Home - Teleport Blog - Is JIT the Secret to Engineer Happiness?
Is JIT the Secret to Engineer Happiness?

Engineering teams lose hours of their work week to access bottlenecks.
Shared credentials, manual checkouts, and ticket-based privileged access management (PAM) tools are poorly equipped to keep up with the speed and complexity of today’s distributed engineering environments.
These bottlenecks stand in the way of critical engineering work. This can ultimately introduce real security risks (but more on that later).
Just-in-time (JIT) access offers an alternative: access that is temporary, request-driven, and fully self-service. This blog breaks down:
- Why legacy access patterns hurt engineering speed — and why platform teams bear the brunt.
- How JIT access restores speed and control.
Shared credentials delay (and add risk to) engineering access
Engineering teams often treat access delays as unavoidable.
“That’s just how it works here.”
But shared credentials and checkout workflows create a compounding tax on engineering productivity.
1. Checkouts create wait time, even for routine tasks
An engineer needs five minutes of read-only access to a production database to validate whether a migration succeeded.
In a legacy PAM workflow, this means they must:
- File a ticket
- Wait for approval
- Wait for a VPN or jump host
- Check out shared credentials
- Perform the task
- Check everything back in
Each step adds friction, and each handoff adds delay.
Across a full team, these micro-delays can add up to hours of cumulative idle time every week, and hundreds of hours per year.
2. Shared credentials increase your attack surface
Shared credentials create invisible risks that compound over time. When multiple people use the same account, teams end up with:
- Unclear attribution
- Inconsistent role alignment
- Overly broad permissions
- Long-lived access no one can clean up
This combination expands the blast radius of every action taken through a shared account.
Security teams know these patterns increase exposure. Engineers know they slow work down.
3. Platform teams shoulder most of the burden
Shared credential workflows also place a disproportionate operational load on the platform teams responsible for keeping access functioning.
Platform engineers routinely spend hours of their work week:
- Fulfilling access tickets that could easily be automated.
- Sifting through audit logs manually to reconstruct who used a shared account.
- Debugging routine access failures caused by expired VPN sessions or open checkouts.
- Rotating shared credentials (just to unknowingly break a pipeline).
- Tracking down standing privileges no one remembers granting.
And at the end of the week, none of this work will have resulted in a meaningful improvement.
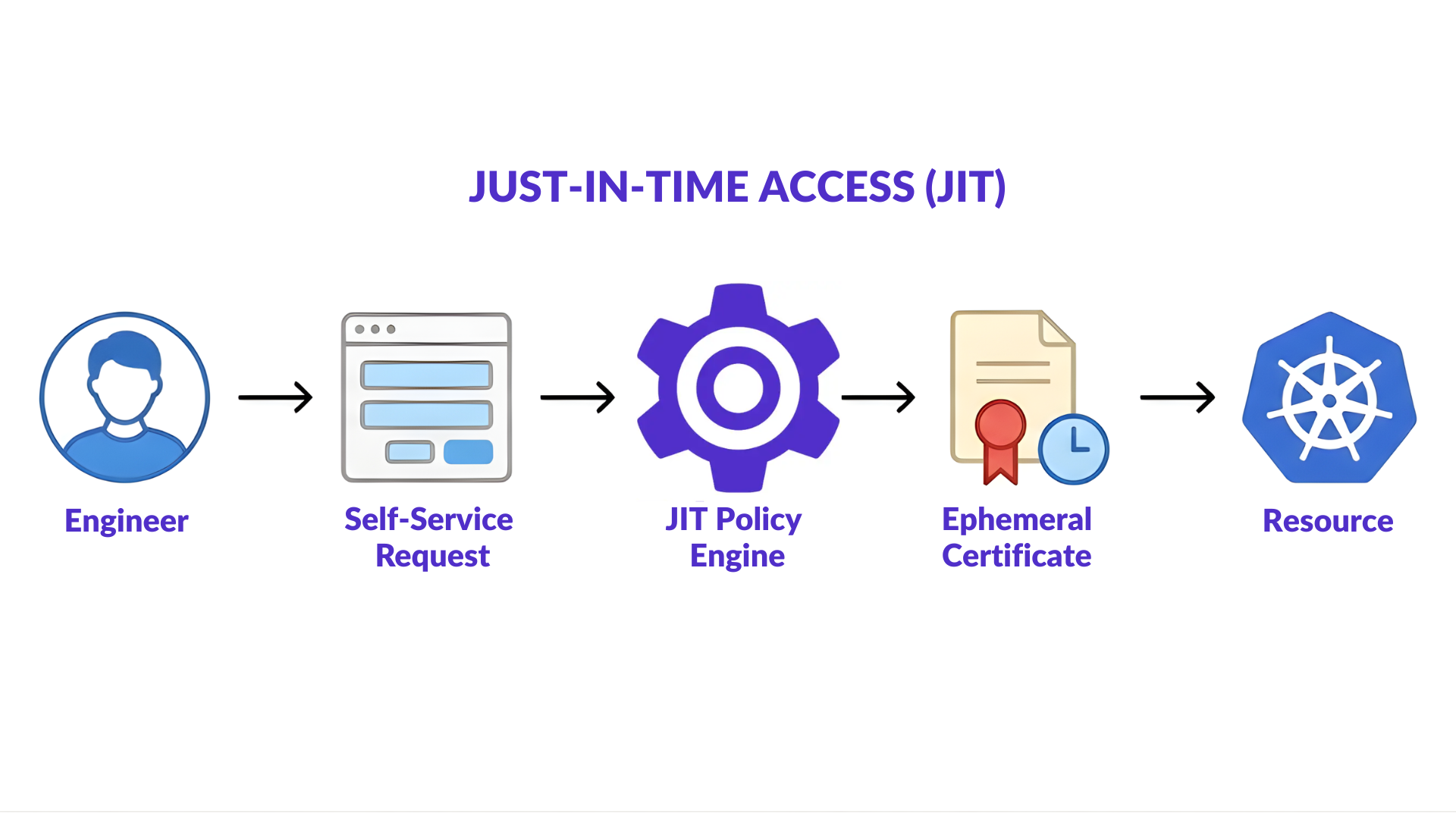
What is Just-in-Time (JIT) access?
Just-in-time (JIT) access flips the default from “always on” to “only when needed.”
Instead of long-lived accounts and standing privileges, engineers receive temporary access that activates for a specific task and expires automatically.
In practice, JIT turns access from a manual, ticket-driven process into an automated, on-demand workflow that prevents access bottlenecks as teams and infrastructure scales.
Why is JIT access better for engineering work?
Just-in-time access takes a different approach: no shared credentials, no waiting for approvals, no manual checkouts. Access is granted only when needed, only to the right identity, and only for the duration of the task.
1. Engineers get instant, auto-expiring access
Engineers request access based on policy and receive it automatically. No waiting in ticket queues, on-call delays, or credential checkouts.
When a developer needs ten minutes of read-only production access to validate a failed job, they request access through the CLI and receive a short-lived certificate in seconds.
Engineering velocity improves because access is self-service, not mediated.
2. Guardrails keep access tightly defined automatically
JIT access is not a free-for-all. Policies enforce:
- Least privilege
- Role-based access control (RBAC) and attribute-based access control (ABAC)
- Automatic expiration
- Full identity-based audit logging
A junior engineer accidentally requests temporary write access for a maintenance task. Policy automatically downgrades the request to read-only because the engineer’s role does not permit write privileges.
They still get what they need, and security guardrails are applied automatically without slowing anyone down or creating ticket back-and-forth.
3. Massive amounts of manual access work — gone
With JIT access, engineering and platform teams are no longer forced to manage shared credentials or sift through access tickets. Instead, they can focus on improving infrastructure.
During an incident, no one needs to wake up a platform engineer to grant emergency console access. Engineers request it, receive a time-limited certificate, and the platform team focuses on remediation rather than being a bottleneck.
JIT access turns access management into an automated and readily-scalable control plane.
What is the impact of JIT on engineering culture?
Just-in-time access is more than a security upgrade. In reality, it can meaningfully improve engineering culture. Faster access, less risk, and happier engineers will do that.
Imagine having:
- Fewer blocked tasks
- Cleaner audit trails
- Reduced ticket noise
- Faster incident response times
- Faster onboarding/offboarding
- Consistent least-privilege discipline
When access becomes self-service, teams spend less time waiting and more time building.
The result is a healthier engineering day-to-day — one with less user friction, no shared credential risks, and more time available to spend on high-value projects.
How JIT works with Teleport
Teleport delivers just-in-time access through an identity-first, vault-free PAM approach designed to remove access bottlenecks while improving infrastructure security.
Instead of storing or rotating shared credentials, Teleport issues short-lived certificates that expire automatically after each task or session.
This completely eliminates standing privileges and the operational overhead of credential handling processes like rotations, checkouts, and manual approvals.
Ephemeral privileges, zero stored secrets
Every engineer, machine, and AI identity receives certificates at request time that automatically expire. Once the certificate expires, privileged access disappears with it.
No shared accounts, secrets to manage, or static credentials to audit.
Self-service access with built-in guardrails
Engineers request access through existing workflows, including CLI, Slack, PagerDuty, or the Teleport API or web UI.
Policy determines what is approved automatically, what requires elevated review, and how long access should last.
Security teams define the boundaries. Teleport automates the workflow.
Unified JIT for Kubernetes, servers, databases, AI, and more
Many point solutions apply JIT only to servers or specific apps while neglecting infrastructure like Kubernetes.
Teleport implements just-in-time, task-based access across everything, including:
- Servers & SSH
- Kubernetes
- Databases
- Web apps
- Windows servers
- GitHub
- Clouds (AWS, GCP, Azure)
- Automation workflows
- AI/agentic systems (like Bedrock)
- MCP servers
- And more
All infrastructure is governed with the same identity authority, audit trail, and policy model.
Complete identity-level auditability
All human and non-human activity is captured at the identity level, not the account or service level. This means logs show exactly who accessed what, when, for how long, and what they did.
Session replays, command logging, and AI-generated session summaries make access reviews fast and reliable.
Permanently less manual work, not a redistribution
Teleport’s approach eliminates the existence of shared credentials and manual checkouts, rather than attempting to manage them more efficiently.
Teams no longer rotate secrets, track check-ins/outs, or field emergency access tickets. Instead, JIT becomes a scalable, low-friction control rather than an ongoing operational burden.
Get started with JIT made for engineers
Teleport makes JIT access simple, consistent, and identity-bound across all infrastructure: past, present, and AI-future.
Learn more about Teleport JIT access or request a demo.
More Resources
- Read: How Teleport Simplifies Just-in-Time Access
- Read: 5 Ways to Keep AWS Fast with Just-in-Time Access
- Read: Modern Infrastructure Demands a Modern Approach to Privileged Access
- Watch: Eliminating Privileged Access Toil with Infrastructure Identity
- Learn: Implement Just-in-Time Access Requests
- Learn: Vault-Free Privileged Access Management (PAM)
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter