Installing Teleport
This guide shows you how to install Teleport binaries on your platform, including:
teleporttshtctltbot
If you are new to Teleport, we recommend following our getting started guide.
For best results, Teleport clients (tsh, tctl, tbot) should be the same major
version as the cluster they are connecting to. Teleport servers are compatible
with clients that are on the same major version or one major version older.
Teleport servers do not support clients that are on a newer major version.
See our Upgrading guide for more information.
Operating system support
Teleport is officially supported on the platforms listed below. It is worth noting that the open-source community has been successful in building and running Teleport on UNIX variants other than Linux [1].
| Operating System | teleport Daemon | tctl Admin Tool | tsh and Teleport Connect User Clients [2] | Web UI (via the browser) | tbot Daemon |
|---|---|---|---|---|---|
| Linux v2.6.23+ (RHEL/CentOS 7+, Amazon Linux 2+, Amazon Linux 2023+, Ubuntu 16.04+, Debian 9+, SLES 12 SP 5+, and SLES 15 SP 5+) [3] | yes | yes | yes | yes | yes |
| macOS v10.13+ (High Sierra) | yes | yes | yes | yes | yes |
| Windows 10+ (rev. 1607) [4] | no | no | yes | yes | no |
[1] Teleport is written in Go and many of these system requirements are due to the requirements of the Go toolchain.
[2] tsh is a Command Line Client (CLI) and Teleport Connect is a Graphical User Interface (GUI) desktop client. See
Using Teleport Connect for usage and installation.
[3] Enhanced Session Recording requires Linux kernel v5.8+.
[4] Teleport server does not run on Windows yet, but tsh and Teleport Connect (the Teleport desktop clients)
supports most features on Windows 10 and later.
Linux
All installations include teleport, tsh, tctl, and tbot.
Feature support
Some Teleport features have additional requirements:
| Feature | Requirement | Debian | Ubuntu | CentOS/RHEL | Amazon Linux | SLES |
|---|---|---|---|---|---|---|
| Enhanced Session Recording | Kernel v5.8+ | 11, or 10 with backports | 20.04.2+ | 9+ | 2 (post 11/2021), 2023 | 12 SP5, 15 SP5 |
| Automatic Updates | systemd-based | 9+ | 16.04+ | 7+ | 2, 2023 | 12 SP5, 15 SP5 |
| Installation through apt/yum/zypper repos | systemd-based | 9+ | 16.04+ | 7+ | 2, 2023 | 12 SP5, 15 SP5 |
apt, yum, and zypper repos don't expose packages for all distribution variants.
When following installation instructions, you might need to replace ID with
ID_LIKE to install packages of the closest supported distribution.
Currently supported distributions (and ID) are:
- RHEL >= 7 (
rhel) - CentOS >= 7 (
centos) - Debian >= 9 (
debian) - Ubuntu >= 16.04 (
ubuntu) - Amazon Linux 2 and 2023 (
amzn) - SLES >= 12 SP5, >= 15 SP5 (
sles)
Installation instructions
Best practices for production security
When running Teleport in production, you should adhere to the following best practices to avoid security incidents:
- Avoid using
sudoin production environments unless it's necessary. - Create new, non-root, users and use test instances for experimenting with Teleport.
- Run Teleport's services as a non-root user unless required. Only the SSH
Service requires root access. Note that you will need root permissions (or
the
CAP_NET_BIND_SERVICEcapability) to make Teleport listen on a port numbered <1024(e.g.443). - Follow the principle of least privilege. Don't give users
permissive roles when more a restrictive role will do.
For example, don't assign users the built-in
access,editorroles, which give them permissions to access and edit all cluster resources. Instead, define roles with the minimum required permissions for each user and configure access requests to provide temporary elevated permissions. - When you enroll Teleport resources—for example, new databases or applications—you
should save the invitation token to a file.
If you enter the token directly on the command line, a malicious user could view
it by running the
historycommand on a compromised system.
You should note that these practices aren't necessarily reflected in the examples used in documentation. Examples in the documentation are primarily intended for demonstration and for development environments.
Select an edition, then follow the instructions for that edition to install Teleport.
