Identify & Mitigate Shadow Access Risks

Trusted by Market Leaders
















Shadow access creates infrastructure risk
Shadow access — the use of backdoor or ungoverned access routes to infrastructure, data, and applications — jeopardizes the security of your infrastructure.
Unmanaged static credentials like passwords, SSH keys, and API keys, along with orphaned or service accounts pose significant security risk.
Used by engineers to easily get to the systems they need, shadow access risks increase exponentially as your infrastructure expands.
Eliminate shadow access at its source
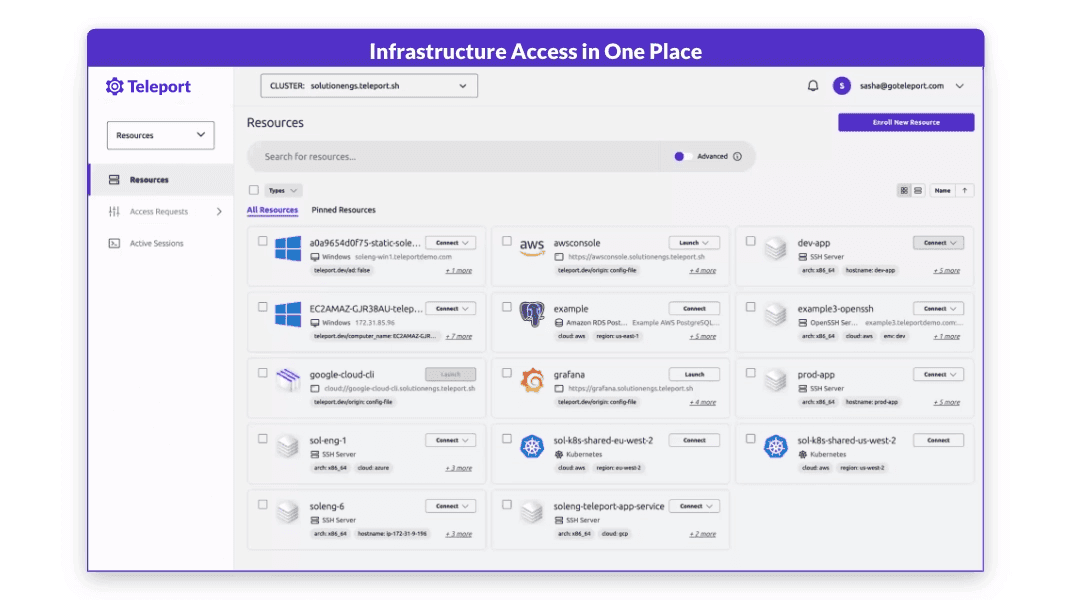
Teleport makes infrastructure access effortless so engineers don't resort to insecure practices or backdoors.
Eliminate anonymous and overprivileged access by removing the use of credentials like SSH keys and API keys entirely. Illuminate shadow access risks like ungoverned credentials, keys, and accounts across your infrastructure.
Accelerate engineering productivity
Engineers utilize shadow access when they can’t get quick access to the resources they need or to solve urgent problems.
Teleport eliminates the need to resort to shadow access pathways and backdoors by making it effortless for engineers to get access to the resources they need, right when they need it.
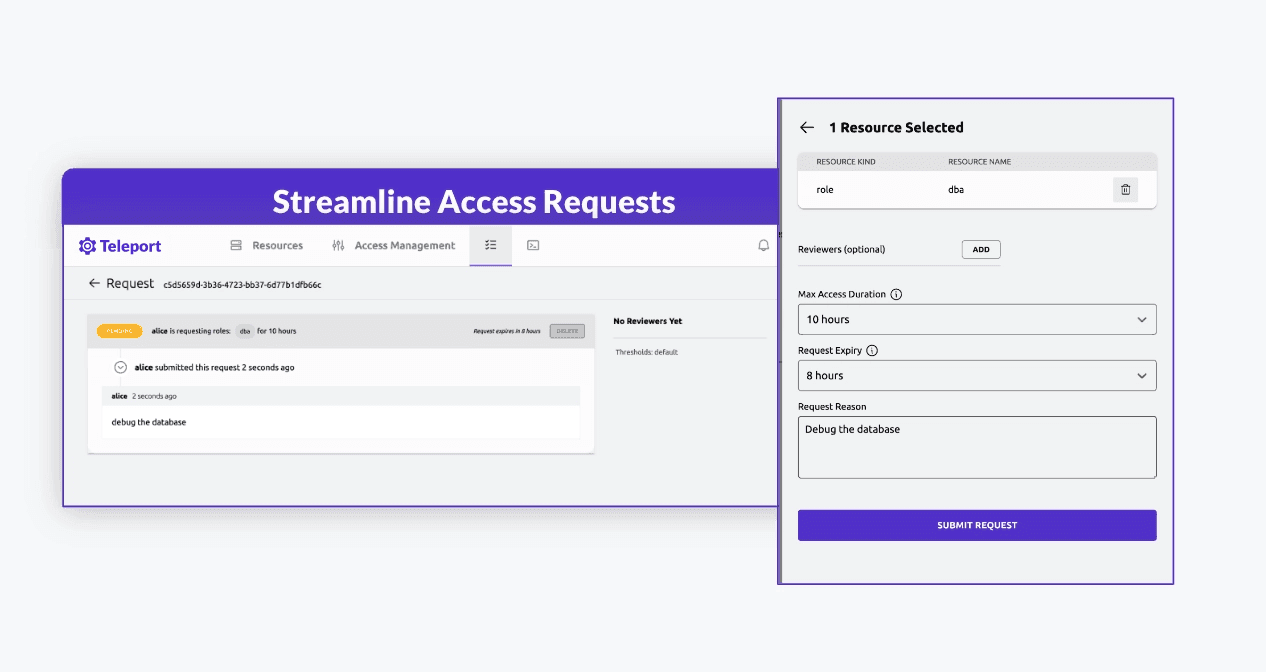
Prevent backdoor risks
Make it simple for engineers to request just-in-time access based on tasks, eliminating the primary motive for creating backdoors.
Eliminate static credentials
Shrink your attack surface by getting rid of credential sprawl and enforcing granular, least privileged access.
Identify and mitigate risks
Find SSH keys, standing privileges, and other risky access paths in your infrastructure — and ensure access policies are enforced at all times.
Just-in-time access for engineers
Render backdoor access paths useless
Engineers want speed — not complicated access processes. When it becomes quick and effortless to access the resources they need, the use of backdoor access paths becomes moot.
Teleport uncomplicates access by providing role-based, just-in-time access for engineers, unified across everything they access — and only for the duration of the task at hand.
Eliminate static credentials as an attack vector
Replace credentials with short-lived certificates
Static credentials can be shared between team members, embedded in source code repositories, or simply misplaced — exposing your infrastructure to unnecessary risk.
Eliminate the inherent risks of passwords, SSH keys, and API tokens with short-lived certificates — shutting down the most common sources of shadow access vulnerabilities at their origin.
Identify and lock down hidden access paths
Enforce identity security in real-time
View a real-time inventory of all users, machines, workloads, and access points across your entire infrastructure. Visualize, monitor, and easily eliminate shadow access threats before they occur.
Lock down hidden backdoors, eliminate undocumented or unauthorized access vectors from SSH or API keys, and ensure policies are followed to the letter without compromise.