TELEPORT IDENTITY GOVERNANCE
Identity Governance that Accelerates Engineers
Automate provisioning, approvals, access reviews, and continuous monitoring — purpose-built for engineering infrastructure at scale.
TRUSTED BY LEADERS


















THE MODERN IDENTITY GOVERNANCE CHALLENGE
Engineers need identity governance at infrastructure scale
Traditional identity governance tools weren’t built for modern engineering infrastructure.
They lack context about servers, clusters, databases, workloads, and developer workflows — creating gaps that attackers exploit and auditors flag.
Teleport Identity Governance
Bring identity governance directly to the engineering stack, unifying access, approval, identity lifecycle, and continuous monitoring across users, machines, agents, and cloud resources.
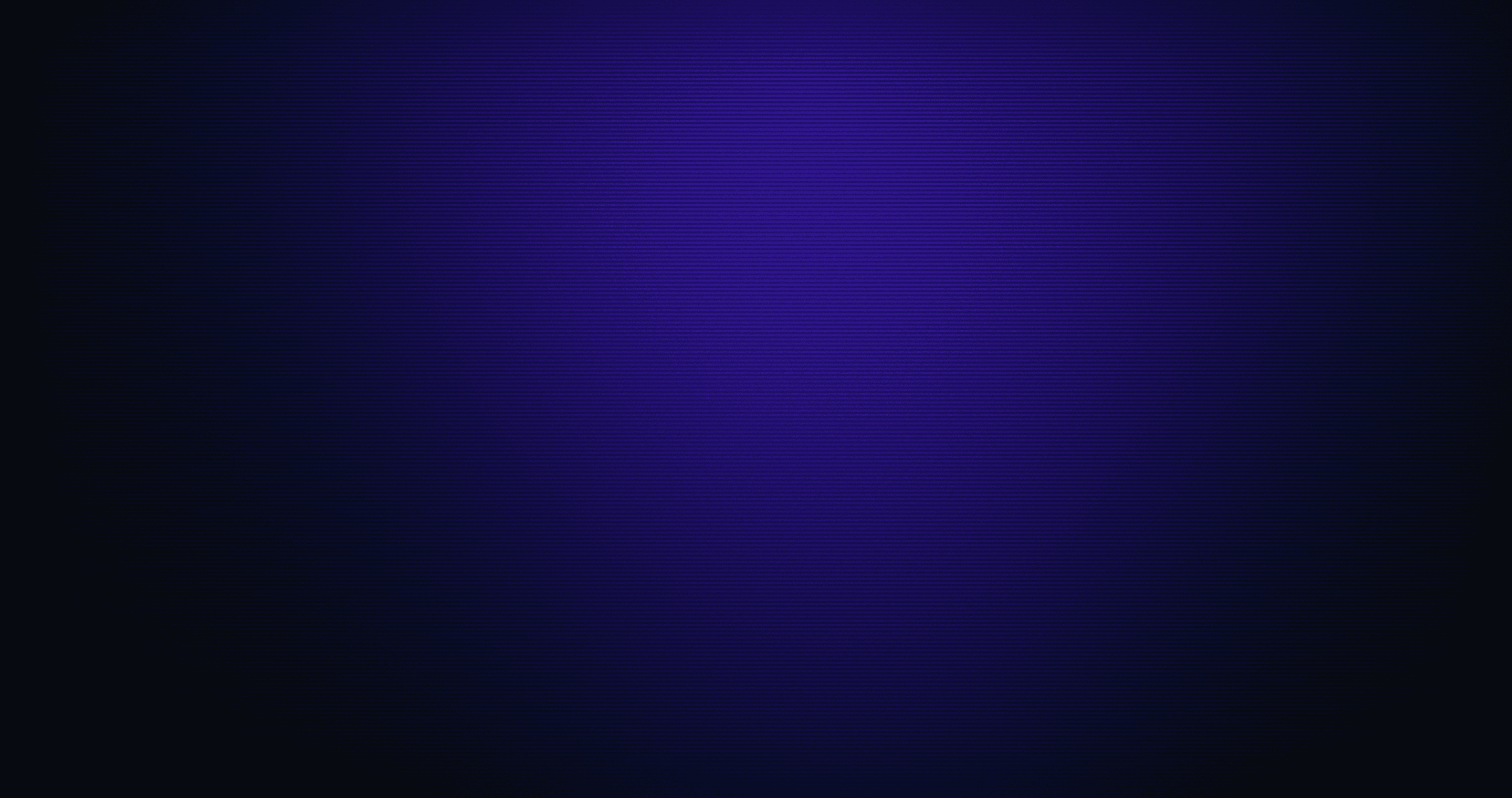
Teleport Identity Governance hardens identities and reduces administration complexity with:
Identity provider integrations
Just-in-time access requests
Access lists and reviews
Access monitoring and response
Trusted devices

Leverage existing identity provider workflows
Teleport integrates seamlessly with your identity providers using custom APIs and SCIM, ensuring users always have the right access at the right time.
Automatic provisioning when employees join or change teams
Instant de-provisioning when employees leave or transfer
Continuous compliance monitoring and alerts for violations
Approve only what’s needed with Just‑In‑Time Access Requests
Teleport eliminates always-on privileged access by issuing short-lived, just-in-time access that expires automatically. Collapse the attack surface by removing long-lived credentials and secrets sprawl.
Enforce least privilege while shortening access response time
Automate approvals using RBAC, ABAC, or contextual rules
Generate rich audit trails for every request and approval
Let engineers request access via familiar tools and CLIs

Reduce compliance workload with Access Lists & Reviews
Teleport automates the repetitive work of access reviews and makes them faster, clearer, and fully traceable.
Review and approve requests using Slack, PagerDuty, Teams, Jira, or ServiceNow
Assign reviewers or managers automatically
Enforce mandatory review cycles
Build custom review logic using APIs or the Go SDK
Integrate with AWS IAM Identity Center, GCP and Azure consoles for unified cloud governance

New Feature AI Access Reviews
Cut access review toil by 90%
AI inspection that automatically clusters, summarizes, and highlights unusual access patterns.

Enforce strong protection with Access Monitoring & Response
Purge unused or unsafe access automatically. Teleport continuously evaluates privileges and session behavior to ensure your policies stay enforced without depending on manual cleanup.
Detect overly broad or unused permissions
Identify sessions missing MFA or device trust
Send alerts for access violations
Automatically remove stale or risky access
Block untrusted devices and lock compromised identities
Teleport verifies device posture before granting access, blocking access from unmanaged or compromised endpoints. This stops attackers who steal laptops or clone disks.
Identity locking provides strong protection if an identity is compromised, instantly cutting off access across all infrastructure resources. This protects against threats like SSO bypass, session relay, token theft, MFA fatigue attacks, and account reactivation abuse.

Purpose-built for engineering teams
No more spreadsheets, manual access reviews, or privilege sprawl. Teleport brings identity governance directly into engineering infrastructure, giving teams:
Unified governance across all identity types
Identity + device + access context in every approval
Built-in Zero Trust enforcement
Engineering-native workflows
AI that reduces governance workload
Trusted by teams building critical infrastructure.
Teleport is a strategic technology partner as they help our joint customers to scale their AWS resources in a secure manner. With Teleport’s Identity-Native Infrastructure Access solution, DevOps Engineers get a frictionless experience managing infrastructure that doesn’t require secrets while implementing zero trust architecture in AWS.
We use Teleport Access Requests in combination with Auth0 to easily manage access to our infrastructure. Prior to Teleport, we manually managed SSH keys and a bastion machine and it was an organizational nightmare.
We used to go through multiple steps just to access cloud resources, and now it happens almost instantly. Our engineers are really happy with the significant improvement in their workflow.
Teleport’s vision for Infrastructure Identity is a game-changer for securing hybrid infrastructure.
Teleport is a strategic technology partner as they help our joint customers to scale their AWS resources in a secure manner. With Teleport’s Identity-Native Infrastructure Access solution, DevOps Engineers get a frictionless experience managing infrastructure that doesn’t require secrets while implementing zero trust architecture in AWS.
We use Teleport Access Requests in combination with Auth0 to easily manage access to our infrastructure. Prior to Teleport, we manually managed SSH keys and a bastion machine and it was an organizational nightmare.
We used to go through multiple steps just to access cloud resources, and now it happens almost instantly. Our engineers are really happy with the significant improvement in their workflow.
Teleport’s vision for Infrastructure Identity is a game-changer for securing hybrid infrastructure.
With Teleport, we were even able to close the Kubernetes API without losing access for our engineers or automation tools. That alone was a huge win.
Teleport allows us to comply with the regulatory hurdles that come with running an international stock exchange. The use of bastion hosts, integration with our identity service and auditing capabilities give us a compliant way to access our internal infrastructure.
The Infrastructure Identity solution from Teleport offers a glimpse into the future of more secure, more resilient, and higher-velocity enterprise computing.
Teleport has made obtaining a FedRAMP-Moderate ATO that much more achievable via their FIPS 140-2 endpoints, ease in integration with our SSO and MFA , and the view into audit logs of remote connection sessions provide the appropriate insight for Continuous Monitoring.
Over the many years of using Teleport, it's been an essential piece of my infrastructure to help secure access, and centralize my infrastructure into one dashboard, without having to jump around… I'm not sure how I could go without it.
With Teleport, we were even able to close the Kubernetes API without losing access for our engineers or automation tools. That alone was a huge win.
Teleport allows us to comply with the regulatory hurdles that come with running an international stock exchange. The use of bastion hosts, integration with our identity service and auditing capabilities give us a compliant way to access our internal infrastructure.
The Infrastructure Identity solution from Teleport offers a glimpse into the future of more secure, more resilient, and higher-velocity enterprise computing.
Teleport has made obtaining a FedRAMP-Moderate ATO that much more achievable via their FIPS 140-2 endpoints, ease in integration with our SSO and MFA , and the view into audit logs of remote connection sessions provide the appropriate insight for Continuous Monitoring.
Over the many years of using Teleport, it's been an essential piece of my infrastructure to help secure access, and centralize my infrastructure into one dashboard, without having to jump around… I'm not sure how I could go without it.
Ready to Teleport?
Additional Resources
Teleport Identity Governance
Discover how Teleport Identity Governance works, including key concepts, use cases, and more.
GoTo Secures and Simplifies Cloud Access with Teleport
Learn how GoTo’s engineering team used Teleport's just-in-time access model to improve security while reducing administrative overhead.
How Teleport Simplifies Just-in-Time (JIT) Access
Learn how to start automating approvals, enforcing least privilege, and ensuring all access is ephemeral and fully auditable.
Frequently Asked Questions
What is Teleport Identity Governance?
Teleport Identity Governance manages on-demand access, privileges, and compliance for infrastructure using Just-in-Time Access Requests, Access Lists, and policy-driven approvals.
How is Teleport different from traditional identity governance tools?
Unlike traditional IGA tools that focus narrowly on SaaS apps, Teleport’s governance features are built to govern access to infrastructure resources like servers, databases, Kubernetes, and cloud consoles (in addition to internal and web applications) via RBAC and Access Lists.
How does Teleport connect to Okta, AWS IAM Identity Center, Azure AD, or Entra ID?
Identity Governance integrations sync RBAC data with AWS IAM Identity Center, Microsoft Entra ID, and Okta while supporting SCIM-based integrations for systems like SailPoint.
What happens when someone changes roles or leaves?
When you use SCIM integrations, Teleport automatically creates, updates, and deletes users and Access List memberships based on changes in the upstream identity provider, including deprovisioning.











