Home - Teleport Blog - 4 Ways to Secure Bedrock Agent-Initiated Actions with Teleport
4 Ways to Secure Bedrock Agent-Initiated Actions with Teleport
AI Agents are Everywhere Already
AI agents powered by Amazon Bedrock are playing an increasingly central role in cloud operations. These agents can interact directly with core AWS services like S3, Lambda, RDS, and EC2 to perform tasks such as data retrieval, automation orchestration, and resource provisioning.
Many teams rely on the Model Context Protocol (MCP) to structure agent behavior and convert natural language into actionable commands. But here’s the catch: MCP doesn’t care who makes the request or whether it should happen in the first place. It’s just the messenger, and without guardrails, you risk unauthorized access to sensitive data by users or bots.
In this blog, we’ll show how Teleport enables secure identity, policy enforcement, and auditing for agent-initiated infrastructure actions using MCP.
Any Unmanaged Access is Risky, Human or Not
If MCP servers and agents share the same admin credentials, there’s no way to distinguish one from the other — and no way to limit what they can or cannot do. To make matters worse, these credentials don’t rotate or expire unless someone intervenes manually.
What is considered standard security hygiene for humans becomes difficult or, in many cases, impossible to properly enforce for agents. For example, revoking access after misfired tasks, or identifying who or what touched production data last Tuesday morning.
How to Secure Agentic AI and Embrace Automation
The secret to retaining the flexibility of MCP and Bedrock (without compounding security debt) starts with identity. In this context, “identity” refers to assigning unique identifiers to each AI agent and server within the system. This allows for precise control and auditing of their actions.
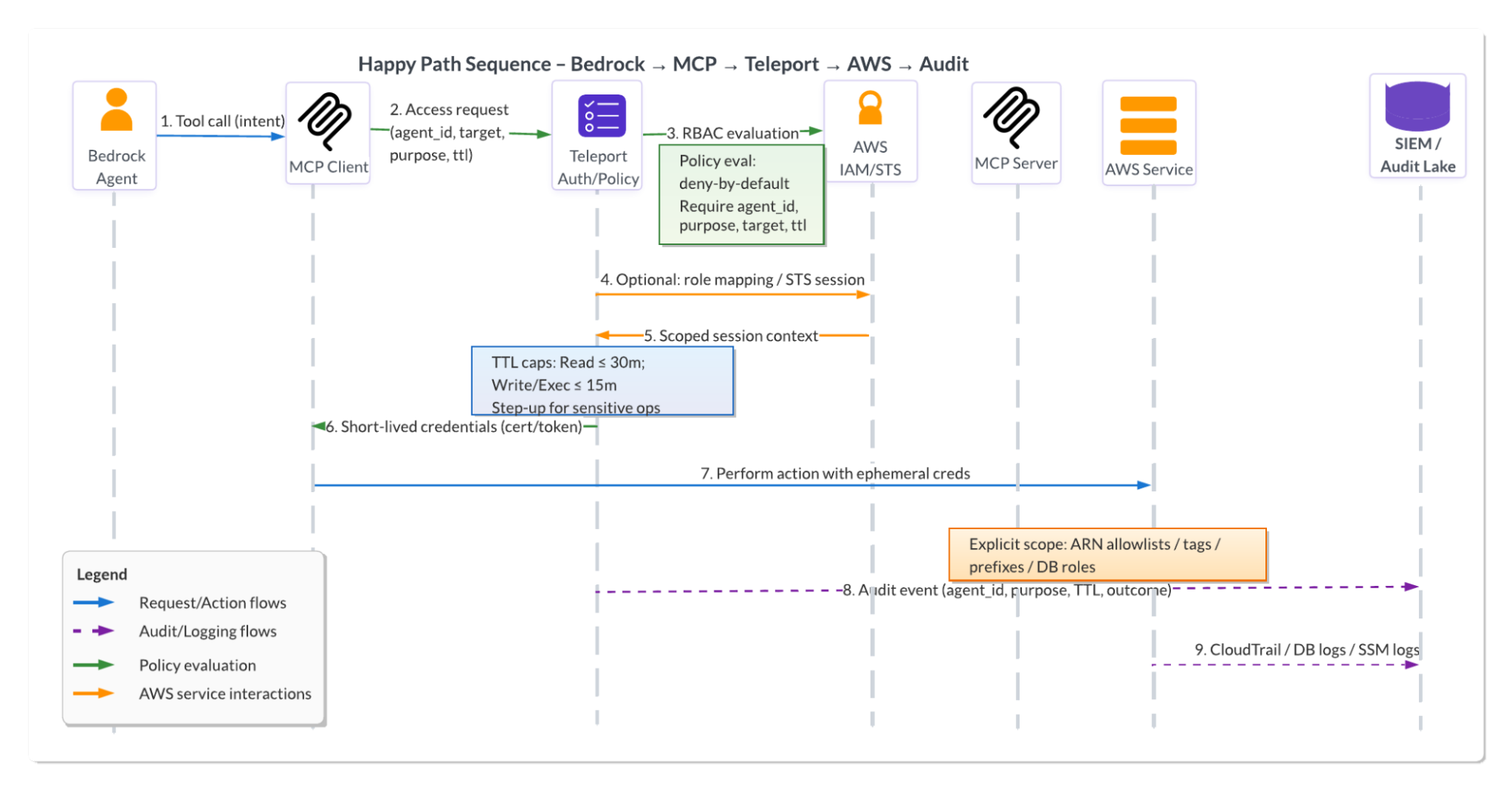
Teleport plays a crucial role in securing MCP-based systems. It achieves this by registering each MCP server with a unique identity using AWS IAM roles and x.509 certificates. This process enhances security and builds confidence in the system’s robustness.
When an AI agent starts a task, the MCP server sends a request to Teleport with the context, including the agent ID, target resource, and task description. Teleport verifies the request against policy and, if approved, issues a short-lived certificate for that session. This ensures dynamic, per-task access for agents with full audit logging using the same security framework as for humans and machines (such as Git runners or CI/CD automation).
Watch our on-demand webinar, How to Safeguard MCP and Agentic AI, co-hosted with AWS, to get a closer look at how this works in real time.
Watch WebinarThis ensures all agent activity follows the appropriate guardrails. Actions are transparent and fully traceable to a specific agent identity. Let’s examine four ways to apply this model via Bedrock across common AWS services.
1. Safely invoking Lambda functions with support agents
A Bedrock-powered support agent must trigger AWS Lambda functions to perform support tasks, such as password resets and credit issuance. Wide MCP server permissions allow this agent to invoke any Lambda function, including those outside of the support function.
Steps to implement
- Define a policy in Teleport that allows access to only specific Lambda ARNs used by the support agent.
- Register the MCP server with Teleport and associate it with the correct identity and permissions.
- When the agent sends a task request (e.g., reset password), the MCP server includes metadata and calls Teleport to request access.
- Teleport verifies the request and issues a short-lived token, valid only for the approved Lambda function.
The Result: Policy-driven Lambda access with full auditability
The support agent can now safely invoke only the Lambdas for which it is authorized. Access is session-based, restricted by policy, and logged with context like task type and prompt origin. Unauthorized attempts to call other functions are denied, improving control and auditability.
2. Just-in-time EC2 access for remediation agents
An incident response agent must connect to multiple EC2 instances to perform diagnostics or implement fixes. This agent requires secure, temporary access to production instances tagged for remediation only.
Allowing broad EC2 access can increase the risk of AI overreach, especially if the agent can access non-production or nearby production systems beyond its designated role.
Steps to implement
- Define a Teleport role that provides a clear and enforceable access policy, allowing access only to EC2 nodes with specific tags (e.g.,
env=prod,purpose=remediation). - Enroll the MCP server in Teleport so that it can request access based on the agent task context.
- When a remediation task starts, the MCP server, which acts as a gateway for agent requests, sends a request to Teleport with details such as the agent ID and target node labels. The MCP server mediates access requests, ensuring they comply with policy.
- Teleport checks the policy, approves the session, and enables temporary access via AWS Systems Manager.
The Result: Just-in-Time EC2 access with full audit trails
As a result, the agent is granted just-in-time EC2 access only for the exact instances it’s supposed to reach. All access is temporary, tightly defined, and auditable. This reduces the risk of lateral movement and ensures that emergency actions remain within defined boundaries, providing reassurance about the security measures in place.
Beyond MCP and Bedrock, Teleport also extends consistent just-in-time access and least privilege enforcement across AWS. Read our latest blog to learn how to apply just-in-time access to AWS resources to accelerate engineering velocity.
3. Controlled S3 access for AI training pipelines
An agent is used to prepare datasets for model training, which requires read-only access to specific S3 paths. Without controlled access, the MCP server may use long-lived S3 credentials that allow the agent to explore or modify unrelated data.
Steps to implement
- Create a policy in Teleport that allows access only to the intended S3 prefix (e.g.,
s3://ml-datasets/project-x/raw/) and restricts the agent to thes3:GetObjectaction. - Register the MCP server in Teleport, using AWS IAM integration and x.509-based identity.
- When the agent requests access for a preprocessing task, the MCP server passes the task context to Teleport.
- If the request aligns with policy, Teleport issues a short-lived, read-only token valid only for the allowed S3 path.
The Result: All S3 access is tightly scoped, temporary, and logged
The training agent can access exactly the data it needs, but nothing more. All S3 interactions are policy-bound, time-limited, and logged for compliance. Sensitive data and other projects remain protected, and the pipeline stays focused and secure.
4. Secure RDS access for finance agents
An agent is responsible for generating monthly financial reports by querying data from Amazon RDS. With stock MCP controls, this agent would likely operate using a long-lived credential, exposing the database to unnecessary risk, making it challenging to enforce task-specific access, and preventing reliable attribution of queries to a specific agent or report.
Steps to implement
- Use Teleport’s AWS integration to register the MCP server and assign it a unique identity using IAM roles and x.509 certificates.
- Create a Teleport role that allows access only to specific RDS databases (
transactions,ledger) under areadonlyuser, with a short session time-to-live and optional MFA enforcement. - When the agent is ready to generate a report, the MCP server submits a session request to Teleport with metadata, such as
agent_id=finance.report.001andtask=generate_monthly_summary. - Teleport evaluates the request, approves it if it matches policy, and issues a short-lived certificate for the duration of the session.
The Result: Identity-traceable, least privilege RDS sessions
The finance agent can only access the RDS databases it needs, for the specific duration required, and under controlled permissions. Every query session is logged with metadata, including the agent's identity, the role used, the databases accessed, and the purpose of the task. This provides clear traceability, minimizes credential exposure, and ensures the agent operates within tightly defined security boundaries.
Why This Matters for AI Innovation
Because AI agents act autonomously, we must treat them in the same manner as we treat human operators. That means providing them with scoped, auditable access instead of broad, persistent permissions.
Teleport makes this possible — and more.
Each access request is evaluated. Each session is separate. Each action is connected to a purpose. This provides platform and security teams with confidence to scale agentic automation while maintaining control and visibility.
Ready to Secure AI Agents with Teleport?
Learn more about Teleport for securing AI infrastructure, or continue exploring how Teleport secures and simplifies AWS.
Teleport for AIGet a Demo
Table Of Contents
- AI Agents are Everywhere Already
- Any Unmanaged Access is Risky, Human or Not
- How to Secure Agentic AI and Embrace Automation
- 1. Safely invoking Lambda functions with support agents
- 2. Just-in-time EC2 access for remediation agents
- 3. Controlled S3 access for AI training pipelines
- 4. Secure RDS access for finance agents
- Why This Matters for AI Innovation
- Ready to Secure AI Agents with Teleport?
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter