Articles by topic
- All
- AI
- AWS
- Access control
- Access requests
- Agentic AI
- Announcements
- Applications
- Audit
- Audit logs
- Automation
- Bastion
- Best Practices
- CI/CD
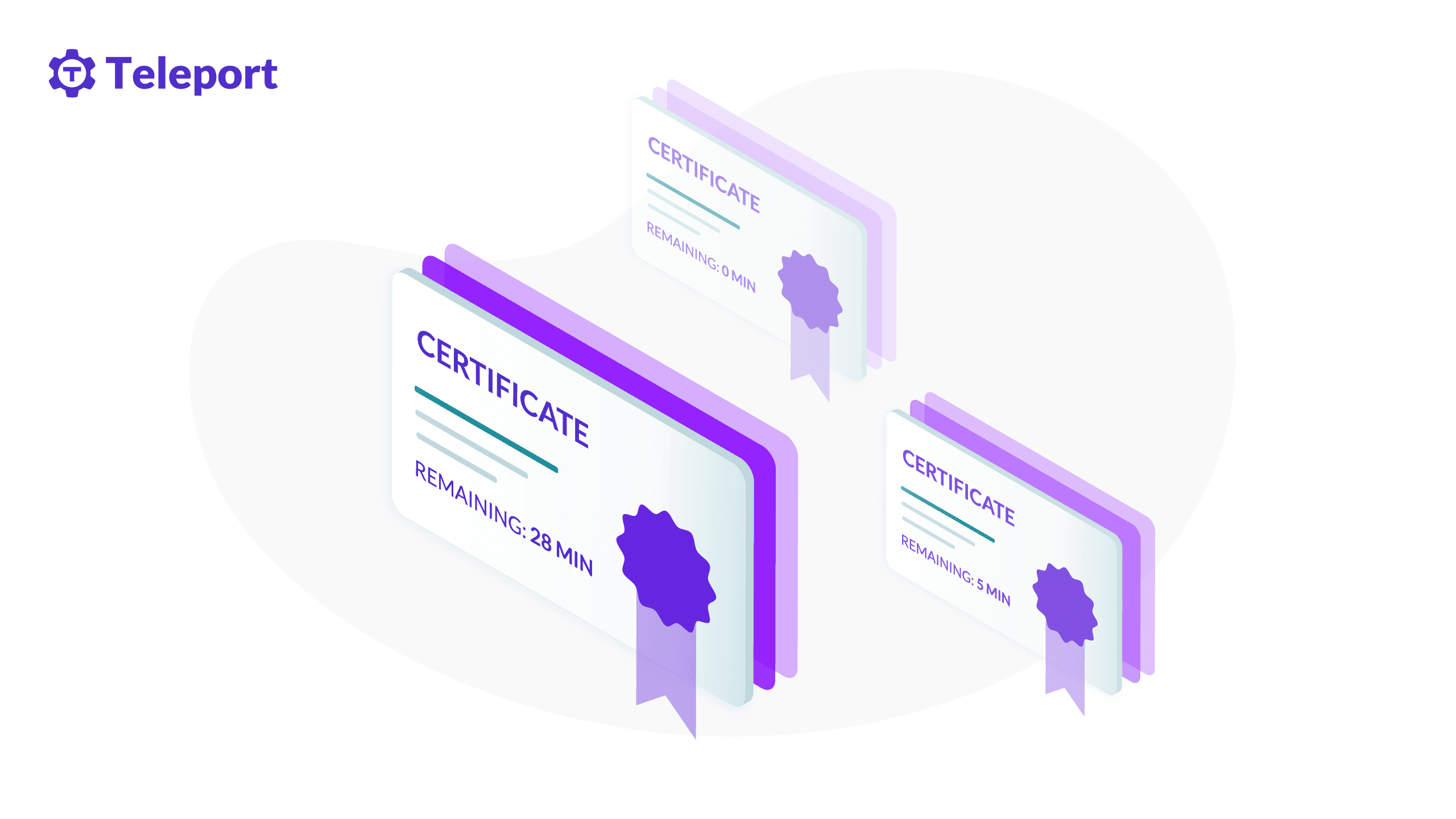
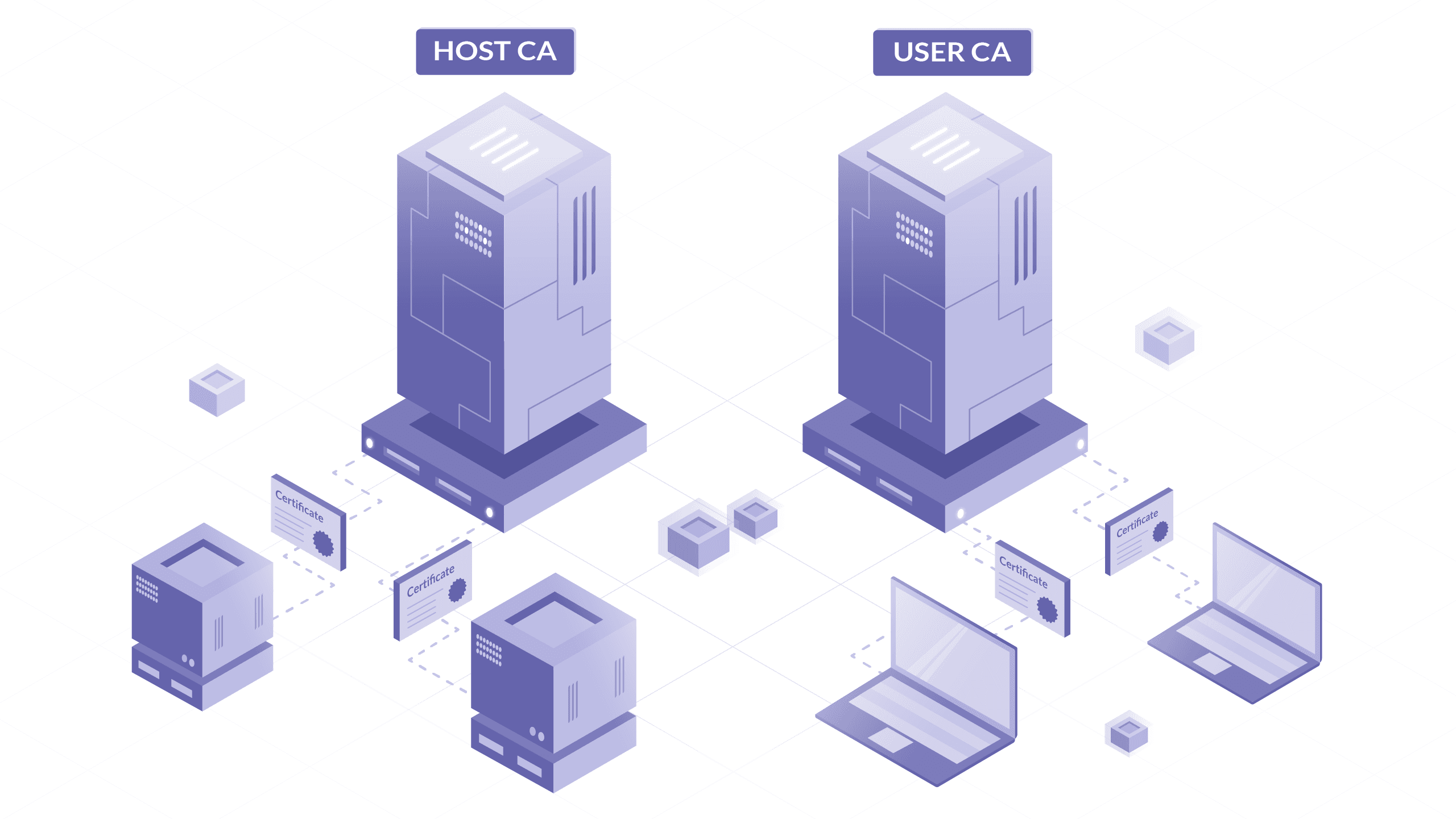
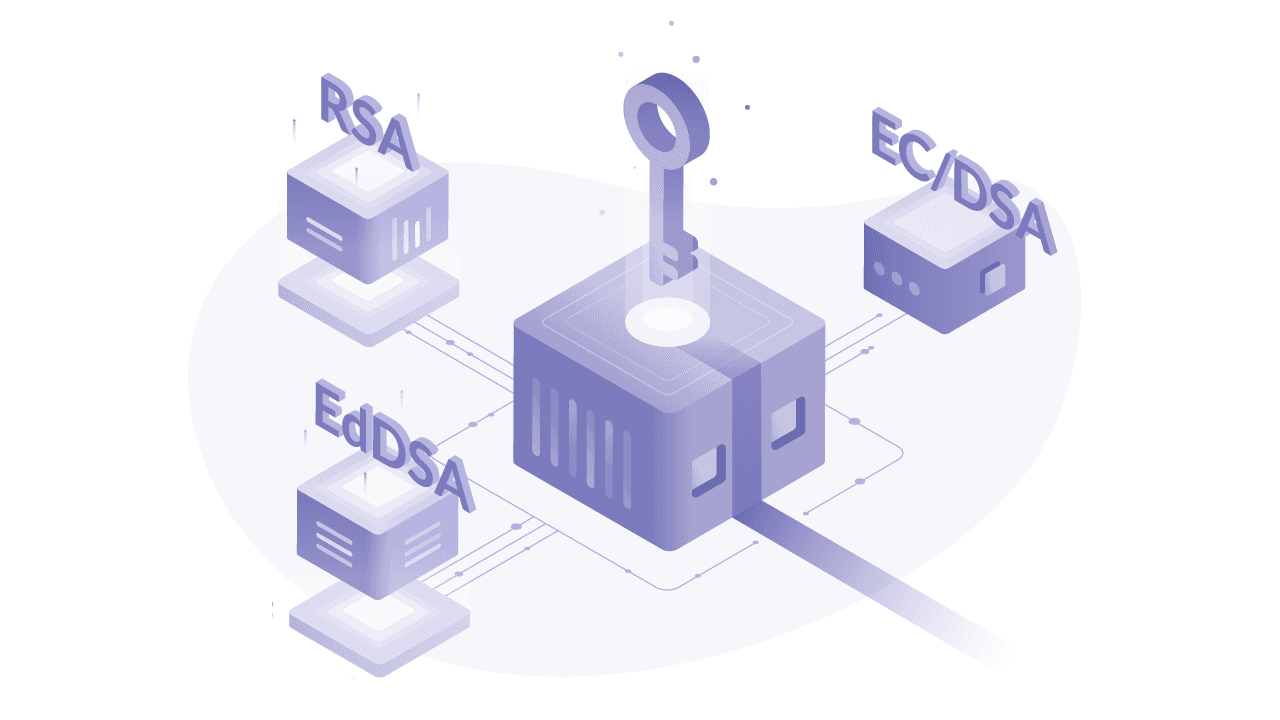
- Certificates
- Company
- Compliance
- Containers
- Credentials
- Cryptocurrency
- Cryptographic identity
- Cybersecurity
- DORA
- Databases
- Device trust
- EKS
- Engineer productivity
- Engineering
- Engineering velocity
- FedRAMP
- Git
- Governance
- Gravity
- Hybrid cloud
- Identity
- Identity Security
- Infrastructure Identity
- Infrastructure access
- Infrastructure resiliency
- Inside Teleport
- Istio
- Just-in-time access
- KubeCon
- Kubernetes
- Least privilege
- MCP
- Machine and Workload Identity
- Microservices
- MongoDB
- Multicloud
- Newsletter
- OSS
- Okta
- PAM
- Passwordless
- Performance
- Policy
- Postgres
- Programming
- RBAC
- Research
- SAML
- SOC 2
- SPIFFE
- SSH
- SSO
- Security
- Security Policy Evaluation Framework
- Shadow access
- Snowflake
- Static credentials
- Teleport
- Teleport platform security
- Terraform
- VNET
- VPN
- WebAuthn
- Windows
- Z3
- Zero Trust
- Zero trust
- featured
Blog Posts by topic SSH

Subscribe to our newsletter