Home - Teleport Blog - Teleport 16
Teleport 16
It’s that time again — for a brand new major release. Our team releases major versions of Teleport every 4 months. Here we introduce Teleport 16. This post goes into detail about Teleport 16 breaking changes, bug fixes and improvements.
In Teleport 16, we focused on new features and enhancements to enable our customers to implement mitigations to protect against an IdP Compromise.
And as with every release, we listened to you — our customers — on suggestions for improvements and have incorporated many of those in Teleport 16.
The changes in Teleport 16 can be summarized as follows:
- Defending against IdP Compromise - Additional security layers to harden Teleport deployments and protect applications and services in case of IdP compromise.
- Usability - Improved usability for teams using Teleport at scale.
Each major Teleport release introduces breaking changes. We try to not gracefully break deployments, but below are two larger breaking changes that we wanted to highlight.
Breaking change for Community Users License Update:
We have been offering the stable releases of the Teleport Community Edition binaries and images distributed under the permissive Apache 2.0 license. Starting with the June release of Teleport 16, we are switching Teleport Community Edition to a commercial license with new restrictions:
- Individuals are free to use Teleport Community Edition for personal and hobby use with no restrictions.
- Companies may use Teleport Community Edition on the condition they have less than 100 employees and less than $10MM in annual revenue (AR).
- Companies cannot resell or embed Teleport Community Edition in their products or services.
- Companies larger than 100 employees or more than $10MM AR need to contact our sales team to evaluate and use Teleport.
- We will stop distributing compiled binaries, container images, and Amazon Machine Images (AMIs) under Apache 2.0 starting with Teleport 16. We will switch the license of those assets to the commercial license of Teleport Community Edition.
- We will continue to support previous versions according to our published schedule. Additionally, we will maintain the Apache 2.0 license for Community Edition binaries, containers, and images for Teleport Community Edition versions prior to Teleport 16.
You can learn more about these restrictions and reasons behind the change from our March 2024 blog post.
Breaking change for Self-Hosted Enterprise Users:
Teleport 16 has introduced license file validation on startup. If you’ve been using Teleport self-hosted for over a year, you’ll need to obtain an updated license. Here’s a step-by-step guide to update your license file.
This change only applies to customers running Teleport Enterprise Self-Hosted. No action is required for customers running Teleport Enterprise Cloud or Teleport Community Edition.
New Teleport 16 features
Teleport 16 brings the following new features and improvements:
- Teleport Identity
- Device Trust for the Web UI
- Per-session Phishing-Resistant MFA for applications
- Access requests from the resources view
- Teleport Access
- Teleport VNet
kubectl execfrom the Web UI- SSH multiplexer
- Teleport Policy
- Updated UI
- Okta Support
- Teleport Platform
- Web UI notification system
tctlfor Windows- Teleport plugin improvements
- Multi-region deployment blueprint
Teleport Identity
Device Trust for Teleport Web UI
Theme: Defending against IdP Compromise
Teleport Device Trust can now be enforced for browser-based workflows for both Teleport Desktop Access and web application access. The Teleport Connect client must be installed in order to satisfy device locality checks.
Per-session Phishing-Resistant MFA for Applications
Theme: Defending against IdP Compromise
Teleport 16 introduces "Phishing-Resistant MFA for Applications", an optional check that requires users to present an MFA token when starting a new session to access web and TCP applications. This feature addresses the challenges organizations face in securing access to critical applications, particularly when relying solely on single-factor authentication methods.
By implementing Phishing-Resistant MFA, organizations can significantly enhance the security of their sensitive applications. Teleport 16 allows organizations to enforce the use of company-issued hardware tokens, specify allowed token types, and customize MFA requirements on a per-cluster or per-user basis.
Access requests from the resources view
Theme: Improved Usability
The Teleport Access resources view in the Web UI now shows both resources you currently have access to and resources you can request access to. This allows users to request access to resources without navigating to a separate page.
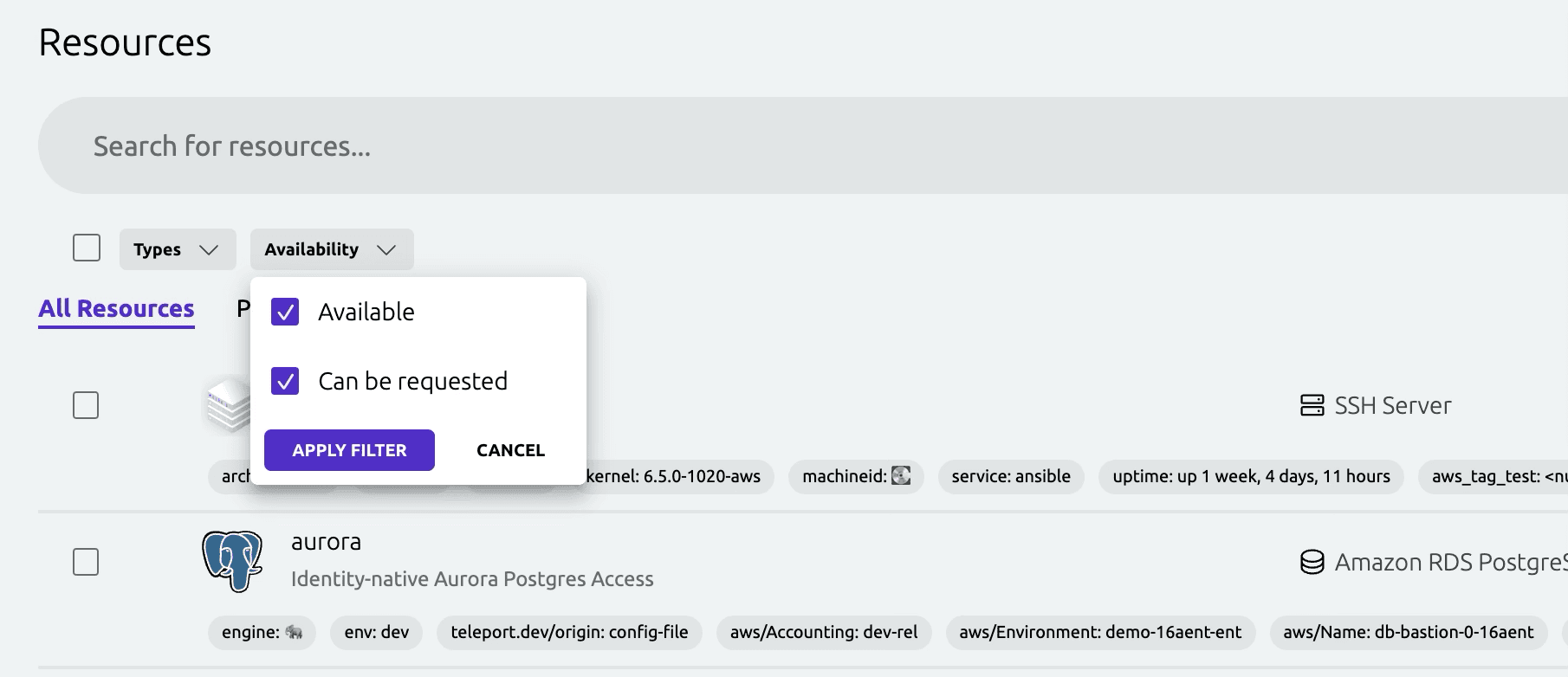
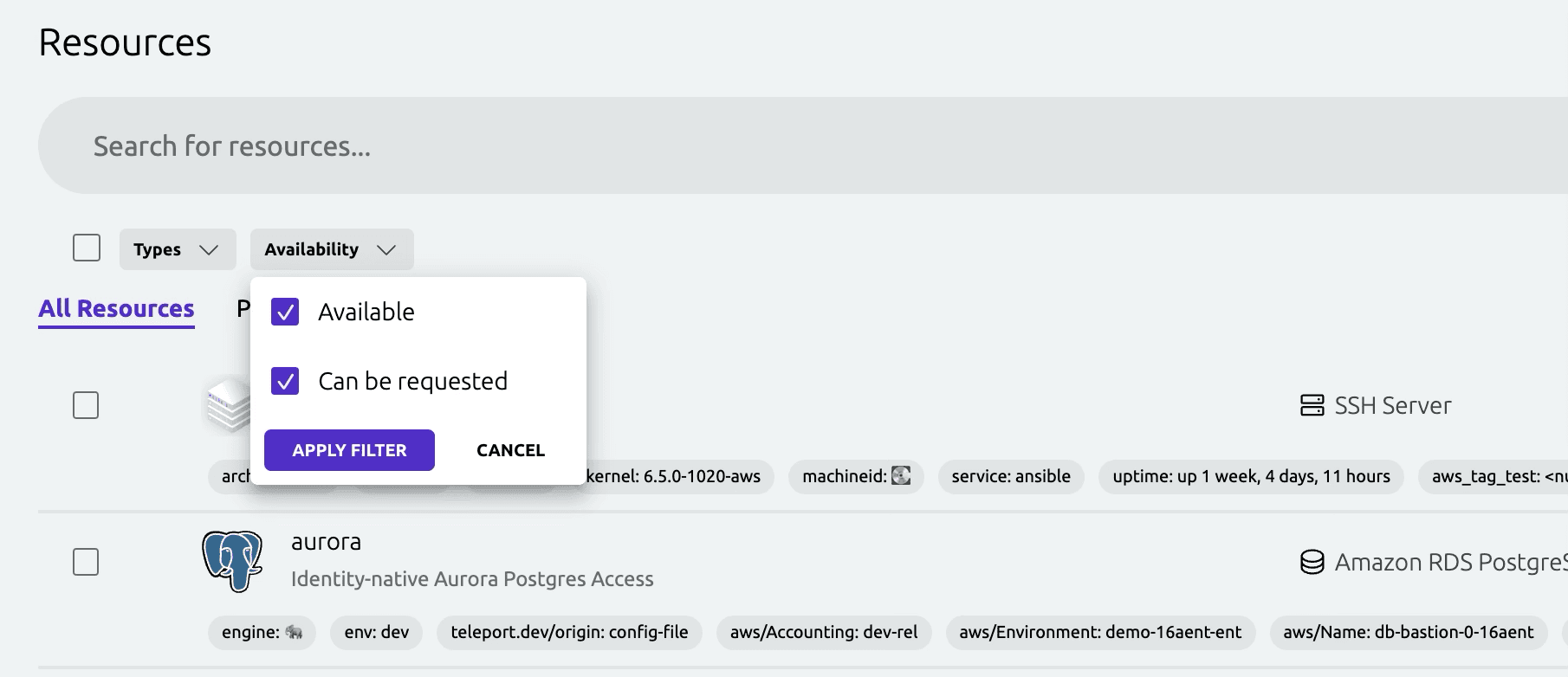
Cluster administrators who prefer the previous behavior of hiding requestable resources from the main view can set show_resources: accessible_only in their UI config. Learn more about configuring the UI.
Teleport Access
Teleport VNet
Theme: Defending against IdP Compromise
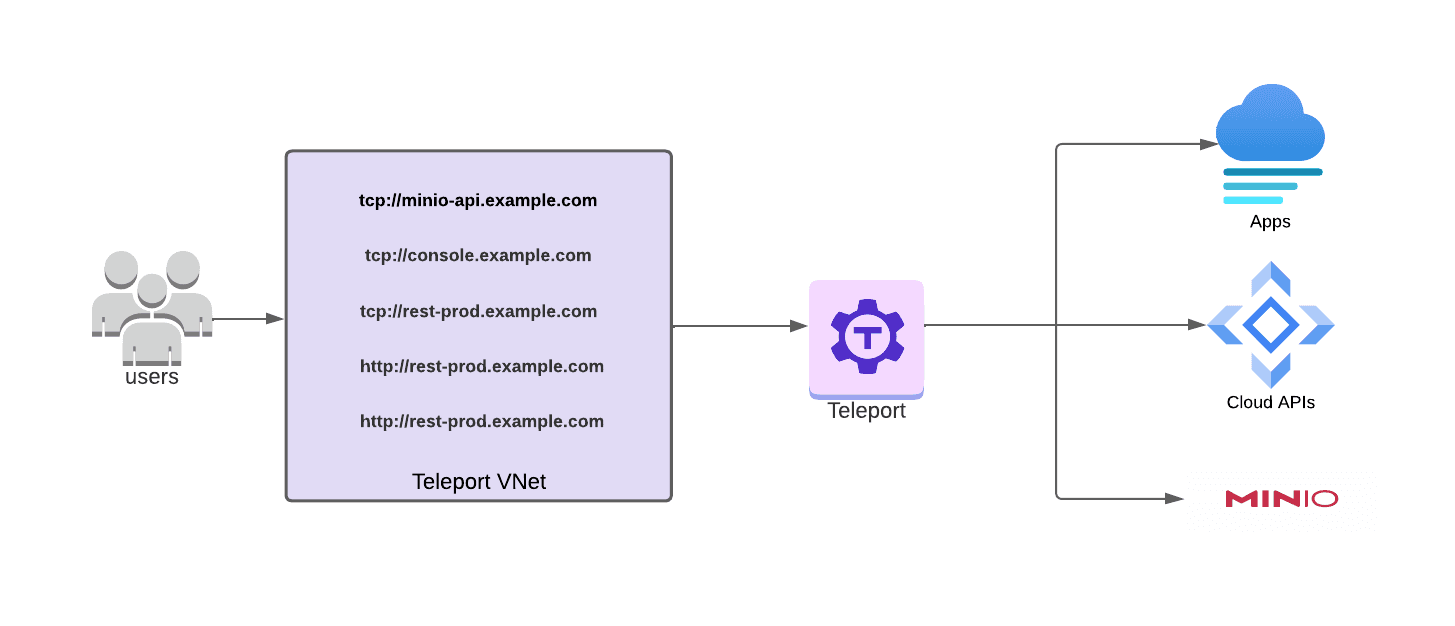
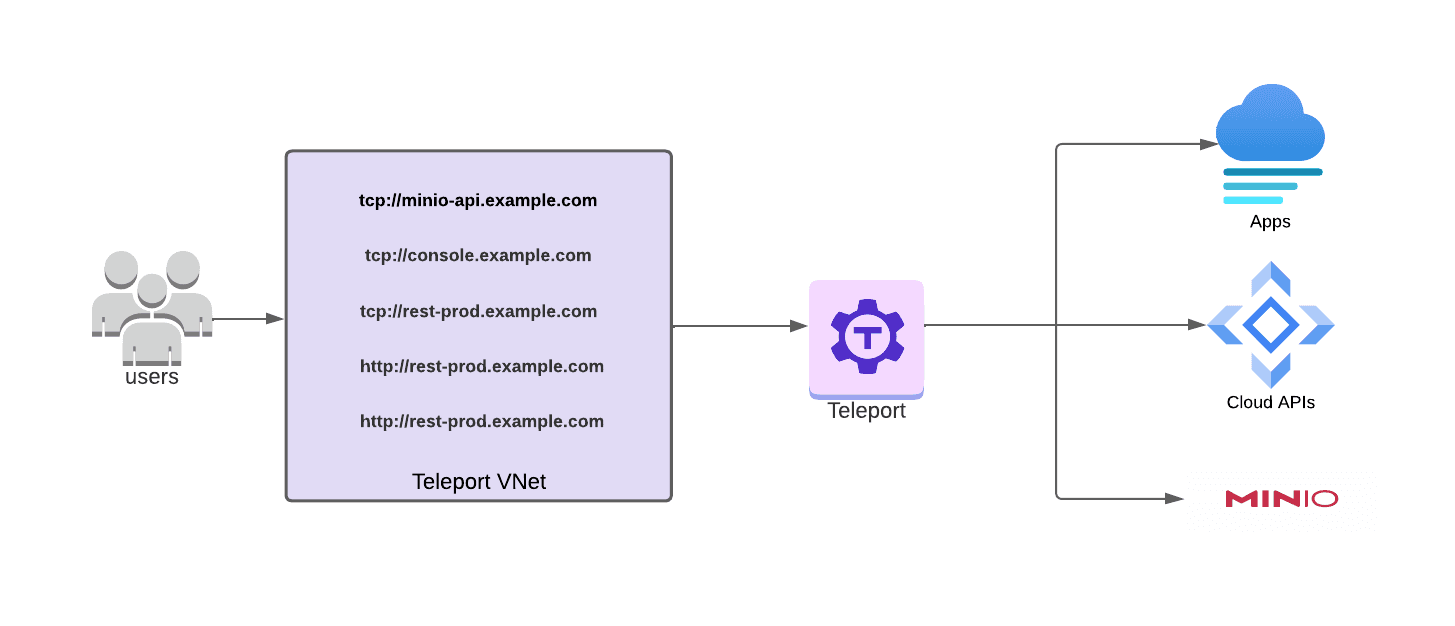
Teleport VNet enables teams eliminate VPNs, while maintaining a VPN-like experience for TCP-based applications. Teleport VNET is perfect for protecting non HTTP/HTTPS applications, and allows teams to connect to applications using regular-old DNS addresses.
Teleport VNet provides a virtual IP subnet and DNS server which automatically proxies connections to TCP apps in Teleport. Teleport VNet is designed to enhance the user experience for accessing applications with non-browser clients by creating a seamless, VPN-like environment where applications are accessible through their DNS names without manual configuration.
This allows local scripts and software applications to connect to any Teleport-protected TCP application as if they were connected to a VPN, without the need to manage local tunnels. Teleport VNet is powered by the Teleport Connect client and is available for macOS. Support for other operating systems will come in a future release. Read more about connecting your client or learn more via the VNet RFD.
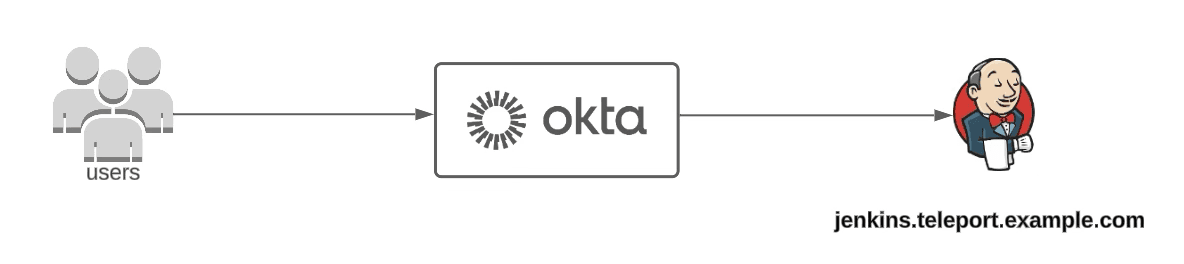
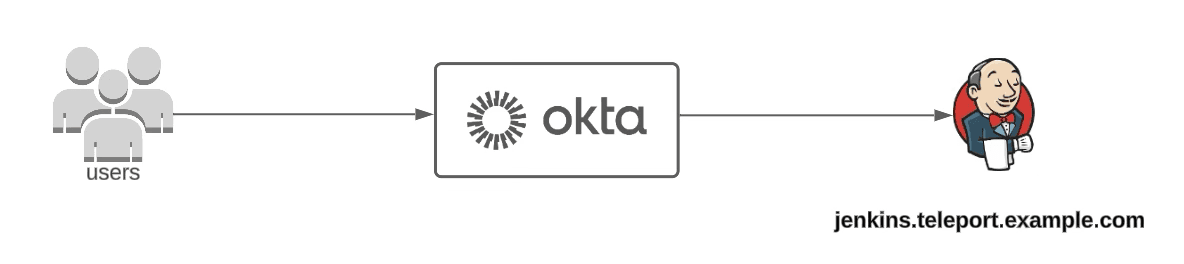
Teleport VNet Jenkins - BEFORE:
In the first example, we have a team that has Jenkins deployment within their environment, accessible via Okta. Jenkins already has TLS certs, and is running smoothly.
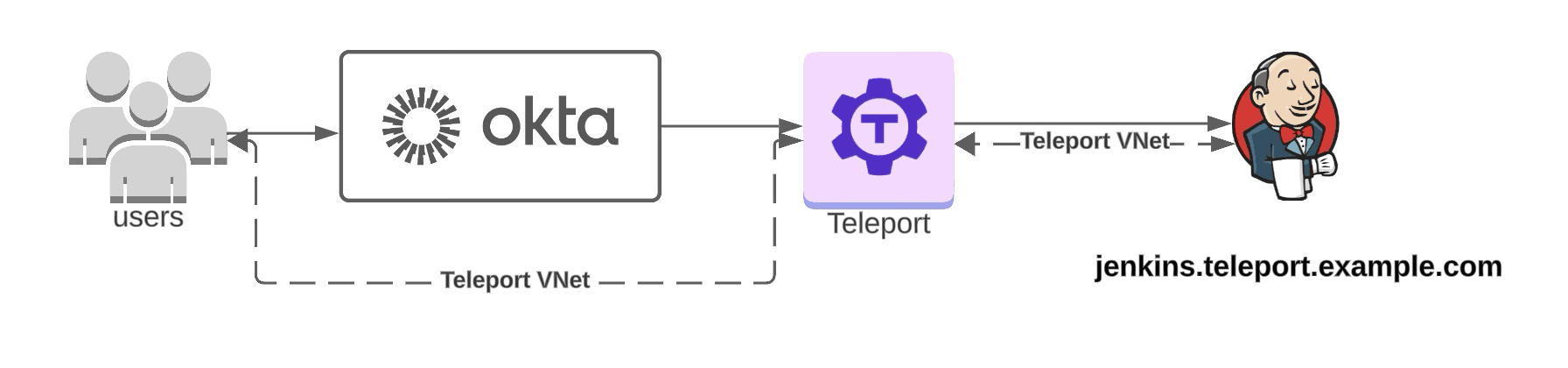
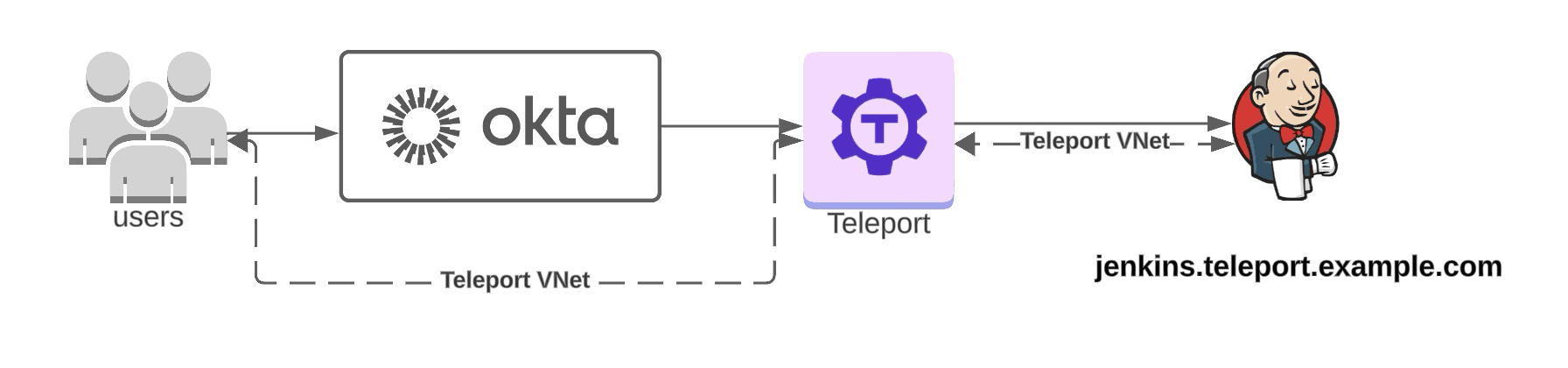
Teleport VNet Jenkins - AFTER:
After Teleport VNet, Jenkins is now only accessible to Teleport Users via VNet, with additional optional required MFA & Device Trust. No extra changes to either Okta or the Jenkins Config are required. Teams can still access the app via jenkins.teleport.example.com but only after they connect via Teleport VNet.
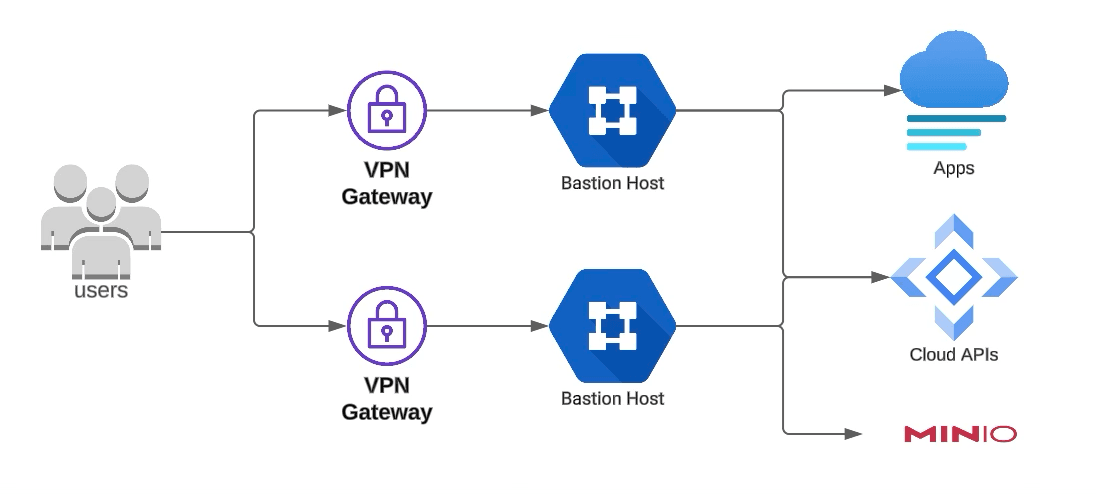
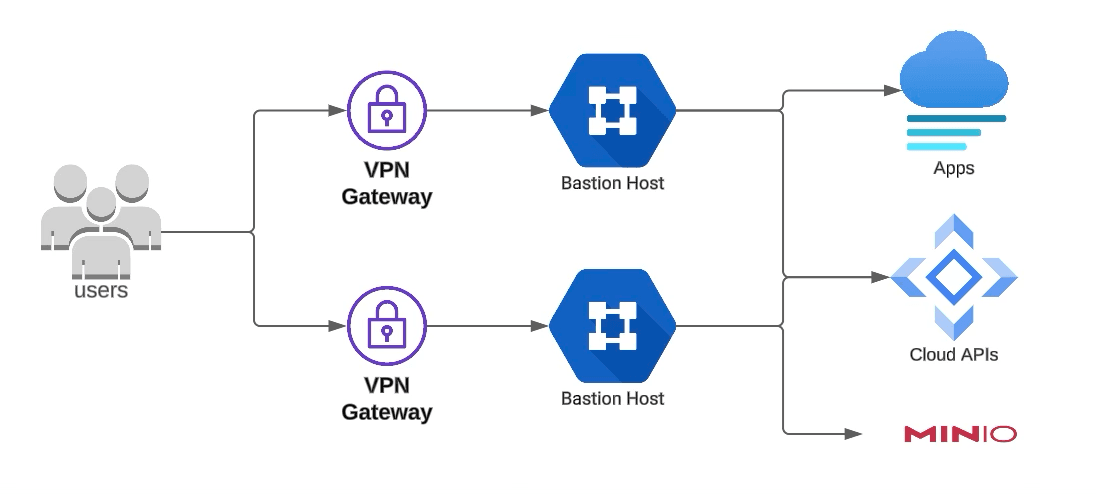
Teleport VNet MinIO - BEFORE:
Example of connecting to other TCP Apps, such as MinIO, a High-Performance Object Storage system. Prior to VNet, teams would need to use a VPN, or open up the firewall to dedicated location.
Teleport VNet MinIO - After:
Once a user has turned on VNet via Teleport Connect, they can access the console and API without the need for extra tunnels. Developers' local CLI tools and scripts can then natively communicate with those endpoints.
Teleport VNet Demo
Kubectl Exec from the Web UI
Theme: Improved Usability
Teleport 16 introduces the ability to run kubectl exec commands from the Teleport Web UI. This feature allows users to interact with Kubernetes pods directly from the Web UI, eliminating the need to switch between the Web UI and a terminal window.
SSH Multiplexer
Theme: Improved Usability
Teleport 16 includes a new high-performance SSH multiplexer. This is designed for use-cases which create a large number of SSH connections using Teleport, for example, Ansible.
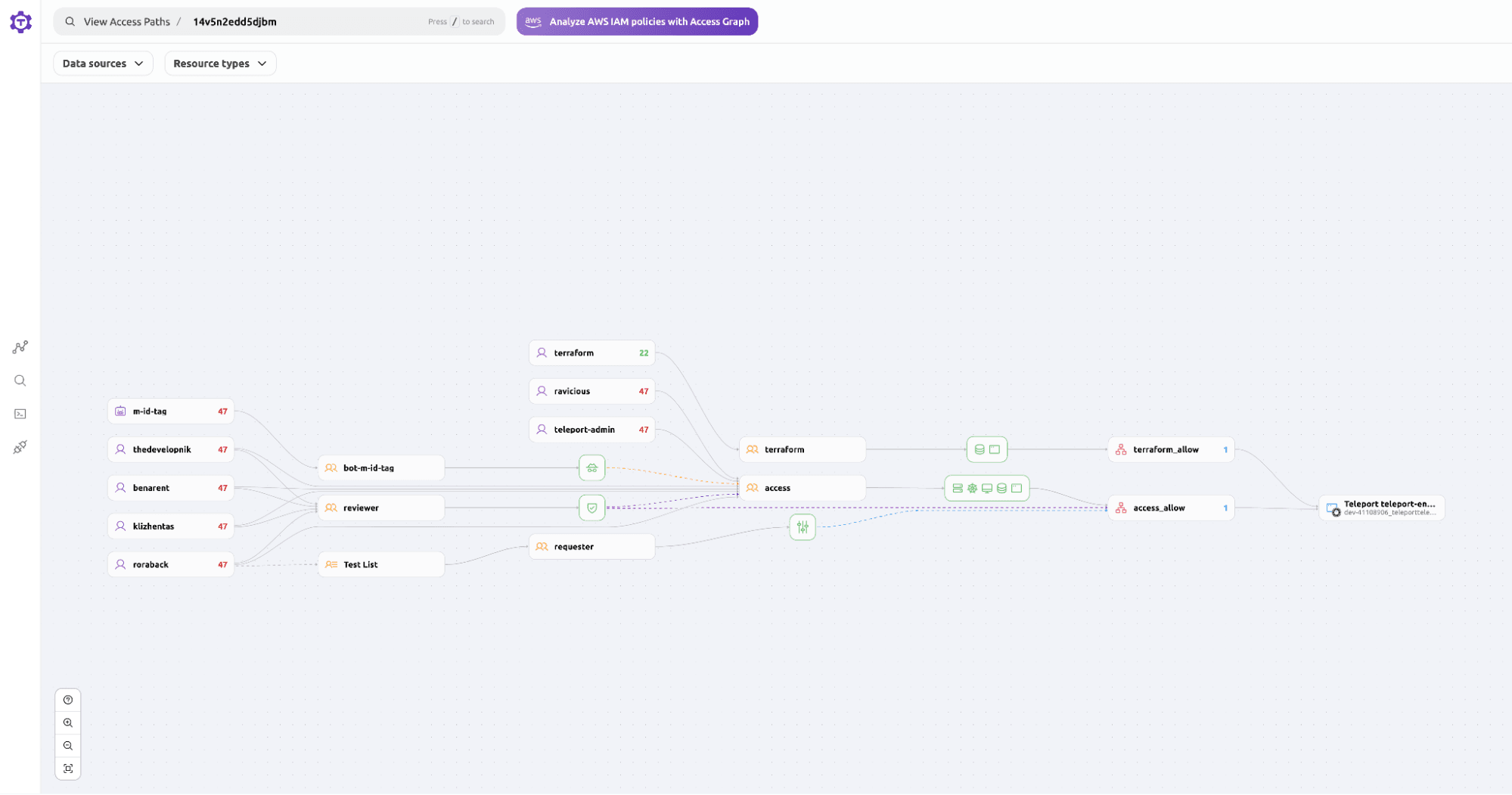
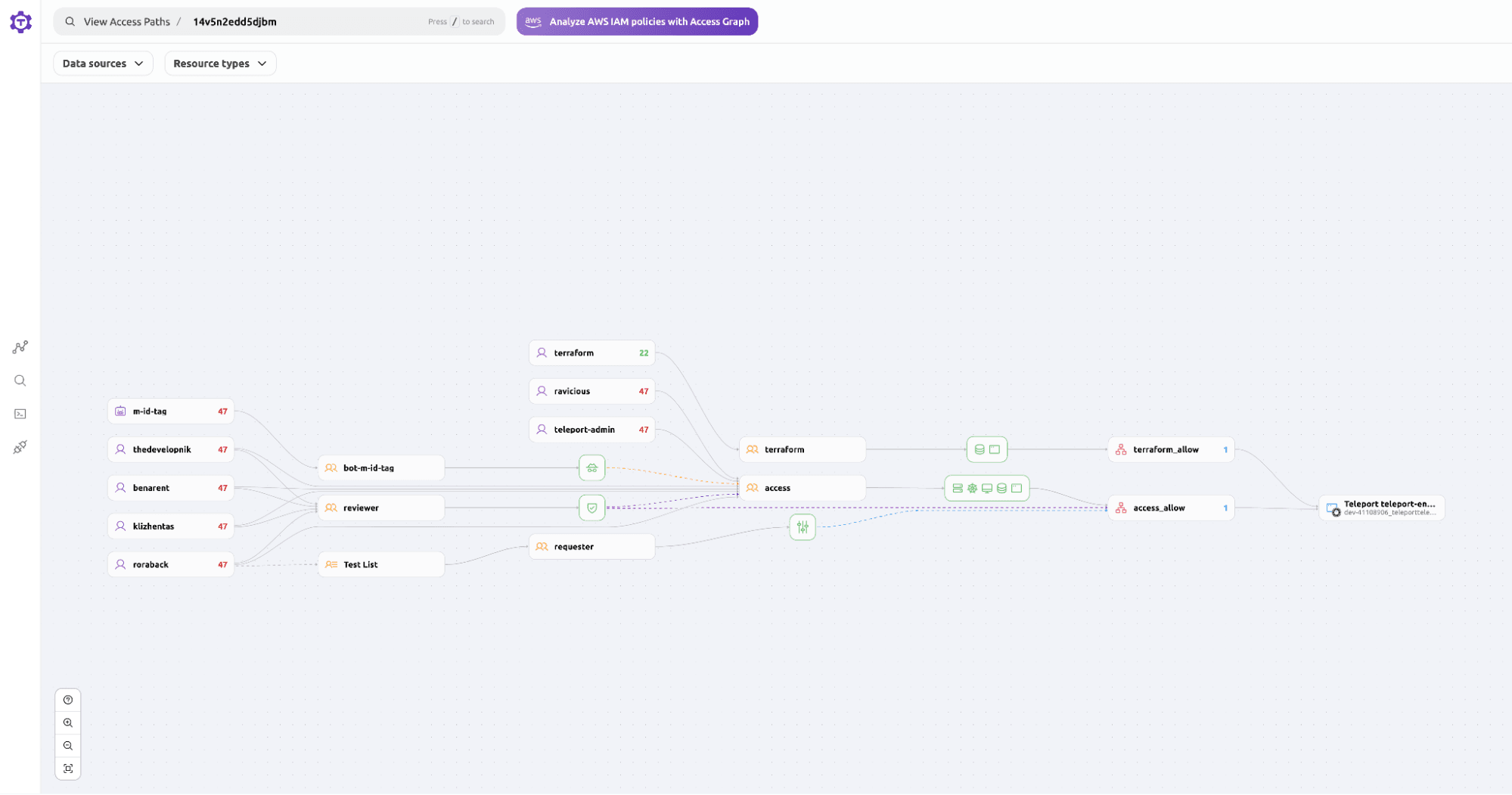
Teleport Identity Security
Teleport Identity Security unifies and controls access policies across all your infrastructure, providing a visually rich view of access relationships and the tools to quickly uncover and remediate long-standing privileges and shadow or risky access paths.
AWS Integration
Theme: Defending against IdP Compromise
Teleport Identity Security integrates with AWS to provide a unified view of access relationships across your AWS infrastructure. By leveraging Teleport Identity Security Access Graph, you can gain insights into IAM permissions, users, groups, roles, and resources within your AWS account, enabling you to identify and analyze access patterns.
With this integration, you can address questions such as what AWS resources are accessible to specific IAM users and roles, which IAM roles are associated with EC2 instances and their permissions, and what AWS resources Teleport users can access when connecting to EC2 nodes.
Teleport Policy's visually rich representation of access relationships helps you uncover and remediate long-standing privileges and risky access paths within your AWS infrastructure. This integration streamlines access management, enhances security, and simplifies the process of monitoring and controlling access to your AWS resources.
Learn more: Docs: AWS Access Patterns with Teleport Policy
Microsoft Entra Integration
Theme: Defending against IdP Compromise
Teleport Identity Security now integrates with Entra to provide a unified view of access relationships across your Entra infrastructure. By leveraging Teleport Identity Security Access Graph, you can gain insights into Entra permissions, users, groups, roles, and resources, enabling you to identify and analyze access patterns.
Okta Integration
Theme: Defending against IdP Compromise
Teleport 16 introduces a new Okta Integration that pulls in groups, users, and apps into the Teleport Policy's Access Graph for teams to better understand access patterns in their infrastructure.
Learn More: Okta Access Patterns with Teleport Policy
Teleport Platform
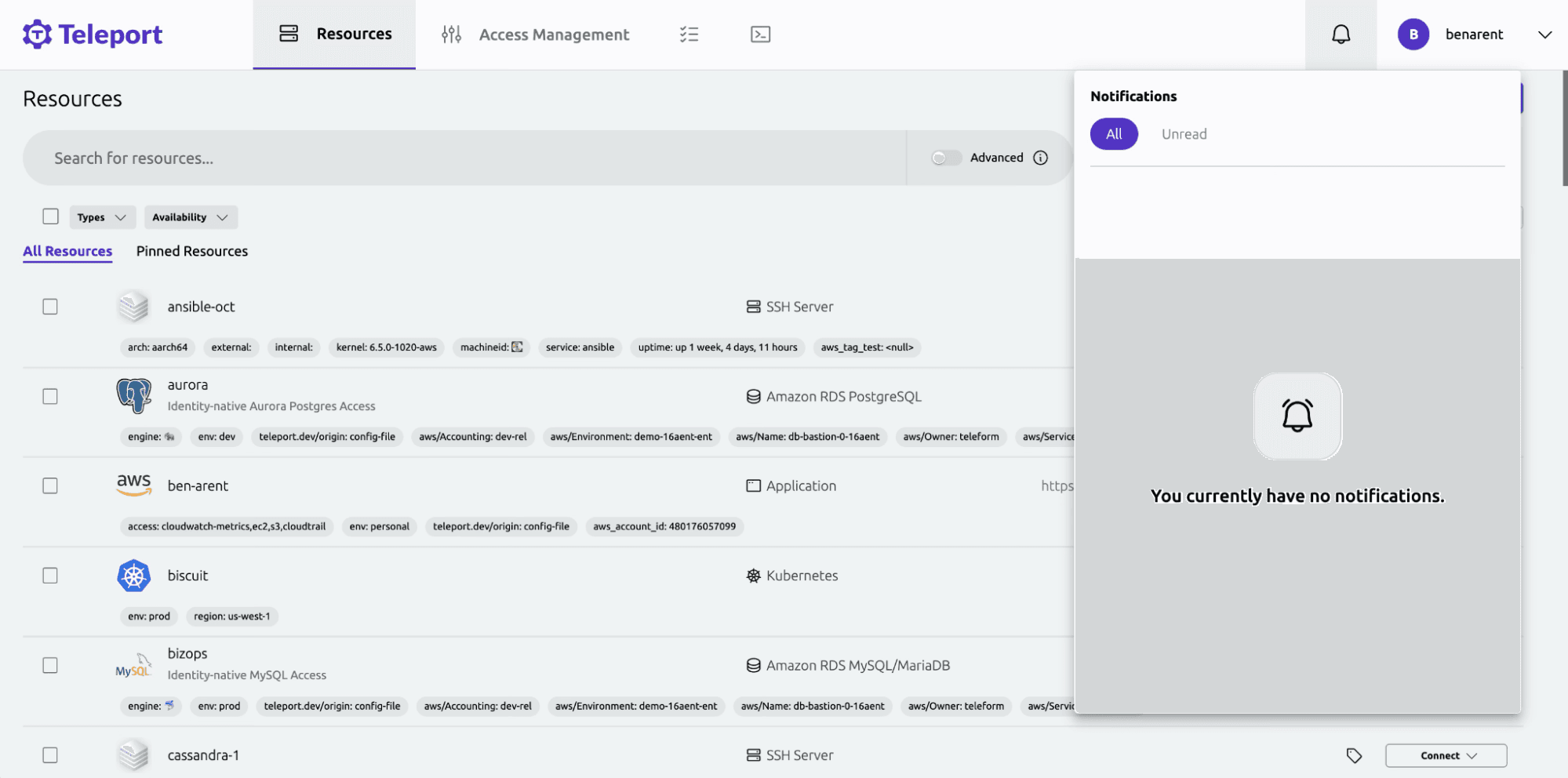
Improved notification system
Theme: Usability
Teleport’s Web Dashboard includes a new notifications system that alerts users to items requiring attention (for example, access requests needing review).
tctl for Windows
Teleport 16 includes Windows builds of the tctl administrative tool, allowing Windows users to administer their cluster without the need for a macOS or Linux workstation.
Additionally, there are no longer enterprise-specific versions of tctl. All Teleport clients (tsh, tctl, and Teleport Connect) are available in a single distribution that works on both Enterprise and Community Edition clusters.
Teleport plugins improvements
Theme: Improved Usability
Teleport 16 includes major improvements to the plugins. All plugins now have
- amd64 and arm64 binaries available
- amd64 and arm64 multi-arch images
- Major and minor version rolling tags (i.e.
public.ecr.aws/gravitational/teleport-plugin-email:16) - Image signatures for all images
- Additional debug images with all of the above features
In addition, we now support plugins for each supported major version, starting with v15. This means that if we fix a bug or security issue in a v16 plugin version, we will also apply and release the change for the v15 plugin version.
Teleport Jamf Plugin
- The Jamf plugin now authenticates with Jamf API credentials instead of username and password.
Multi-region deployment blueprint
Theme: Improved Usability
For self-hosted customers, Teleport 16 introduces an officially supported multi-region deployment blueprint using Cockroach DB. The blueprint provides a reference architecture for massively-scaled clusters that need improved resiliency and the ability to sustain regional failure.
Breaking changes and deprecations
Community Edition license
Starting with this release, Teleport Community Edition restricts commercial usage, as per the above-referenced March 2024 blog post.
License file validation on startup
Teleport 16 introduces license file validation on startup. This only applies to customers running Teleport Enterprise Self-Hosted. No action is required for customers running Teleport Enterprise Cloud or Teleport Community Edition.
If, after updating to Teleport 16, you receive an error message regarding an outdated license file, follow our step-by-step guide to update your license file.
Multi-factor authentication is now required for local users
Support for disabling second factor authentication has been removed. Teleport will refuse to start until the second_factor setting is set to on, webauthn or otp.
This change only affects self-hosted Teleport users, as Teleport Cloud has always required second factor authentication.
Important: To avoid locking users out, we recommend the following steps:
- Ensure that all cluster administrators have second factor devices registered in Teleport so that they will be able to reset any other users.
- Announce to the user base that all users must register an MFA device. Consider creating a cluster alert with
tctl alerts createto help spread the word. - While you are still on Teleport 15, set
second_factor: on. This will help identify any users who have not registered MFA devices and allow you to quickly revert tosecond_factor: optionalif necessary. - Upgrade to Teleport 16.
Any users who do not register MFA devices prior to the Teleport 16 upgrade will be unable to log in and must be reset by an administrator (tctl users reset).
Incompatible clients are rejected
In accordance with our component compatibility guidelines, Teleport 16 will start rejecting connections from clients and agents running incompatible (i.e. too old) versions.
If Teleport detects connection attempts from outdated clients, it will show an alert to cluster administrators in both the Web UI and tsh.
To disable this behavior and run in an unsupported configuration that allows incompatible agents to connect to your cluster, start your auth server with the TELEPORT_UNSTABLE_ALLOW_OLD_CLIENTS=yes environment variable.
Opsgenie plugin annotations
Role annotations must now contain the teleport.dev/notify-services to receive notifications on Opsgenie. The teleport.dev/schedules label is used to determine the automatic approval flow. Detailed setup instructions are available in the documentation.
New required permissions for DynamoDB
Teleport clusters using the DynamoDB backend on AWS now require the dynamodb:ConditionCheckItem permissions. For a full list of required permissions, see the IAM policy example.
Updated keyboard shortcuts in Teleport connect
On Windows and Linux, some of Teleport Connect’s keyboard shortcuts conflicted with the default bash or nano shortcuts (Ctrl+E, Ctrl+K, etc). On those platforms, the default shortcuts have been changed to a combination of Ctrl+Shift+*.
On macOS, the default shortcut to open a new terminal has been changed to Ctrl+Shift+`.
See the configuration guide for a list of updated keyboard shortcuts.
Machine ID and OpenSSH client config changes
Users with custom ssh_config should modify their ProxyCommand to use the new, more performant tbot ssh-proxy command. See the v16 upgrade guide for more details.
Removal of Active Directory configuration flow
The Active Directory installation and configuration wizard has been removed. Users who don’t already have Active Directory should leverage Teleport’s local user support, and users with existing Active Directory environments should follow the manual setup guide.
Teleport Assist is removed
All Teleport Assist functionality and OpenAI integration have been removed from Teleport.
Teleport 16 Webinar
To wrap up this release, we’ll be hosting a webinar on Teleport 16 capabilities. The webinar will be an extension of our post on How To Detect Compromised Identities with Teleport. The webinar, Hardening Infrastructure Security Against SSO Identity Provider, Compromise, is set for July 11 at 9am PT.


Teleport partnered with security researcher Doyensec to explore the current state of the third-party identity management security market and steps that companies can take, using Teleport, to implement an additional layer of security in order to reduce the impact of a compromised SSO provider. The paper summarizes Doyensec’s findings, including a Hardening Checklist for defense against IdP compromise, as well as commentary from Jack Poller, Principal Analyst of Paradigm Technica. Customers may request Doyensec’s full research report from their Teleport account manager.
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter