Home - Teleport Blog - How Crypto Companies Can Break the Breach Cycle
How Crypto Companies Can Break the Breach Cycle
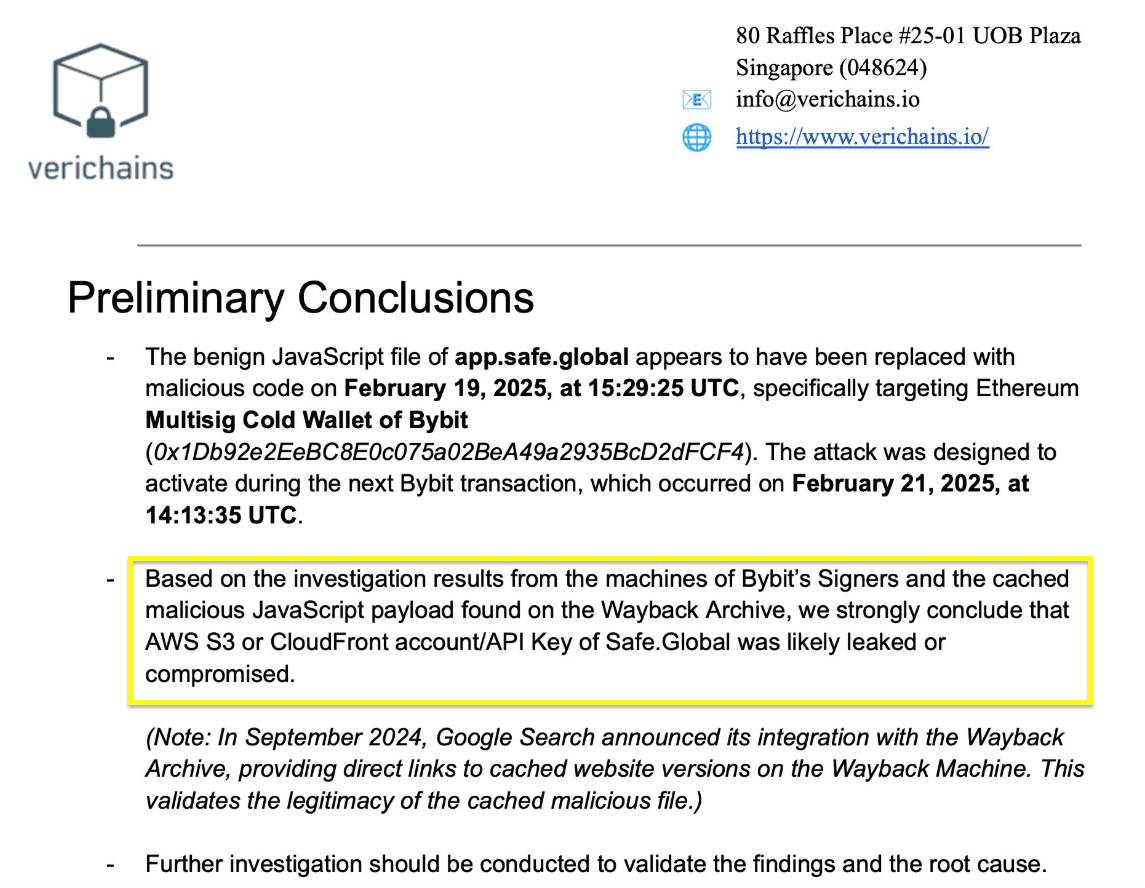
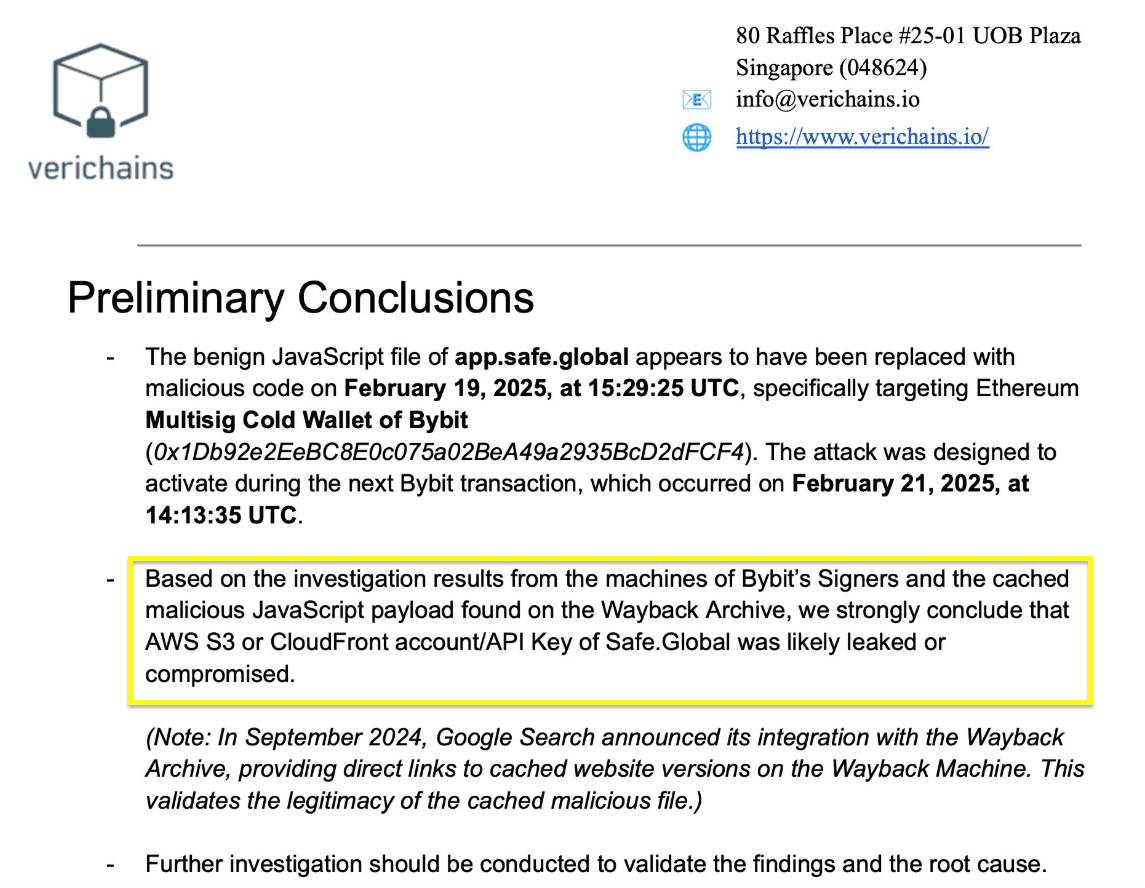
In February of 2025, North Korean state-backed cybercriminals stole over $1.9 billion from a popular crypto exchange.
That's a mind-boggling amount of money, let alone from a breach. But here's the craziest part; it was excruciatingly simple. In short, it went down like this: an engineer was phished, attackers located static API keys — and just like that, attackers had direct access to critical cloud resources.
Static credentials strike again. This same story keeps playing out over and over again, while the damages steadily increase from millions to Billions (with a capital B for emphasis). At this point, it's more novel to learn about a breach that didn't abuse static credentials or stale privileges to access critical infrastructure.
In this blog, we'll examine why this keeps happening (even as the stakes grow higher and higher) and what crypto exchanges and crypto-focused organizations can do about it — while increasing engineer velocity in the process.
Traditional security models are failing everyone
Let's quickly define traditional security models. We are referring to models where security for compute/storage/networking resources are individually configured, deployments are discrete and staged, and the overall focus is on employee lifecycle management for hardware, software, and network resources. Historically, this approach to security has been carried out by IT administrators to support perimeter-based IT environments.
Crypto companies, like many other organizations with a modern infrastructure environment, are constantly provisioning and scaling new resources, often automatically. These deployments are elastic, ephemeral, and highly dynamic, making it near-impossible to enforce consistent security policies across everything as it scales up or down.
Adapting traditional security measures across this complex and constantly evolving infrastructure often requires restrictive or manually-intensive request/approval processes. That's a problem for both security and engineering teams.
Complex infrastructure meets pressure cooker deadlines
Things move quickly in the crypto industry. Organizations need to be ready to adapt and respond to things like market events or regulatory changes at the drop of a hat. As a result, engineers in the crypto industry are under intense pressure to meet time-to-market objectives. Delays in access can leave critical projects dead in the water.
Traditional security models were not designed for the scale, speed, and complexity of the high-tech infrastructure crypto organizations rely on. They are focused on employee-level, IT-centric concerns like users, devices, and applications — not on supporting the break-neck pace of modern engineering.
Square peg, round hole.
Death by a thousand logins
The results can be toxic. The same engineers responsible for delivering innovation are forced to stop what they're doing, remember the right VPN for the resource they need, and request elevated permissions — and even then, must wait for a human in IT to review and approve the request. All to do their daily work.
We know engineers need to move fast. But when processes slow them down, they go around the roadblock (they're engineers; that's what they do). Even at organizations like crypto exchanges, where security and auditability is critical, shadow access and static credential threats are constantly being perpetrated. Developers may hardcode an API token into a script, or leave an SSH key backdoor open — all just to circumvent the outdated or overly complicated approval process standing in their way.
At best, productivity suffers. At worst, you are essentially handing a blank check to a cybercriminal (or nation-state agent).
Break the breach cycle and turbocharge engineer velocity
As long as credentials exist, they can be stolen. As long as cumbersome access requests stand in the way of engineers doing their job, standing privileges and shadow access will proliferate.
The fix is simple: make engineer access requests trusted AND effortless. That's where Teleport comes in.
Teleport consolidates cryptographic identities backed by real world attributes (biometrics, secure enclaves, TPM) that cannot be stolen or lost. Elaborate, credential-based access request workflows are replaced with task-based, short-lived privileges designed to quickly grant engineers and developers access to the resources they need to keep projects moving.
By removing static credentials, standing privileges, and anonymous identities from the access chain, the effectiveness and blast radius of identity attacks — and common crypto threats like breach and pivot attacks — are significantly reduced.
- Unified cryptographic identities for all humans and machines: No passwords, no secrets, no API keys to steal.
- Zero trust for every connection: Every connection is secured with encryption.
- Least privilege by default: Access is granted to the right resources at the right time based on tasks that need to be completed.
- Identity and policy governance: Provides a single source of trust for audit to prove nothing has changed in your security posture.
With Teleport, forward-thinking crypto organizations, including cryptocurrency exchanges, blockchain developers, and coin trading platforms, can achieve unified cryptographic identity across their entire infrastructure, ensuring secure, high-velocity development and uncompromising compliance.
Learn more about how Teleport solves critical infrastructure, engineering, and compliance challenges for crypto organizations — and why we're trusted by three of the top five crypto exchanges by trading volume.
Learn More
Future-proof your crypto infrastructure. Request a Teleport demo today to see how cryptographic identities eliminate credential risks and enable zero trust security.
Request a Demo
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter