TELEPORT IDENTITY SECURITY
Turn Session Recordings into Security Intelligence
The first step toward autonomous investigations
Teleport Identity Security summarizes interactive SSH, Kubernetes, and database sessions, classifies them by risk level, and shows a timeline of activity. Security teams review what matters — platform teams see where to automate.
Trusted by Market Leaders
















THE IDENTITY SECURITY CHALLENGE
Manual session review doesn't scale
Security teams at compliance-driven organizations dedicate countless hours reviewing session recordings every week.
Endless session reviews
Security teams at compliance-driven organizations dedicate countless hours reviewing session recordings every week.
Barriers to automation
Platform teams want to know what engineers are doing on hosts and in clusters so they can reduce toil and build automation, but nobody has time to scrub through hours of playback.
Automated session analysis does
Both problems point to the same solution: automated visibility into every session without a human watching it.
Teleport's session analysis is an always-on observer that summarizes, classifies, and flags activity
across every recorded session — and the first step towards fully autonomous security investigations.
Session timeline view
Sessions have a chronological breakdown of activity. Jump directly to risky commands instead of scrubbing through playback to find it.
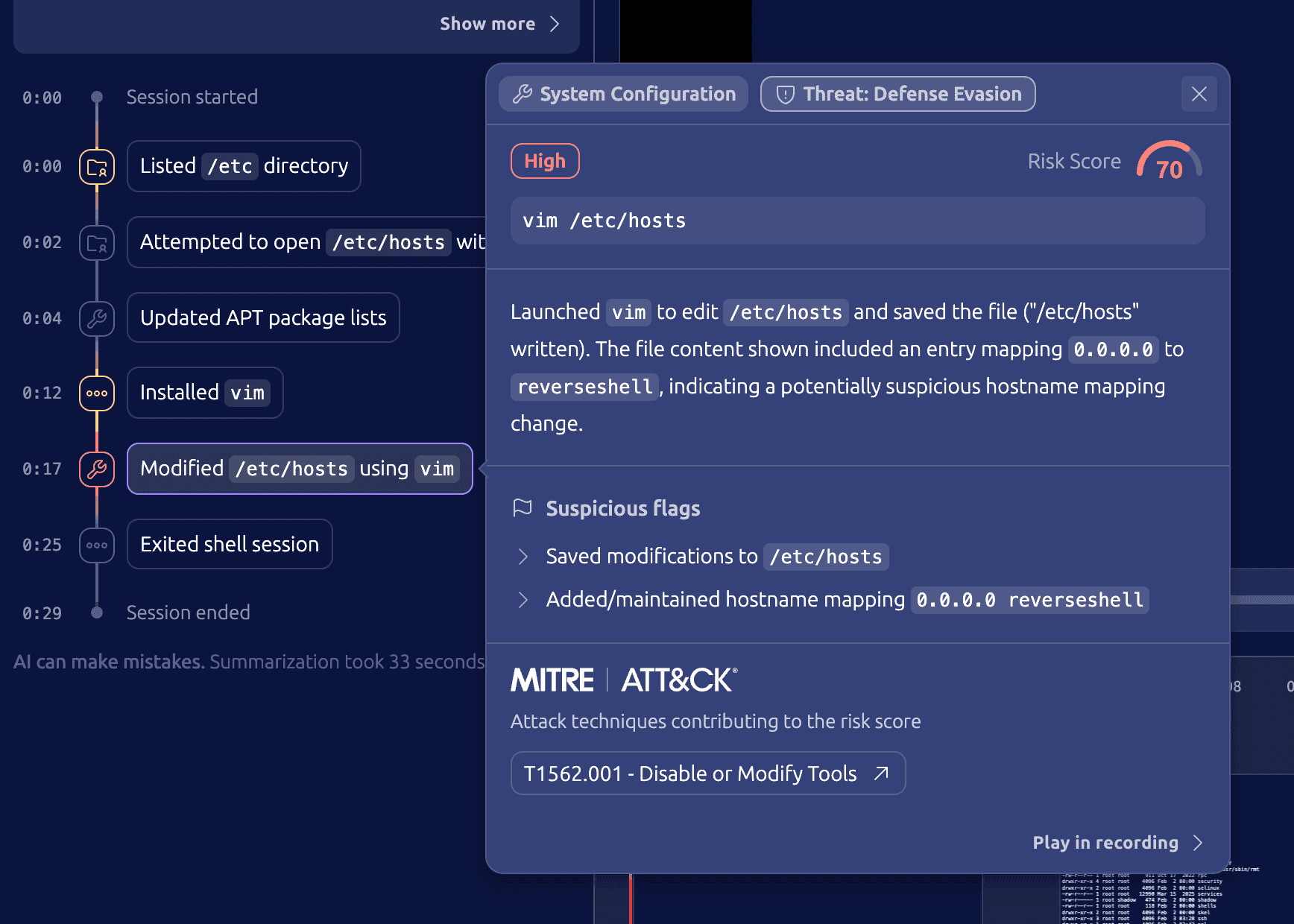
Audit events for risk levels
Risk classifications (Low / Medium / High / Critical) emit audit events. Session Timeline Events map to attack techniques outlined in the MITRE AT&CK Framework. Route directly to Splunk, Datadog, PagerDuty, or any existing log pipeline. No custom integration required.
