teleport --tunnel sqlserver
Read the Database Access GUI Clients guide for how to connect your DB GUI client to the local proxy.
To log out of the database and remove credentials:
tsh db logout sqlserver
Troubleshooting
Certificate error
If your tsh db connect error includes the following text, the certificate used by SQL Server is not a known Certificate Authority.
Error message: TLS Handshake failed: x509: certificate signed by unknown authority
To solve this, you can add the CA configuration to the database like the following:
databases:
- name: sqlserver
protocol: sqlserver
uri: sqlserver.example.com:1433
ad:
keytab_file: /path/to/teleport.keytab
domain: EXAMPLE.COM
spn: MSSQLSvc/sqlserver.example.com:1433
static_labels:
"env": "dev"
+ tls:
+ # Point it to your Database CA PEM certificate.
+ ca_cert_file: "rdsca.pem"
+ # If your database certificate has an empty CN filed, you must change
+ # the TLS mode to only verify the CA.
+ mode: verify-ca
If you’re unable to acquire the database CA, you can skip TLS verification by
providing the configuration tls.mode: "insecure". However, we do not recommend
skipping TLS verification in production environments.
Next steps
- Learn how to restrict access to certain users and databases.
- View the High Availability (HA) guide.
- Take a look at the YAML configuration reference.
- See the full CLI reference.
Further reading
- Manually join a Linux instance in the AWS documentation.
- Introduction to
adutilin the Microsoft documentation.