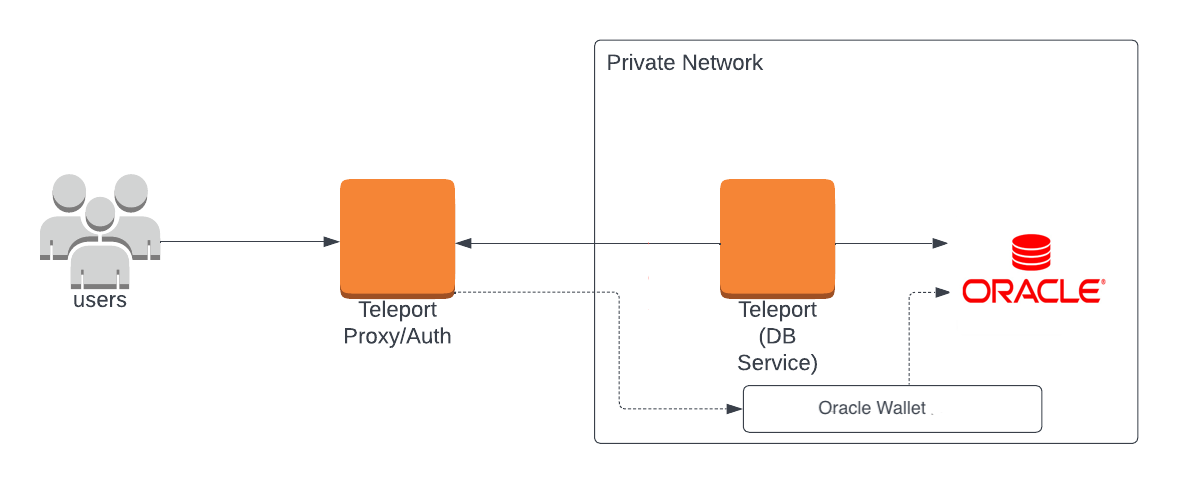
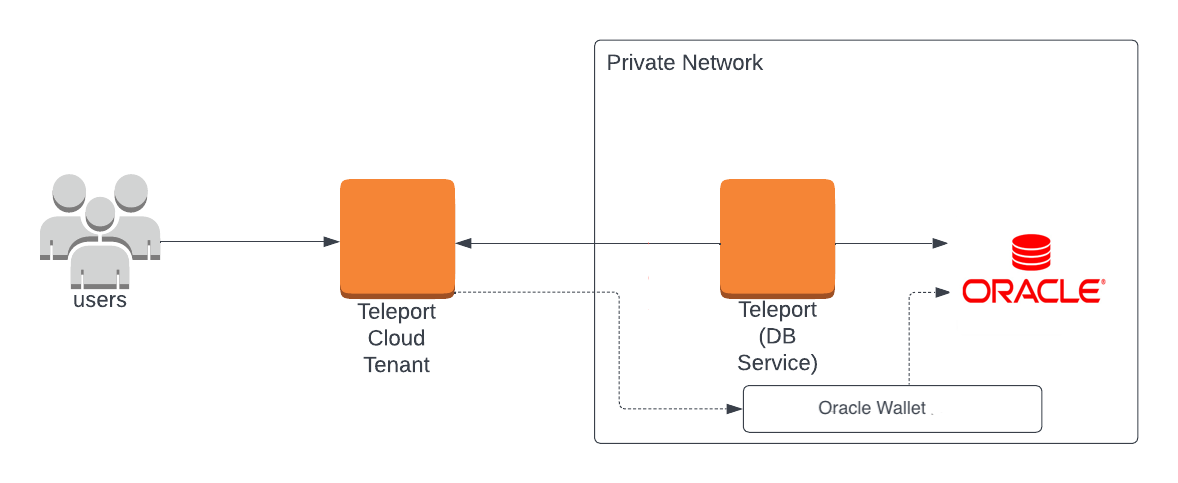
Database Access with Oracle
Teleport can provide secure access to Oracle via the Teleport Database Service. This allows for fine-grained access control through Teleport's RBAC.
In this guide, you will:
- Configure an Oracle with mutual TLS authentication.
- Join the Oracle database to your Teleport cluster.
- Connect to the Oracle database via the Teleport Database Service.
- Teleport Enterprise
- Teleport Enterprise Cloud
Prerequisites
- Self-Hosted Enterprise
- Teleport Enterprise Cloud
-
A running Teleport Enterprise cluster. For details on how to set this up, see the Enterprise Getting Started guide.
-
The Enterprise
tctladmin tool andtshclient tool version >= 14.3.33. You can download these tools by visiting your Teleport account. You can verify the tools you have installed by running the following commands:$ tctl version
# Teleport Enterprise v14.3.33 go1.21
$ tsh version
# Teleport v14.3.33 go1.21
-
A Teleport Enterprise Cloud account. If you do not have one, visit the signup page to begin a free trial of Teleport Team and upgrade to Teleport Enterprise Cloud.
-
The
tctladmin tool andtshclient tool version >= 16.4.3. To download these tools, visit the Installation page.$ tctl version
# Teleport Enterprise v16.4.3 go1.21
$ tsh version
# Teleport v16.4.3 go1.21
- Self-hosted Oracle server instance 18c or later.
- The
sqlclOracle client installed and added to your system'sPATHenvironment variable or any GUI client that supports JDBC Oracle thin client.
Step 1/6. Create a Teleport token and user
The Database Service requires a valid join token to join your Teleport cluster.
Run the following tctl command and save the token output in /tmp/token
on the server that will run the Database Service:
$ tctl tokens add --type=db --format=text
abcd123-insecure-do-not-use-this
To modify an existing user to provide access to the Database Service, see Database Access Access Controls
Create a local Teleport user with the built-in access and requester roles:
$ tctl users add \
--roles=access,requester \
--db-users=\* \
--db-names=\* \
alice
| Flag | Description |
|---|---|
--roles | List of roles to assign to the user. The builtin access role allows them to connect to any database server registered with Teleport. |
--db-users | List of database usernames the user will be allowed to use when connecting to the databases. A wildcard allows any user. |
--db-names | List of logical databases (aka schemas) the user will be allowed to connect to within a database server. A wildcard allows any database. |
Database names are only enforced for PostgreSQL and MongoDB databases.
For more detailed information about database access controls and how to restrict access see RBAC documentation.
Step 2/6. Create a certificate/key pair and Teleport Oracle Wallet
Teleport uses mutual TLS authentication with self-hosted databases. These databases must be configured with Teleport's certificate authority to be able to verify client certificates. They also need a certificate/key pair that Teleport can verify.
If you are using Teleport Cloud, your Teleport user must be allowed to
impersonate the system role Db in order to be able to generate the database
certificate.
Include the following allow rule in in your Teleport Cloud user's role:
allow:
impersonate:
users: ["Db"]
roles: ["Db"]
Follow the instructions below to generate TLS credentials for your database.
# Export Teleport's certificate authority and a generated certificate/key pair
# for host db.example.com with a 3-month validity period.
$ tctl auth sign --format=oracle --host=db.example.com --out=server --ttl=2190h
In this example, db.example.com is the hostname where the Teleport Database
Service can reach the Oracle server.
We recommend using a shorter TTL, but keep mind that you'll need to update the database server certificate before it expires to not lose the ability to connect. Pick the TTL value that best fits your use-case.
If tctl finds the Orapki tool in your local environment, the tctl auth sign --format=oracle --host=db.example.com --out=server --ttl=2190h command will produce an Oracle Wallet and
instructions how to configure the Oracle TCPS listener with Teleport Oracle Wallet. Otherwise the tctl auth sign --format=oracle command will produce a p12 certificate and instructions on how to create an Oracle Wallet on your Oracle Database instance.
If copying these files to your Oracle server, ensure the cert file permissions are readable by the oracle user.
Step 3/6. Configure Oracle Database
In order to enable the Teleport Oracle integration you will need to configure the TCPS Oracle listener and use the Teleport Oracle Wallet created in the previous step.
Align your listener.ora Oracle configuration file and add the following entries:
LISTENER =
(DESCRIPTION_LIST =
(DESCRIPTION =
(ADDRESS = (PROTOCOL = TCPS)(HOST = 0.0.0.0)(PORT = 2484))
)
)
WALLET_LOCATION = (SOURCE = (METHOD = FILE)(METHOD_DATA = (DIRECTORY = /path/to/oracleWalletDir)))
SSL_CLIENT_AUTHENTICATION = TRUE
Additionally, you will need to extend your sqlnet.ora Oracle configuration:
WALLET_LOCATION = (SOURCE = (METHOD = FILE)(METHOD_DATA = (DIRECTORY = /path/to/oracleWalletDir)))
SSL_CLIENT_AUTHENTICATION = TRUE
SQLNET.AUTHENTICATION_SERVICES = (TCPS)
You will need to reload Oracle Listener lsnrctl reload after updating the listener.ora configuration file.
Additionally, your Oracle Database user accounts must be configured to require a valid client certificate. If you're creating a new user:
CREATE USER alice IDENTIFIED EXTERNALLY AS 'CN=alice';
GRANT CREATE SESSION TO alice;
Step 4/6. Configure and Start the Database Service
Install and configure Teleport where you will run the Teleport Database Service:
- Linux Server
- Kubernetes Cluster
Use the appropriate commands for your environment to install your package:
- Enterprise
- Enterprise Cloud
- Debian 9+/Ubuntu 16.04+ (apt)
- Amazon Linux 2/RHEL 7 (yum)
- Amazon Linux 2/RHEL 7 (zypper)
- Amazon Linux 2023/RHEL 8+ (dnf)
- SLES 12 SP5+ and 15 SP5+ (zypper)
- Tarball
# Download Teleport's PGP public key
$ sudo curl https://apt.releases.teleport.dev/gpg \
-o /usr/share/keyrings/teleport-archive-keyring.asc
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport APT repository for v14. You'll need to update this
# file for each major release of Teleport.
$ echo "deb [signed-by=/usr/share/keyrings/teleport-archive-keyring.asc] \
https://apt.releases.teleport.dev/${ID?} ${VERSION_CODENAME?} stable/v14" \
| sudo tee /etc/apt/sources.list.d/teleport.list > /dev/null
$ sudo apt-get update
$ sudo apt-get install teleport-ent
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo apt-get install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for v14. You'll need to update this
# file for each major release of Teleport.
# First, get the major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
$ sudo yum install -y yum-utils
$ sudo yum-config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/v14/teleport.repo")"
$ sudo yum install teleport-ent
#
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo yum install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport Zypper repository for v14. You'll need to update this
# file for each major release of Teleport.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use zypper to add the teleport RPM repo
$ sudo zypper addrepo --refresh --repo $(rpm --eval "https://zypper.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-zypper.repo")
$ sudo yum install teleport-ent
#
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo yum install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for v14. You'll need to update this
# file for each major release of Teleport.
# First, get the major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use the dnf config manager plugin to add the teleport RPM repo
$ sudo dnf config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/v14/teleport.repo")"
# Install teleport
$ sudo dnf install teleport-ent
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo dnf install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport Zypper repository.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use Zypper to add the teleport RPM repo
$ sudo zypper addrepo --refresh --repo $(rpm --eval "https://zypper.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/v14/teleport-zypper.repo")
# Install teleport
$ sudo zypper install teleport-ent
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo zypper install teleport-ent-fips
In the example commands below, update $SYSTEM_ARCH with the appropriate
value (amd64, arm64, or arm). All example commands using this variable
will update after one is filled out.
$ curl https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz.sha256
# <checksum> <filename>
$ curl -O https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz
$ shasum -a 256 teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz
# Verify that the checksums match
$ tar -xvf teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz
$ cd teleport-ent
$ sudo ./install
For FedRAMP/FIPS-compliant installations of Teleport Enterprise, package URLs will be slightly different:
$ curl https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz.sha256
# <checksum> <filename>
$ curl -O https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz
$ shasum -a 256 teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz
# Verify that the checksums match
$ tar -xvf teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz
$ cd teleport-ent
$ sudo ./install
- Debian 9+/Ubuntu 16.04+ (apt)
- Amazon Linux 2/RHEL 7/CentOS 7 (yum)
- Amazon Linux 2023/RHEL 8+ (dnf)
- SLES 12 SP5+ and 15 SP5+ (zypper)
Add the Teleport repository to your repository list:
# Download Teleport's PGP public key
$ sudo curl https://apt.releases.teleport.dev/gpg \
-o /usr/share/keyrings/teleport-archive-keyring.asc
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport APT repository for cloud.
$ echo "deb [signed-by=/usr/share/keyrings/teleport-archive-keyring.asc] \
https://apt.releases.teleport.dev/${ID?} ${VERSION_CODENAME?} stable/cloud" \
| sudo tee /etc/apt/sources.list.d/teleport.list > /dev/null
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Update the repo and install Teleport and the Teleport updater
$ sudo apt-get update
$ sudo apt-get install "teleport-ent=$TELEPORT_VERSION" teleport-ent-updater
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for cloud.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
$ sudo yum install -y yum-utils
$ sudo yum-config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-yum.repo")"
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Install Teleport and the Teleport updater
$ sudo yum install "teleport-ent-$TELEPORT_VERSION" teleport-ent-updater
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for cloud.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use the dnf config manager plugin to add the teleport RPM repo
$ sudo dnf config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-yum.repo")"
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Install Teleport and the Teleport updater
$ sudo dnf install "teleport-ent-$TELEPORT_VERSION" teleport-ent-updater
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport Zypper repository for cloud.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use Zypper to add the teleport RPM repo
$ sudo zypper addrepo --refresh --repo $(rpm --eval "https://zypper.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-zypper.repo")
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Install Teleport and the Teleport updater
$ sudo zypper install "teleport-ent-$TELEPORT_VERSION" teleport-ent-updater
Is my Teleport instance compatible with Teleport Enterprise Cloud?
Before installing a teleport binary with a version besides v16,
read our compatibility rules to ensure that the binary is compatible with
Teleport Enterprise Cloud.
Teleport uses Semantic Versioning. Version numbers
include a major version, minor version, and patch version, separated by dots.
When running multiple teleport binaries within a cluster, the following rules
apply:
- Patch and minor versions are always compatible, for example, any 8.0.1 component will work with any 8.0.3 component and any 8.1.0 component will work with any 8.3.0 component.
- Servers support clients that are one major version behind, but do not support
clients that are on a newer major version. For example, an 8.x.x Proxy Service
instance is compatible with 7.x.x agents and 7.x.x
tsh, but we don't guarantee that a 9.x.x agent will work with an 8.x.x Proxy Service instance. This also means you must not attempt to upgrade from 6.x.x straight to 8.x.x. You must upgrade to 7.x.x first. - Proxy Service instances and agents do not support Auth Service instances that
are on an older major version, and will fail to connect to older Auth Service
instances by default. You can override version checks by passing
--skip-version-checkwhen starting agents and Proxy Service instances.
On the host where you will run the Teleport Database Service, start Teleport with the appropriate configuration.
Note that a single Teleport process can run multiple different services, for
example multiple Database Service agents as well as the SSH Service or Application
Service. The step below will overwrite an existing configuration file, so if
you're running multiple services add --output=stdout to print the config in
your terminal, and manually adjust /etc/teleport.yaml.
Generate a configuration file at /etc/teleport.yaml for the Database Service:
- Teleport Enterprise/Enterprise Cloud
- Teleport Community Edition
$ sudo teleport db configure create \
-o file \
--token=/tmp/token \
--proxy=teleport.example.com:443 \
--name=oracle \
--protocol=oracle \
--uri=oracle.example.com:2484 \
--labels=env=dev
$ sudo teleport db configure create \
-o file \
--token=/tmp/token \
--proxy=mytenant.teleport.sh:443 \
--name=oracle \
--protocol=oracle \
--uri=oracle.example.com:2484 \
--labels=env=dev
Configure the Teleport Database Service to start automatically when the host boots up by creating a systemd service for it. The instructions depend on how you installed the Teleport Database Service.
- Package Manager
- TAR Archive
On the host where you will run the Teleport Database Service, enable and start Teleport:
$ sudo systemctl enable teleport
$ sudo systemctl start teleport
On the host where you will run the Teleport Database Service, create a systemd service configuration for Teleport, enable the Teleport service, and start Teleport:
$ sudo teleport install systemd -o /etc/systemd/system/teleport.service
$ sudo systemctl enable teleport
$ sudo systemctl start teleport
You can check the status of the Teleport Database Service with systemctl status teleport
and view its logs with journalctl -fu teleport.
Teleport provides Helm charts for installing the Teleport Database Service in Kubernetes Clusters.
Set up the Teleport Helm repository.
Allow Helm to install charts that are hosted in the Teleport Helm repository:
$ helm repo add teleport https://charts.releases.teleport.dev
Update the cache of charts from the remote repository so you can upgrade to all available releases:
$ helm repo update
- Self-Hosted
- Cloud-Hosted
Install the Teleport Kube Agent into your Kubernetes Cluster with the Teleport Database Service configuration.
$ JOIN_TOKEN=$(cat /tmp/token)
$ helm install teleport-kube-agent teleport/teleport-kube-agent \
--create-namespace \
--namespace teleport-agent \
--set roles=db \
--set proxyAddr=teleport.example.com:443 \
--set authToken=${JOIN_TOKEN?} \
--set "databases[0].name=oracle" \
--set "databases[0].uri=oracle.example.com:2484" \
--set "databases[0].protocol=oracle" \
--set "databases[0].static_labels.env=dev" \
--version 14.3.33
Install the Teleport Kube Agent into your Kubernetes Cluster with the Teleport Database Service configuration.
$ JOIN_TOKEN=$(cat /tmp/token)
$ helm install teleport-kube-agent teleport/teleport-kube-agent \
--create-namespace \
--namespace teleport-agent \
--set roles=db \
--set proxyAddr=mytenant.teleport.sh:443 \
--set authToken=${JOIN_TOKEN?} \
--set "databases[0].name=oracle" \
--set "databases[0].uri=oracle.example.com:2484" \
--set "databases[0].protocol=oracle" \
--set "databases[0].static_labels.env=dev" \
--version 16.4.3
Make sure that the Teleport agent pod is running. You should see one
teleport-kube-agent pod with a single ready container:
$ kubectl -n teleport-agent get pods
NAME READY STATUS RESTARTS AGE
teleport-kube-agent-0 1/1 Running 0 32s
A single Teleport process can run multiple services, for example multiple Database Service instances as well as other services such the SSH Service or Application Service.
Step 5/6. (Optional) Configure Teleport to pull audit logs from Oracle Audit Trail
Teleport can pull audit logs from Oracle Audit Trail. In order to enable this feature, you will need to configure Oracle Audit Trail and create a dedicated Teleport user that will be used to fetch audit events from Oracle Audit Trail.
Create an internal Oracle teleport user that will fetch
audit events from Oracle Audit Trail:
CREATE USER teleport IDENTIFIED EXTERNALLY AS 'CN=teleport';
GRANT CREATE SESSION TO teleport;
GRANT SELECT ON dba_audit_trail TO teleport;
GRANT SELECT ON V_$SESSION TO teleport;
Enable the table in Oracle Audit Trail:
ALTER system SET audit_trail=db,extended scope=spfile;
Restart your Oracle instance to propagate audit trail changes.
Enable Oracle auditing for the alice user:
AUDIT ALL STATEMENTS by alice BY access;
You must enable auditing for each Teleport user that will be used to connect to Oracle. Additionally you can create a different audit policy for each user.
Configure the Teleport Database Service to pull audit logs from Oracle Audit Trail:
- Static config
- Dynamic resource
db_service:
enabled: "yes"
databases:
- name: "oracle"
protocol: "oracle"
uri: oracle.example.com:2484"
oracle:
audit_user: "teleport"
kind: db
version: v3
metadata:
name: oracle
spec:
protocol: "oracle"
uri: "oracle.example.com:2484"
oracle:
audit_user: "teleport"
Teleport doesn't clean up audit trail events from Oracle Audit Trail. Make sure to configure an Oracle Audit Trail cleanup policy to avoid running out of disk space.
Step 6/6. Connect
Once the Database Service has joined the cluster, log in to see the available databases:
$ tsh login --proxy=mytenant.teleport.sh --user=alice
$ tsh db ls
# Name Description Allowed Users Labels Connect
# ------ -------------- ------------- ------- -------
# oracle Oracle Example [*] env=dev
Connect to the database:
$ tsh db connect --db-user=alice --db-name=XE oracle
#
#
# SQLcl: Release 22.4 Production on Fri Mar 31 20:48:02 2023
#
# Copyright (c) 1982, 2023, Oracle. All rights reserved.
#
# Connected to:
# Oracle Database 21c Express Edition Release 21.0.0.0.0 - Production
# Version 21.3.0.0.0
#
# SQL>
To log out of the database and remove credentials:
# Remove credentials for a particular database instance.
$ tsh db logout oracle
# Remove credentials for all database instances.
$ tsh db logout
Next steps
- Learn how to restrict access to certain users and databases.
- Learn more about dynamic database registration.
- View the High Availability (HA) guide.
- See the YAML configuration reference for updating dynamic resource matchers or static database definitions.
- Take a look at the full CLI reference.
- Learn more about
sqlnet.oraandlistener.oraconfiguration from the Parameters for the sqlnet.ora File and Oracle Net Listener Parameters in the listener.ora File Oracle documentation. - Oracle Audit Trail