- Teleport Community Edition
- Teleport Enterprise
- Teleport Enterprise Cloud
The following command updates the repository for the package manager on the local operating system and installs the provided Teleport version:
$ curl https://cdn.teleport.dev/install-v14.3.33.sh | bash -s 14.3.33
- Debian 9+/Ubuntu 16.04+ (apt)
- Amazon Linux 2/RHEL 7 (yum)
- Amazon Linux 2/RHEL 7 (zypper)
- Amazon Linux 2023/RHEL 8+ (dnf)
- SLES 12 SP5+ and 15 SP5+ (zypper)
- Tarball
# Download Teleport's PGP public key
$ sudo curl https://apt.releases.teleport.dev/gpg \
-o /usr/share/keyrings/teleport-archive-keyring.asc
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport APT repository for v14. You'll need to update this
# file for each major release of Teleport.
$ echo "deb [signed-by=/usr/share/keyrings/teleport-archive-keyring.asc] \
https://apt.releases.teleport.dev/${ID?} ${VERSION_CODENAME?} stable/v14" \
| sudo tee /etc/apt/sources.list.d/teleport.list > /dev/null
$ sudo apt-get update
$ sudo apt-get install teleport-ent
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo apt-get install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for v14. You'll need to update this
# file for each major release of Teleport.
# First, get the major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
$ sudo yum install -y yum-utils
$ sudo yum-config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/v14/teleport.repo")"
$ sudo yum install teleport-ent
#
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo yum install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport Zypper repository for v14. You'll need to update this
# file for each major release of Teleport.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use zypper to add the teleport RPM repo
$ sudo zypper addrepo --refresh --repo $(rpm --eval "https://zypper.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-zypper.repo")
$ sudo yum install teleport-ent
#
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo yum install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for v14. You'll need to update this
# file for each major release of Teleport.
# First, get the major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use the dnf config manager plugin to add the teleport RPM repo
$ sudo dnf config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/v14/teleport.repo")"
# Install teleport
$ sudo dnf install teleport-ent
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo dnf install teleport-ent-fips
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport Zypper repository.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use Zypper to add the teleport RPM repo
$ sudo zypper addrepo --refresh --repo $(rpm --eval "https://zypper.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/v14/teleport-zypper.repo")
# Install teleport
$ sudo zypper install teleport-ent
For FedRAMP/FIPS-compliant installations, install the teleport-ent-fips package instead:
$ sudo zypper install teleport-ent-fips
In the example commands below, update $SYSTEM_ARCH with the appropriate
value (amd64, arm64, or arm). All example commands using this variable
will update after one is filled out.
$ curl https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz.sha256
# <checksum> <filename>
$ curl -O https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz
$ shasum -a 256 teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz
# Verify that the checksums match
$ tar -xvf teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-bin.tar.gz
$ cd teleport-ent
$ sudo ./install
For FedRAMP/FIPS-compliant installations of Teleport Enterprise, package URLs will be slightly different:
$ curl https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz.sha256
# <checksum> <filename>
$ curl -O https://cdn.teleport.dev/teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz
$ shasum -a 256 teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz
# Verify that the checksums match
$ tar -xvf teleport-ent-v14.3.33-linux-$SYSTEM_ARCH-fips-bin.tar.gz
$ cd teleport-ent
$ sudo ./install
OS repository channels
The following channels are available for APT, YUM, and Zypper repos. They may be used in place of
stable/v14 anywhere in the Teleport documentation.
| Channel name | Description |
|---|---|
stable/<major> | Receives releases for the specified major release line, i.e. v14 |
stable/cloud | Rolling channel that receives releases compatible with current Cloud version |
stable/rolling | Rolling channel that receives all published Teleport releases |
- Debian 9+/Ubuntu 16.04+ (apt)
- Amazon Linux 2/RHEL 7/CentOS 7 (yum)
- Amazon Linux 2023/RHEL 8+ (dnf)
- SLES 12 SP5+ and 15 SP5+ (zypper)
Add the Teleport repository to your repository list:
# Download Teleport's PGP public key
$ sudo curl https://apt.releases.teleport.dev/gpg \
-o /usr/share/keyrings/teleport-archive-keyring.asc
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport APT repository for cloud.
$ echo "deb [signed-by=/usr/share/keyrings/teleport-archive-keyring.asc] \
https://apt.releases.teleport.dev/${ID?} ${VERSION_CODENAME?} stable/cloud" \
| sudo tee /etc/apt/sources.list.d/teleport.list > /dev/null
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Update the repo and install Teleport and the Teleport updater
$ sudo apt-get update
$ sudo apt-get install "teleport-ent=$TELEPORT_VERSION" teleport-ent-updater
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for cloud.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
$ sudo yum install -y yum-utils
$ sudo yum-config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-yum.repo")"
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Install Teleport and the Teleport updater
$ sudo yum install "teleport-ent-$TELEPORT_VERSION" teleport-ent-updater
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport YUM repository for cloud.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use the dnf config manager plugin to add the teleport RPM repo
$ sudo dnf config-manager --add-repo "$(rpm --eval "https://yum.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-yum.repo")"
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Install Teleport and the Teleport updater
$ sudo dnf install "teleport-ent-$TELEPORT_VERSION" teleport-ent-updater
# Tip: Add /usr/local/bin to path used by sudo (so 'sudo tctl users add' will work as per the docs)
# echo "Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin:/usr/local/bin" > /etc/sudoers.d/secure_path
# Source variables about OS version
$ source /etc/os-release
# Add the Teleport Zypper repository for cloud.
# First, get the OS major version from $VERSION_ID so this fetches the correct
# package version.
$ VERSION_ID=$(echo $VERSION_ID | grep -Eo "^[0-9]+")
# Use Zypper to add the teleport RPM repo
$ sudo zypper addrepo --refresh --repo $(rpm --eval "https://zypper.releases.teleport.dev/$ID/$VERSION_ID/Teleport/%{_arch}/stable/cloud/teleport-zypper.repo")
# Provide your Teleport domain to query the latest compatible Teleport version
$ export TELEPORT_DOMAIN=example.teleport.com
$ export TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"
# Install Teleport and the Teleport updater
$ sudo zypper install "teleport-ent-$TELEPORT_VERSION" teleport-ent-updater
OS repository channels
The following channels are available for APT, YUM, and Zypper repos. They may be used in place of
stable/v14 anywhere in the Teleport documentation.
| Channel name | Description |
|---|---|
stable/<major> | Receives releases for the specified major release line, i.e. v14 |
stable/cloud | Rolling channel that receives releases compatible with current Cloud version |
stable/rolling | Rolling channel that receives all published Teleport releases |
Is my Teleport instance compatible with Teleport Enterprise Cloud?
Before installing a teleport binary with a version besides v16,
read our compatibility rules to ensure that the binary is compatible with
Teleport Enterprise Cloud.
Teleport uses Semantic Versioning. Version numbers
include a major version, minor version, and patch version, separated by dots.
When running multiple teleport binaries within a cluster, the following rules
apply:
- Patch and minor versions are always compatible, for example, any 8.0.1 component will work with any 8.0.3 component and any 8.1.0 component will work with any 8.3.0 component.
- Servers support clients that are one major version behind, but do not support
clients that are on a newer major version. For example, an 8.x.x Proxy Service
instance is compatible with 7.x.x agents and 7.x.x
tsh, but we don't guarantee that a 9.x.x agent will work with an 8.x.x Proxy Service instance. This also means you must not attempt to upgrade from 6.x.x straight to 8.x.x. You must upgrade to 7.x.x first. - Proxy Service instances and agents do not support Auth Service instances that
are on an older major version, and will fail to connect to older Auth Service
instances by default. You can override version checks by passing
--skip-version-checkwhen starting agents and Proxy Service instances.
- Teleport Community Edition
- Teleport Enterprise Cloud
Check the Downloads page for the most up-to-date information.
Check the Installation page for the most up-to-date information on obtaining Teleport binaries compatible with Teleport Cloud.
Docker
Images
We provide a pre-built Docker image for every version of Teleport. This section describes the available Docker images.
These images are hosted on Amazon ECR Public.
Image suffixes
For each of the image names listed in this section, you can specify attributes of the image by appending a suffix to the repository name or tag.
Images with the -distroless suffix within the repository name include only the
teleport binary and its runtime dependencies, with no shell or utility
applications. An example is public.ecr.aws/gravitational/teleport-distroless
for Teleport Community Edition.
Images with the *-distroless-debug suffix within the repository name include a
Busybox shell and tool suite in addition to Teleport, and are intended for
troubleshooting deployments only. They are not intended for production use. An
example is public.ecr.aws/gravitational/teleport-distroless-debug.
You can specify the architecture of an image by appending a suffix to its tag.
We support the following architecture suffixes: amd64, arm, and arm64. For
example, if you want to pull the ARM64 image for
public.ecr.aws/gravitational/teleport, you can use
public.ecr.aws/gravitational/teleport:14.3.33-arm64.
*-distroless and *-distroless-debug images support multiple architectures
natively, and do not require (or support) image suffixes. You can specify an
architecture using the --platform flag of docker pull to pull the arm,
arm64 or amd64 version of an image.
Version tags
Images point to a static version of Teleport. Use the image's tag to specify either:
- The major, minor, and patch version (e.g.,
14.3.33for the latest version of Teleport Community Edition). - The major version only, which implies the latest minor and patch numbers for
that major version. For example,
14implies14.3.33.
- Teleport Community Edition
- Teleport Enterprise
- Teleport Enterprise Cloud
| Image name | Troubleshooting Tools? | Image base |
|---|---|---|
public.ecr.aws/gravitational/teleport-distroless:14.3.33 | No | Distroless Debian 12 |
public.ecr.aws/gravitational/teleport-distroless-debug:14.3.33 | Yes | Distroless Debian 12 |
For testing, we always recommend that you use the latest release version of
Teleport, which is currently public.ecr.aws/gravitational/teleport-distroless:14.3.33.
Ubuntu 20.04-based images are available from our Legacy Amazon ECR Public repository. Their use is considered deprecated, and they may be removed in future releases.
| Image name | Includes troubleshooting tools | Image base |
|---|---|---|
public.ecr.aws/gravitational/teleport-ent-distroless:14.3.33 | No | Distroless Debian 12 |
public.ecr.aws/gravitational/teleport-ent-distroless-debug:14.3.33 | Yes | Distroless Debian 12 |
We also provide the following images for FIPS builds of Teleport Enterprise:
| Image name | Includes troubleshooting tools | Image base |
|---|---|---|
public.ecr.aws/gravitational/teleport-ent-fips-distroless:14.3.33 | No | Distroless Debian 12 |
public.ecr.aws/gravitational/teleport-ent-fips-distroless-debug:14.3.33 | Yes | Distroless Debian 12 |
For testing, we always recommend that you use the latest release version of
Teleport Enterprise, which is currently public.ecr.aws/gravitational/teleport-ent-distroless:14.3.33.
Ubuntu 20.04-based images for non-FIPS Teleport are available from our Legacy Amazon ECR Public repository.
| Image name | Includes troubleshooting tools | Image base |
|---|---|---|
public.ecr.aws/gravitational/teleport-ent-distroless:16.4.3 | No | Distroless Debian 12 |
public.ecr.aws/gravitational/teleport-ent-distroless-debug:16.4.3 | Yes | Distroless Debian 12 |
For testing, we always recommend that you use the latest Cloud release version of
Teleport Enterprise, which is currently public.ecr.aws/gravitational/teleport-ent-distroless:16.4.3.
Running Teleport on Docker
When running a container from one of the images listed above, consider the
container equivalent to running the teleport binary. The Teleport container
requires access to a file system and network ports.
Configuration
Teleport processes read their configuration from a local file path, which is
/etc/teleport.yaml by default. Make sure this file path is mounted to your
Teleport container.
Data directory
All Teleport processes read from and write to a data directory, which by default
is /var/lib/teleport. Make sure the data directory is mounted to your Teleport
container.
License file
If your Teleport Enterprise container runs the Auth Service, you will need to
give it access to a license file at the path named in the configuration, which
is /var/lib/teleport/license.pem by default. Make sure a license exists at
this location in the Teleport container's data directory.
Other file paths
Depending on the configuration settings you assign on your Teleport container, you will need to make sure that any file paths you name are mounted on the container.
For example, if you are running the Teleport Proxy Service on a container, you need to mount the directory containing TLS credentials to your Teleport container, then assign the following fields in the container's configuration file to the appropriate paths:
proxy_service:
https_keypairs:
- key_file: /my/path/key.pem
cert_file: /my/path/cert.pem
See the Teleport Configuration Reference for whether a field you would like to assign requires a file path.
Ports
A single Teleport process can run multiple services, each of which listens on a specific set of ports depending on your configuration. See our Networking Reference for the ports on your Teleport container to expose.
Extracting certificates from distroless images
Extracting certificates created with tctl auth sign from a container running
a distroless image can be tricky due to the absence of a shell and other OS tools.
Where possible you should log into the Teleport cluster using tsh and use
tctl auth sign locally to generate certificates. This way the action will be
logged against your Teleport user and be subject to all of the usual Teleport
RBAC policies in your cluster.
If this is not possible, use tctl auth sign --tar to collect all the files
generated by tctl auth sign into a tar archive, which is streamed directly
to stdout. The resulting certificates are never stored on the container
filesystem. You can either pipe this output directly to tar, or redirect it
to a local file for later use.
For example:
docker exec ${TELEPORT_CONTAINER} \
tctl auth sign --user alice --format tls -o alice.local --tar | tar xv
x alice.local.crt
x alice.local.key
x alice.local.cas
Example of running a Teleport container
In this example, we will show you how to run the Teleport Auth and Proxy Services on a local Docker container using Teleport Community Edition.
Since this container uses a self-signed certificate, we do not recommend using this configuration to protect any infrastructure outside your workstation. You can, however, join other local Docker containers to it using the token method.
First, create directories in your home directory to mount to the container. The Teleport container will write its configuration and data to these directories:
$ mkdir -p ~/teleport/config ~/teleport/data
Run teleport configure from the Teleport container to generate a configuration
file. This sets the container's name to localhost so your browser can trust
the Proxy Service's self-signed TLS certificate:
$ docker run --hostname localhost --rm \
--entrypoint=/usr/local/bin/teleport \
public.ecr.aws/gravitational/teleport-distroless:14.3.33 configure --roles=proxy,auth > ~/teleport/config/teleport.yaml
Start Teleport on your container:
$ docker run --hostname localhost --name teleport \
-v ~/teleport/config:/etc/teleport \
-v ~/teleport/data:/var/lib/teleport \
-p 3025:3025 -p 3080:3080 \
public.ecr.aws/gravitational/teleport-distroless:14.3.33
From there, open another terminal and make sure your Teleport container's web API is functioning as intended:
$ curl --insecure https://localhost:3080/webapi/ping
You should see JSON output similar to the following:
{
"auth": {
"type": "local",
"second_factor": "otp",
"preferred_local_mfa": "otp",
"local": {
"name": ""
},
"private_key_policy": "none",
"device_trust_disabled": true,
"has_motd": false
},
"proxy": {
"kube": {
"enabled": true,
"listen_addr": "0.0.0.0:3080"
},
"ssh": {
"listen_addr": "0.0.0.0:3080",
"tunnel_listen_addr": "0.0.0.0:3080",
"web_listen_addr": "0.0.0.0:3080"
},
"db": {
"postgres_listen_addr": "0.0.0.0:3080",
"mysql_listen_addr": "0.0.0.0:3080"
},
"tls_routing_enabled": true
},
"server_version": "12.1.5",
"min_client_version": "11.0.0",
"cluster_name": "localhost",
"automatic_upgrades": false
}
We are using the --insecure flag to trust Teleport's self-signed certificate.
In production, you will want to provision TLS credentials to the Proxy Service
from a trusted CA, e.g., Let's Encrypt.
Amazon EC2
We provide pre-built amd64 Amazon Linux 2023 based EC2 AMIs with Teleport
pre-installed.
These images are primarily intended for deploying a Teleport cluster using our reference Terraform code.
See the AWS Single-Instance Deployment and the Running Teleport Enterprise in High Availability mode on AWS using Terraform guide for detailed usage examples.
In order to use these AMIs outside of the reference Terraform, you can configure
the Teleport installation by setting configuration variables in the
/etc/teleport.d/conf file on the EC2 instance. See the Starter Cluster Configuration Template
for a list of the available configuration options.
The image names all include the build timestamp (shown as $TIMESTAMP in the table
below), and are tagged for easier searching.
| Image name | Edition | FIPS support | AMI Tags | Owner Account ID |
|---|---|---|---|---|
teleport-oss-14.3.33-$TIMESTAMP | OSS | No | TeleportVersion: 14.3.33, TeleportEdition: oss, TeleportFipsEnabled: false | 146628656107 |
teleport-ent-14.3.33-$TIMESTAMP | Enterprise | No | TeleportVersion: 14.3.33, TeleportEdition: ent, TeleportFipsEnabled: false | 146628656107 |
teleport-ent-14.3.33-fips-$TIMESTAMP | Enterprise | Yes | TeleportVersion: 14.3.33, TeleportEdition: ent, TeleportFipsEnabled: true | 146628656107 |
All images are based on Amazon Linux 2023 and have been hardened using the Amazon EC2 ImageBuilder STIG hardening component.
Teleport AMIs are automatically published to all non-opt-in AWS regions.
Helm
Set up the Teleport Helm repository.
Allow Helm to install charts that are hosted in the Teleport Helm repository:
$ helm repo add teleport https://charts.releases.teleport.dev
Update the cache of charts from the remote repository so you can upgrade to all available releases:
$ helm repo update
There are two charts available to install. Please see our guide for using each chart.
| Chart | Included Services | Values Reference |
|---|---|---|
teleport-cluster | Auth Service Proxy Service Other Teleport services if using a custom configuration | Reference |
teleport-kube-agent | Kubernetes Service Application Service Database Service | Reference |
macOS
- Community Edition
- Enterprise
- Enterprise Cloud
- Teleport package
- Homebrew
You can download one of the following .pkg installers for macOS:
| Link | Binaries |
|---|---|
teleport-14.3.33.pkg | teleporttctltshtbot |
tsh-14.3.33.pkg | tsh |
You can also fetch an installer via the command line:
$ curl -O https://cdn.teleport.dev/teleport-14.3.33.pkg
# Installs on Macintosh HD
$ sudo installer -pkg teleport-14.3.33.pkg -target /
# Password:
# installer: Package name is teleport-14.3.33
# installer: Upgrading at base path /
# installer: The upgrade was successful.
$ which teleport
# /usr/local/bin/teleport
The Teleport package in Homebrew is not maintained by Teleport and we can't guarantee its reliability or security.
Warnings
We recommend the use of our official Teleport packages. Binaries provided by Homebrew are not signed by Teleport, so features that require signed and notarized binaries (TouchID, Device Trust) are not available in Homebrew builds.
The tctl release available on Homebrew is the open source edition, and
cannot manage configuration resources unique to Teleport Enterprise and
Teleport Enterprise Cloud (e.g., OIDC and SAML connectors). For Teleport
Enterprise and Enterprise Cloud, we recommend installing the official Teleport
Enterprise edition of tctl.
Installing Teleport with Homebrew
To install Teleport with Homebrew, run the following command:
$ brew install teleport
If you choose to use Homebrew, you must verify that the versions of tsh
and tctl you run on your local machine are compatible with the versions
you run on your infrastructure. Homebrew usually ships the latest release of
Teleport, which may be incompatible with older versions. See our
compatibility policy for details.
To verify versions, log in to your cluster and compare the output of tctl status
against tsh version and tctl version.
You can download one of the following .pkg installers for macOS:
| Link | Binaries |
|---|---|
teleport-ent-14.3.33.pkg | teleporttctltshtbot |
tsh-14.3.33.pkg | tsh |
You can also fetch an installer from the command line:
$ curl -O https://cdn.teleport.dev/teleport-ent-14.3.33.pkg
# Install on Macintosh HD
$ sudo installer -pkg teleport-ent-14.3.33.pkg -target /
Password:
installer: Package name is teleport-ent-14.3.33
installer: Upgrading at base path /
installer: The upgrade was successful.
$ which teleport
/usr/local/bin/teleport
You can download one of the following .pkg installers for macOS:
| Link | Binaries |
|---|---|
teleport-ent-16.4.3.pkg | teleporttctltshtbot |
tsh-16.4.3.pkg | tsh |
You can also fetch an installer from the command line:
$ curl -O https://cdn.teleport.dev/teleport-ent-16.4.3.pkg
# Install on Macintosh HD
$ sudo installer -pkg teleport-ent-16.4.3.pkg -target /
Password:
installer: Package name is teleport-ent-16.4.3
installer: Upgrading at base path /
installer: The upgrade was successful.
$ which teleport
/usr/local/bin/teleport
Windows (tsh client only)
Most tsh features are supported for Windows 10 1607+. The tsh ssh command
can be run under cmd.exe, PowerShell, and Windows Terminal.
To install tsh on Windows, run the following commands in PowerShell (these commands will not work in cmd.exe):
- Teleport Community Edition
- Teleport Enterprise
- Teleport Enterprise Cloud
# Set the TLS level to TLS 1.2 (required on Windows Server 2016 and lower)
$ [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
# Get the expected checksum for the Windows tsh package
$ $Resp = Invoke-WebRequest https://cdn.teleport.dev/teleport-v14.3.33-windows-amd64-bin.zip.sha256
# PowerShell will return the binary representation of the response content
# by default, so you need to convert it to a string
$ [System.Text.Encoding]::UTF8.getstring($Resp.Content)
# <checksum> <filename>
$ Invoke-WebRequest -OutFile teleport-v14.3.33-windows-amd64-bin.zip -Uri https://cdn.teleport.dev/teleport-v14.3.33-windows-amd64-bin.zip
$ certUtil -hashfile teleport-v14.3.33-windows-amd64-bin.zip SHA256
# SHA256 hash of teleport-v14.3.33-windows-amd64-bin.zip:
# <checksum>
# CertUtil: -hashfile command completed successfully.
After you have verified that the checksums match, you can extract the archive.
The executable will be available at
teleport-v14.3.33-windows-amd64-bin\tsh.exe.
$ Expand-Archive teleport-v14.3.33-windows-amd64-bin.zip
$ cd teleport-v14.3.33-windows-amd64-bin
$ .\tsh.exe version
Teleport v14.3.33 git:v14.3.33 go1.21
Make sure to move tsh.exe into your PATH.
Do not place tsh.exe in the System32 directory, as this can cause issues when using WinSCP.
You should use %SystemRoot% (e.g. C:\Windows) instead, which is already included in %PATH%.
If you do not have administrator rights on the Windows system you're using, you can use %USERPROFILE%
(e.g. C:\Users\<username>) instead - but note that you will not be able to run tsh commands globally
from the command line unless you are in the same directory as tsh.exe.
# Set the TLS level to TLS 1.2 (required on Windows Server 2016 and lower)
$ [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
# Get the expected checksum for the Windows tsh package
$ $Resp = Invoke-WebRequest https://cdn.teleport.dev/teleport-v14.3.33-windows-amd64-bin.zip.sha256
# PowerShell will return the binary representation of the response content
# by default, so you need to convert it to a string
$ [System.Text.Encoding]::UTF8.getstring($Resp.Content)
# <checksum> <filename>
$ Invoke-WebRequest -OutFile teleport-v14.3.33-windows-amd64-bin.zip -Uri https://cdn.teleport.dev/teleport-v14.3.33-windows-amd64-bin.zip
$ certUtil -hashfile teleport-v14.3.33-windows-amd64-bin.zip SHA256
# SHA256 hash of teleport-v14.3.33-windows-amd64-bin.zip:
# <checksum>
# CertUtil: -hashfile command completed successfully.
After you have verified that the checksums match, you can extract the archive.
The executable will be available at
teleport-v14.3.33-windows-amd64-bin\tsh.exe.
$ Expand-Archive teleport-v14.3.33-windows-amd64-bin.zip
$ cd teleport-v14.3.33-windows-amd64-bin
$ .\tsh.exe version
Teleport v14.3.33 git:v14.3.33 go1.21
Make sure to move tsh.exe into your PATH.
Do not place tsh.exe in the System32 directory, as this can cause issues when using WinSCP.
You should use %SystemRoot% (e.g. C:\Windows) instead, which is already included in %PATH%.
If you do not have administrator rights on the Windows system you're using, you can use %USERPROFILE%
(e.g. C:\Users\<username>) instead - but note that you will not be able to run tsh commands globally
from the command line unless you are in the same directory as tsh.exe.
# Set the TLS level to TLS 1.2 (required on Windows Server 2016 and lower)
$ [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
# Get the expected checksum for the Windows tsh package
$ $Resp = Invoke-WebRequest https://cdn.teleport.dev/teleport-v16.4.3-windows-amd64-bin.zip.sha256
# PowerShell will return the binary representation of the response content
# by default, so you need to convert it to a string
$ [System.Text.Encoding]::UTF8.getstring($Resp.Content)
# <checksum> <filename>
$ Invoke-WebRequest -OutFile teleport-v16.4.3-windows-amd64-bin.zip -Uri https://cdn.teleport.dev/teleport-v16.4.3-windows-amd64-bin.zip
$ certUtil -hashfile teleport-v16.4.3-windows-amd64-bin.zip SHA256
# SHA256 hash of teleport-v16.4.3-windows-amd64-bin.zip:
# <checksum>
# CertUtil: -hashfile command completed successfully.
After you have verified that the checksums match, you can extract the archive.
The executable will be available at
teleport-v16.4.3-windows-amd64-bin\tsh.exe.
$ Expand-Archive teleport-v16.4.3-windows-amd64-bin.zip
$ cd teleport-v16.4.3-windows-amd64-bin
$ .\tsh.exe version
Teleport v16.4.3 git:v16.4.3 go1.21
Make sure to move tsh.exe into your PATH.
Do not place tsh.exe in the System32 directory, as this can cause issues when using WinSCP.
You should use %SystemRoot% (e.g. C:\Windows) instead, which is already included in %PATH%.
If you do not have administrator rights on the Windows system you're using, you can use %USERPROFILE%
(e.g. C:\Users\<username>) instead - but note that you will not be able to run tsh commands globally
from the command line unless you are in the same directory as tsh.exe.
Building from source
Teleport is written in Go, and currently requires go v1.21 or newer. Detailed instructions for building from source are available in the README.
Checksums
If you want to verify the integrity of a Teleport binary, SHA256 checksums are available for all downloads on our downloads page.
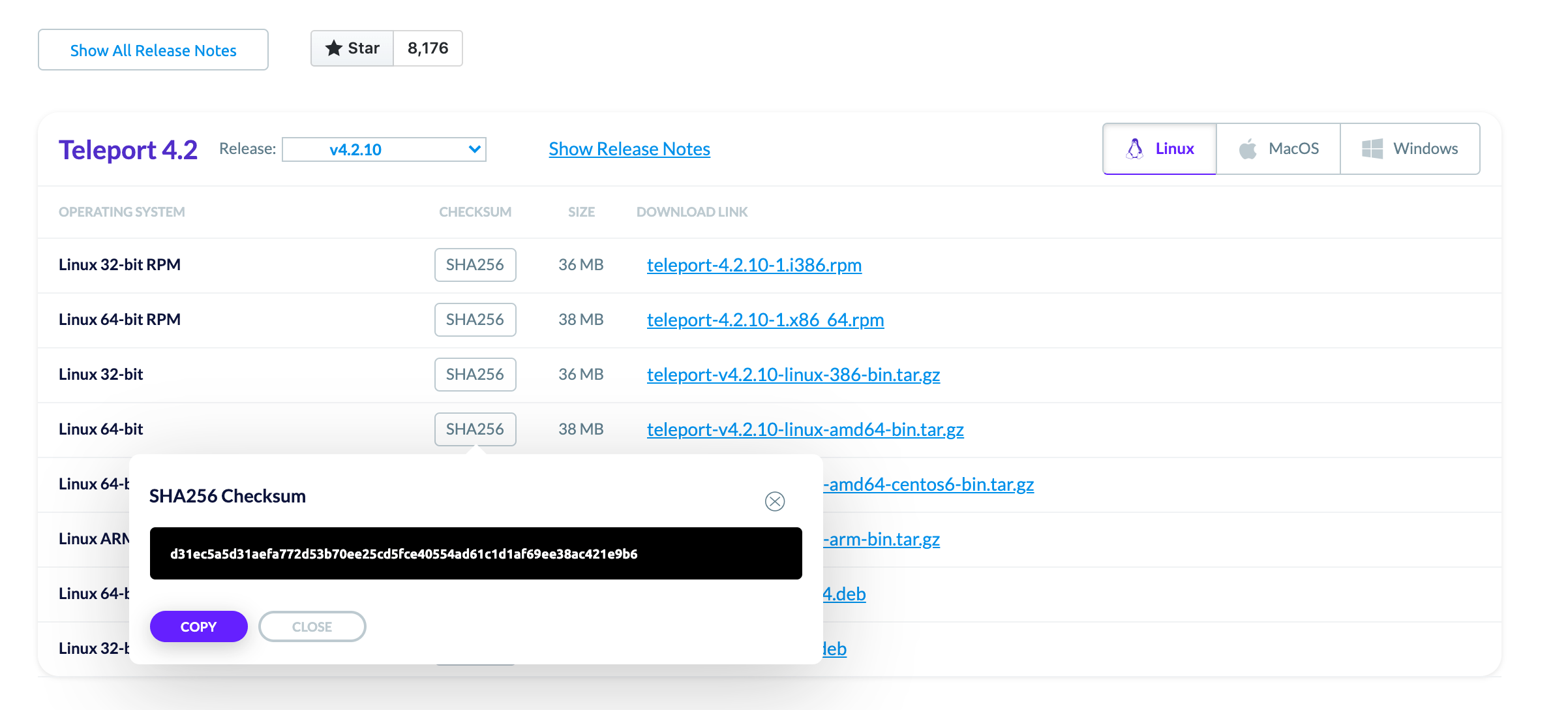
If you download Teleport via an automated system, you can programmatically
obtain the checksum by adding .sha256 to the download link. This is the method
shown in the installation examples.
$ export version=v14.3.33
# 'darwin' 'linux' or 'windows'
$ export os=linux
# '386' 'arm' on linux or 'amd64' for all distros
$ export arch=amd64
$ curl https://cdn.teleport.dev/teleport-$version-$os-$arch-bin.tar.gz.sha256
# <checksum> <filename>
Uninstalling Teleport
If you wish to uninstall Teleport at any time, see our documentation on Uninstalling Teleport.
Next steps
Now that you know how to install Teleport, you can enable access to all of your infrastructure. Get started with: