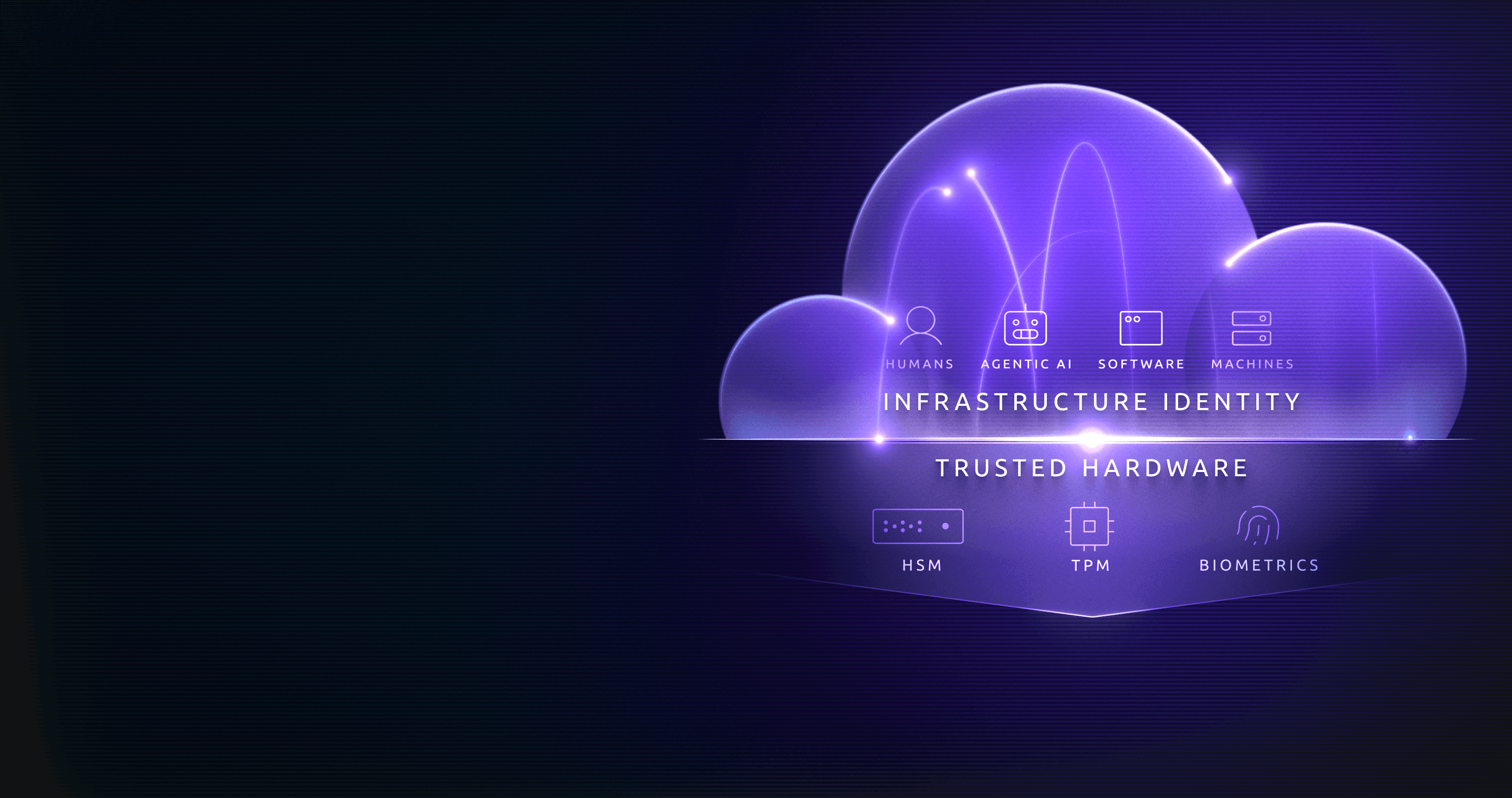
UNIFIED IDENTITY LAYER
Infrastructure Identity for Humans, Machines, Software, and Agents
Treat every identity as a first class citizen, implemented with strong identity and unified in one layer to improve resilience and drive operational efficiency across your infrastructure. A prerequisite for securely implementing AI in infrastructure.
TRUSTED BY LEADERS


















FRAGMENTED IDENTITIES INTRODUCE RISK
Why Secrets Don’t Scale
Every engineer has faced the challenge of too many access paths, passwords, and credentials to handle, often resorting to shortcuts that increase risk.
However, the real risk in static credentials is not just that they’re messy and difficult to manage. They proliferate everywhere, with accounts registered in different resources. At scale, there are too many access paths to watch, govern, or control. Determined hackers can eventually find a way in to get to sensitive data.
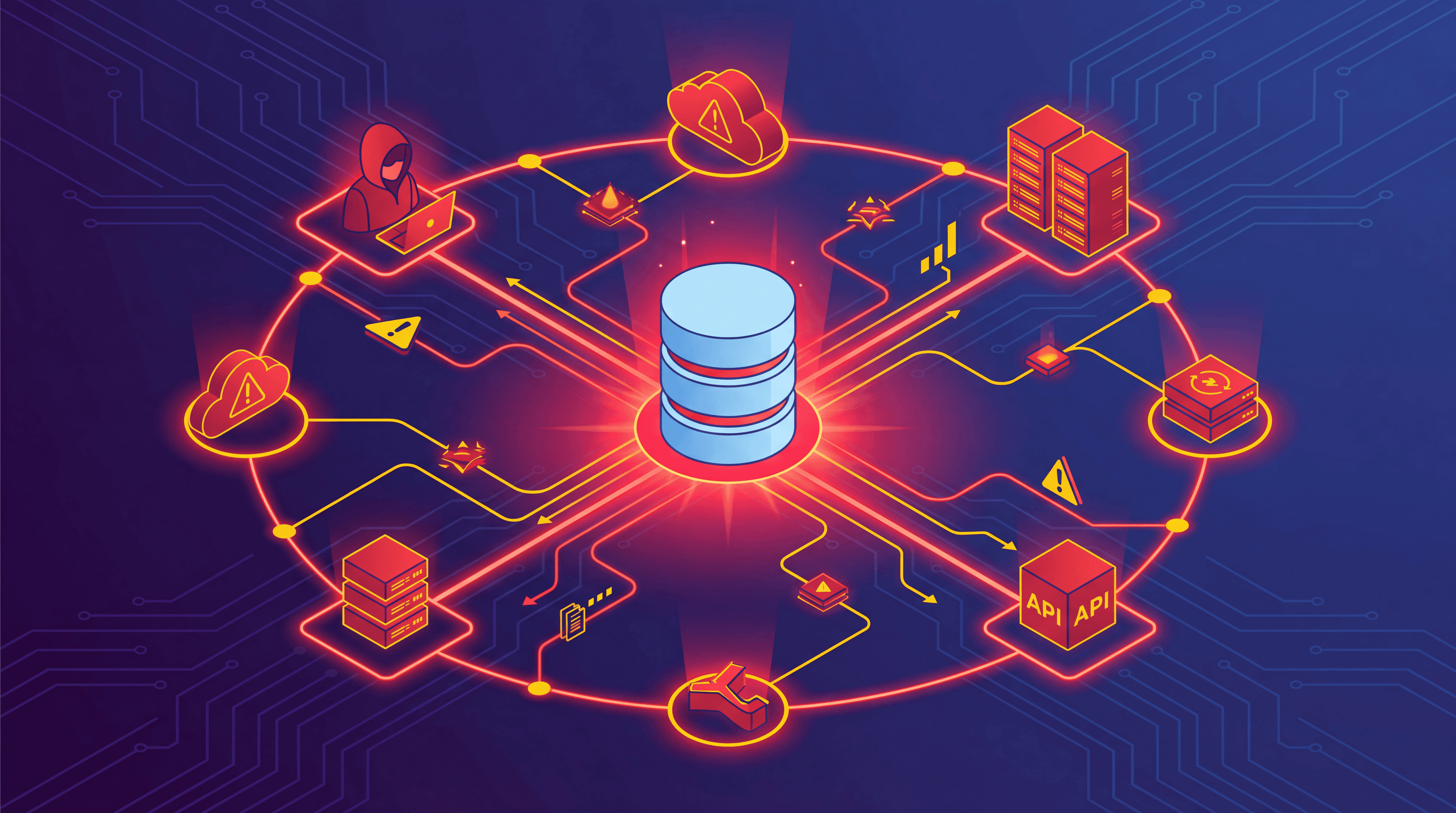
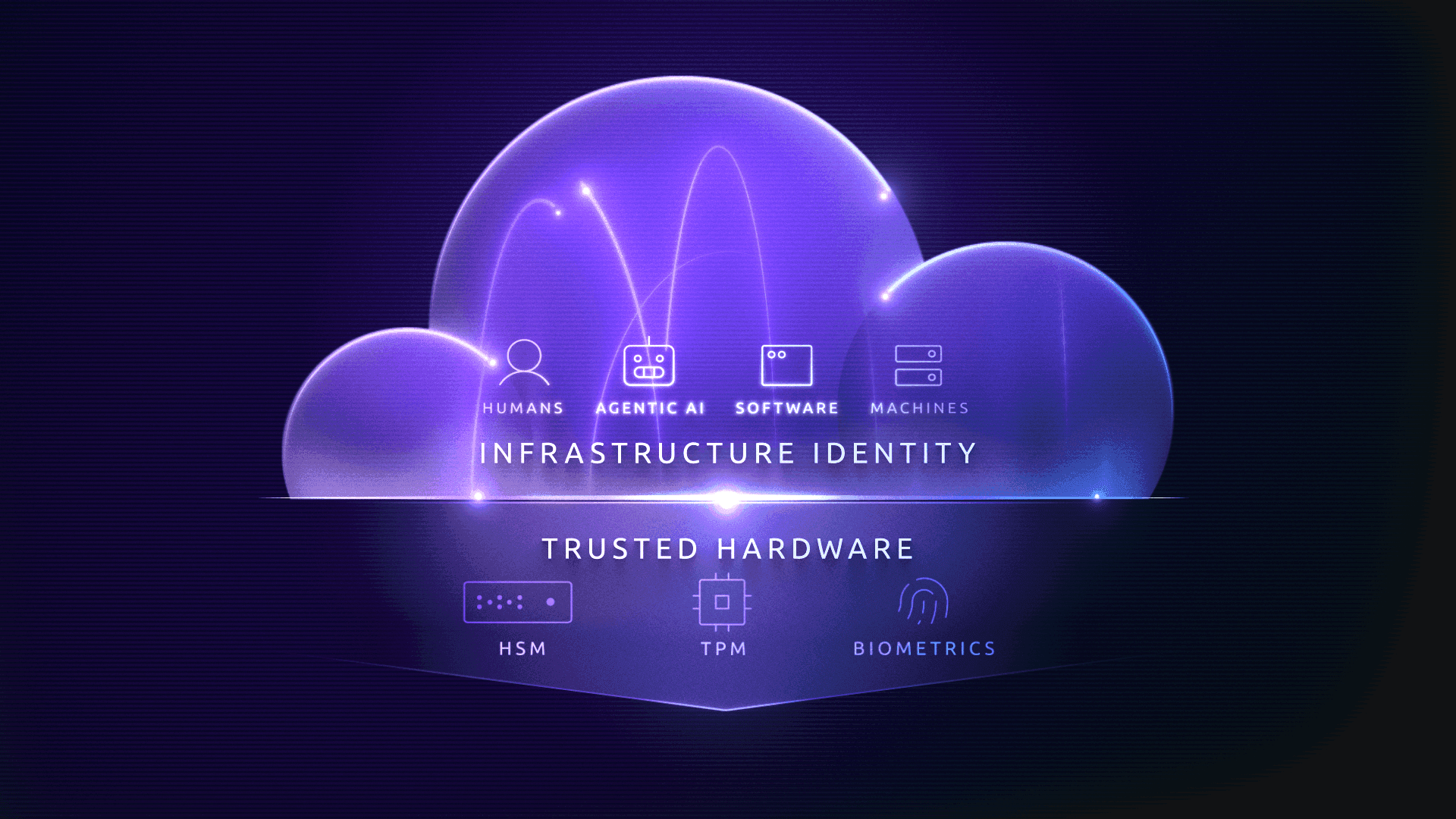
Unified Identity Is Necessary for Securing AI Infrastructure
In the age of AI, layering nondeterministic agents on top of a myriad of unprotected access paths is a recipe for disaster. A unified identity layer, implemented with strong identity, protects organizations against identity compromise and can readily be extended from securing humans and machines to also securing AI, accelerating the path to business innovation.
Teleport Unified Identity Layer
Teleport unifies identities and secures access for your entire infrastructure with:
Strong identity implementation
Unified humans, machines, and agentic AI
Zero trust access control: secretless authentication + ephemeral privileges
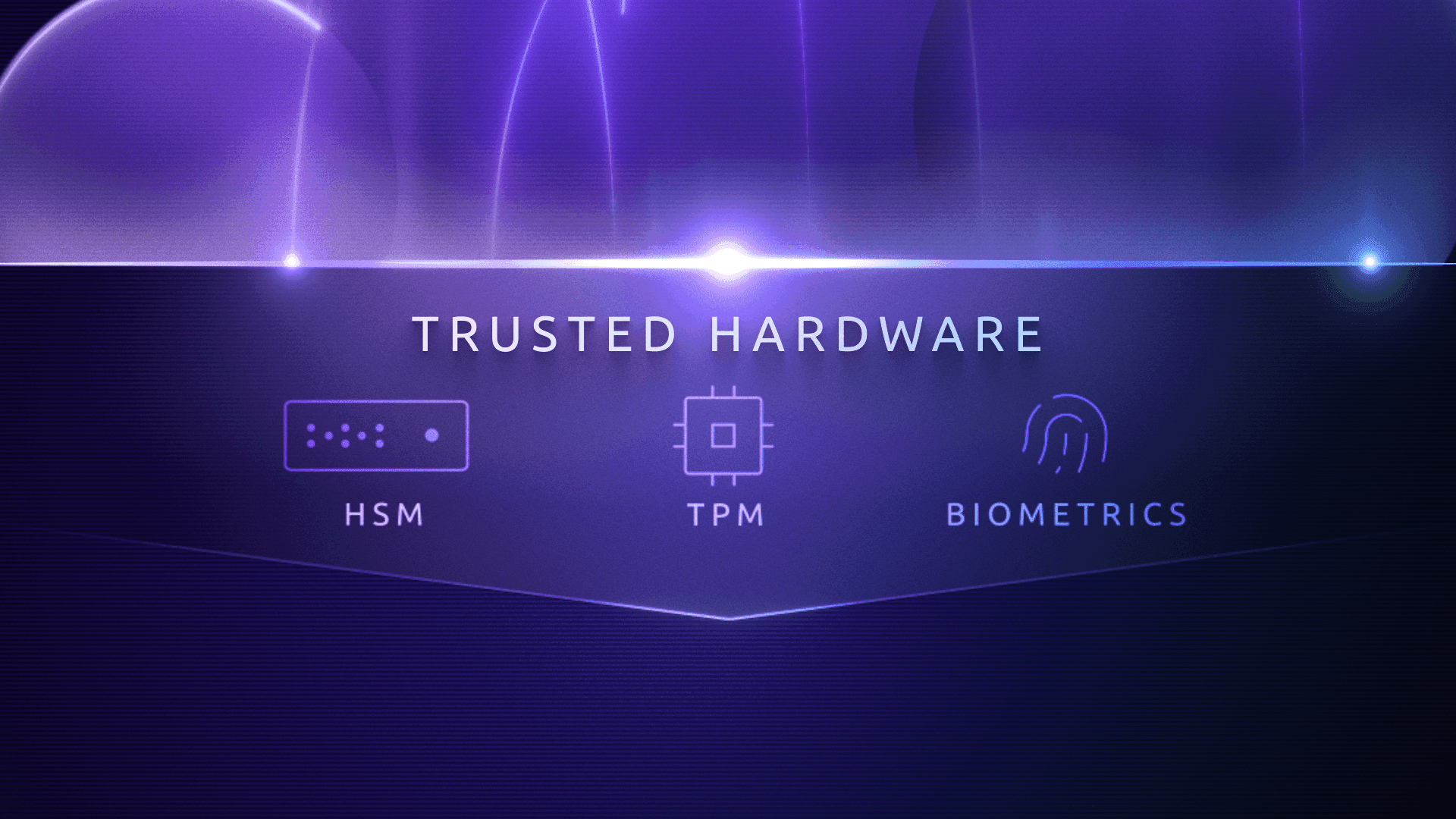
Strong Identity Implementation
Teleport locks down attack surfaces with cryptographic, phishing-resistant identities assigned to users, machines and workloads, devices, resources, and AI (agents and LLMs).
All Teleport identities are backed by a physical-world root of trust: biometrics for humans, secure enclaves (TPM) for machines, and secure hardware (HSM) for workloads. These identities are cryptographically backed, ensuring that they cannot be lost, stolen and shared. The result? Every actor in your infrastructure is a known, trusted identity that cannot be hacked or phished.
Unified Infrastructure Identities
All identities are enrolled in Teleport, creating a unified identity layer for users, machines, devices, agents, and protected resources:
Users: Authenticate users without passwords leveraging biometric devices. Add Teleport as a security layer on top of your identity provider or use Teleport's SSO.
Machines & workloads: Issue and govern identities for your CI/CD automation systems, service accounts and microservices, and agentic AI and LLMs leveraging HSM and KMS.
Devices: Assign identities to enrolled TPM-equipped client devices (laptops, workstations, YubiKeys, and more).
Resources: Assign a cryptographic identity to every application, server, database, and cloud resource. Supports SSH, RDP, databases, K8s, clouds, Model Context Protocol (MCP) and more.
Zero Trust Access Control
Access and governance is based on secretless authentication and ephemeral privileges that expire, further removing standing privileges as a threat vector that can be exploited. Steady state infrastructure, that is infrastructure where there is no active work being performed, becomes immune to threat actors because there is no path in. The risk of “infinite access paths” is remediated, with full visibility into authorization pathways that can be locked down and removed.


Full Visibility with No Anonymous Actors
With full visibility into actors and access events, audit/compliance and forensic investigation becomes a breeze. There are no more anonymous or super-user actors taking actions that obfuscate the data. Teleport simplifies the thorniest access control requirements for major and regional regulatory standards.
A Prerequisite to Securing AI Infrastructure
Learn how Infrastructure Identity lays the foundation for resiliency and
operational efficiency that is needed to securely deploy AI into production environments.
What Our Customers Say
Teleport is a strategic technology partner as they help our joint customers to scale their AWS resources in a secure manner. With Teleport’s Identity-Native Infrastructure Access solution, DevOps Engineers get a frictionless experience managing infrastructure that doesn’t require secrets while implementing zero trust architecture in AWS.
We use Teleport Access Requests in combination with Auth0 to easily manage access to our infrastructure. Prior to Teleport, we manually managed SSH keys and a bastion machine and it was an organizational nightmare.
We used to go through multiple steps just to access cloud resources, and now it happens almost instantly. Our engineers are really happy with the significant improvement in their workflow.
Teleport’s vision for Infrastructure Identity is a game-changer for securing hybrid infrastructure.
Teleport is a strategic technology partner as they help our joint customers to scale their AWS resources in a secure manner. With Teleport’s Identity-Native Infrastructure Access solution, DevOps Engineers get a frictionless experience managing infrastructure that doesn’t require secrets while implementing zero trust architecture in AWS.
We use Teleport Access Requests in combination with Auth0 to easily manage access to our infrastructure. Prior to Teleport, we manually managed SSH keys and a bastion machine and it was an organizational nightmare.
We used to go through multiple steps just to access cloud resources, and now it happens almost instantly. Our engineers are really happy with the significant improvement in their workflow.
Teleport’s vision for Infrastructure Identity is a game-changer for securing hybrid infrastructure.
With Teleport, we were even able to close the Kubernetes API without losing access for our engineers or automation tools. That alone was a huge win.
Teleport allows us to comply with the regulatory hurdles that come with running an international stock exchange. The use of bastion hosts, integration with our identity service and auditing capabilities give us a compliant way to access our internal infrastructure.
The Infrastructure Identity solution from Teleport offers a glimpse into the future of more secure, more resilient, and higher-velocity enterprise computing.
Teleport has made obtaining a FedRAMP-Moderate ATO that much more achievable via their FIPS 140-2 endpoints, ease in integration with our SSO and MFA , and the view into audit logs of remote connection sessions provide the appropriate insight for Continuous Monitoring.
Over the many years of using Teleport, it's been an essential piece of my infrastructure to help secure access, and centralize my infrastructure into one dashboard, without having to jump around… I'm not sure how I could go without it.
With Teleport, we were even able to close the Kubernetes API without losing access for our engineers or automation tools. That alone was a huge win.
Teleport allows us to comply with the regulatory hurdles that come with running an international stock exchange. The use of bastion hosts, integration with our identity service and auditing capabilities give us a compliant way to access our internal infrastructure.
The Infrastructure Identity solution from Teleport offers a glimpse into the future of more secure, more resilient, and higher-velocity enterprise computing.
Teleport has made obtaining a FedRAMP-Moderate ATO that much more achievable via their FIPS 140-2 endpoints, ease in integration with our SSO and MFA , and the view into audit logs of remote connection sessions provide the appropriate insight for Continuous Monitoring.
Over the many years of using Teleport, it's been an essential piece of my infrastructure to help secure access, and centralize my infrastructure into one dashboard, without having to jump around… I'm not sure how I could go without it.
Ready to Teleport?
Frequently Asked Questions
What is a “unified identity layer”?
Teleport implements a unified identity layer by providing cryptographic identities for humans, machines, workloads, endpoints, infrastructure assets, and AI agents from one control plane.
How does Teleport scale to AI?
Teleport extends the same infrastructure identity, access, and governance model it uses for humans and machines to MCP-based AI applications and agentic AI, so AI components use the same secure identity fabric.
Why don’t secrets and credentials scale with AI?
Static credentials create unmanaged, and over-privileged access paths. Teleport eliminates them in favor of short-lived, cryptographic identities for human, machine, and AI actors.
Does Teleport work with my current IdP and cloud providers?
Teleport integrates with major IdPs and cloud IAM systems, including SSO connectors and Identity Governance Integrations that sync roles and Access Lists with AWS IAM Identity Center, Microsoft Entra ID, Okta, and more.
Does Teleport make audits and investigations simpler?
Teleport centralizes logs, visualizes identity-to-resource access with Access Graph and dashboards, and provides tools like SQL Editor to quickly answer audit questions about who accessed what, when, and how.