One-click setup
In Enterprise Cloud, enable session summaries with one click and an opt-in to AI terms. No API keys to configure, no infrastructure to deploy. Included in current Identity Security pricing.
How it works
Observe
Teleport records interactive SSH, Kubernetes, and database sessions. This includes PTY output, JSON events, and optional kernel-level (eBPF) system tracing.
Summarize
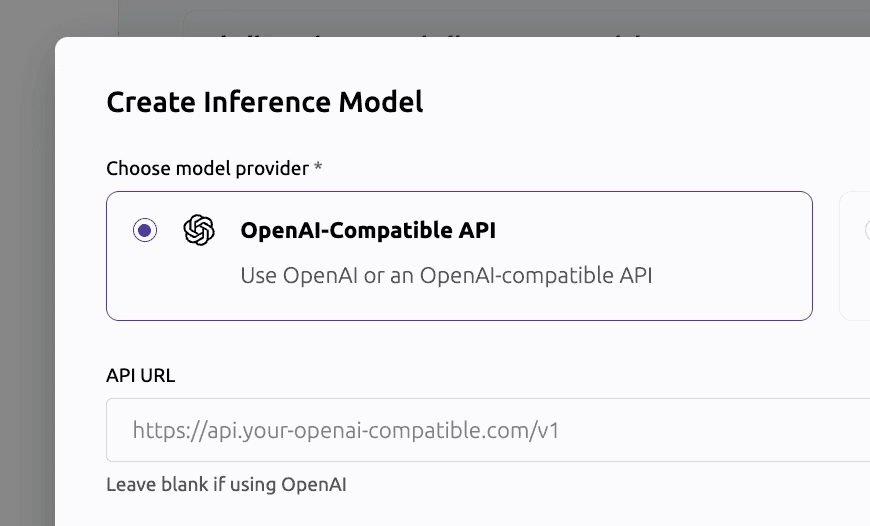
After a session ends, Teleport routes the recording to an LLM based on configurable inference policies. You choose the provider: OpenAI, Amazon Bedrock, or any OpenAI-compatible gateway.
Classify
The model assigns a risk level (Low, Medium, High, or Critical) based on what commands were run and whether there are signs of obfuscation or unusual behavior. With MITRE ATT&CK Mappings to understand the potential risk of commands being executed.
Alert
Risk classifications emit audit events that go to your existing SIEM and alerting tools.
We came in expecting session recording summaries to be easy to bypass. They weren't. The models are surprisingly resistant to the most common evasion techniques, and they've gotten significantly better even in the last few months.
- Marcus Niemietz, Persistence Security
Who uses this and why
Security and compliance
Review flagged sessions instead of all sessions. Risk classifications go to your SIEM as audit events, and session summaries give auditors the evidence they need for SOC 2, PCI, FedRAMP, and HIPAA without manual playback.
Platform engineering
Most platform teams don't want engineers exec-ing into pods or SSHing into servers. Session summaries show you what people are actually doing on hosts, making it easier to build the automation and runbooks that replace those sessions.
Third-party and vendor access
When vendors access your infrastructure through just-in-time access requests, session summaries give you an immediate record of what they did. Verify that they stayed within scope without watching the full session.
Ready to Teleport?
Frequently Asked Questions
What are session recording summaries?
Teleport records interactive SSH, Kubernetes, and database sessions. Session recording summaries send those recordings to an LLM, which produces a structured summary and a risk classification. Instead of watching hours of playback, you read a summary and decide whether to dig deeper.
What's new in the timeline view?
Teleport 18.7 adds a chronological timeline of session activity, so you can see what happened when and jump to specific moments. It also adds audit events for risk classifications (which you can send to your SIEM) and one-click setup in Enterprise Cloud.
How does risk classification work?
The LLM analyzes each session and assigns a risk level: Low, Medium, High, or Critical. The classification is based on what commands were executed, whether there's obfuscation or encoding, and how the session compares to expected behavior. Each classification emits an audit event you can route to your alerting tools.
Is my session data sent to a third-party AI provider?
Only if you turn the feature on. Summarization is disabled by default. When enabled, session data goes to whatever inference provider you configure (OpenAI, Amazon Bedrock, or a self-hosted model via LiteLLM). Self-hosted customers control the entire data path. Providers do not retain session data after processing.
Can attackers evade session recording summaries?
We hired Persistence Security to find out. They ran 150+ attack sessions and found that current LLMs are resistant to most common evasion techniques, including prompt injection and command obfuscation. The attacks that worked (mainly encoding tricks that triggered content filters) still produced detectable signals: a failed or rejected summary is itself something that can trigger alerts. A report of these findings can be found in the Teleport Trust Center.
How much does it cost?
Session summaries are included in Teleport Identity Security pricing for Enterprise Cloud. You pay your own inference provider costs (OpenAI API usage, Bedrock invocations). Inference policies let you control which sessions are summarized, so you can manage spend.
Can I use my own models?
Yes. OpenAI, Amazon Bedrock (self-hosted), or any OpenAI-compatible API through LiteLLM. You can run open-source models on your own infrastructure.