Home - Teleport Blog - Trusted Computing: The Role of Infrastructure IAM
Trusted Computing: The Role of Infrastructure IAM
This blog is a guest contribution from Simon Moffatt, founder of The Cyber Hut.
The role of trust for both employees and customers has come under increased scrutiny in the past decade. The rise of concepts such as zero trust for the workforce and the privacy/personalisation paradox for customers has moved trust from being an exercise in academic rigour, to one which has realigned enterprise security architecture choices.
With the growing need for a flexible and responsive computing fabric, the concept of trust has emerged wholeheartedly in the infrastructure management arena too. Organisations wish to deliver storage, network and processing capabilities at the speed of business - with an assumption that this foundation is based upon a Trusted Computing paradigm.
This paradigm reduces all forms of anonymous access and left-shifts assurance to the start of any authentication event and access request for both humans and non-humans. This requires concepts such as software attestation - making sure software of a known origin is loaded in the right order, at the right time - as well as using cryptographic challenge response processes for all authentication events based on now widely accepted standards and availability of trusted platform modules.
These shifts now allow “trust” to extend beyond data and applications right the way down to the infrastructure that delivers those applications and services.
But infrastructure management and the protection of it has become complex - with the impact of getting it wrong higher than ever before.
Perfect Storm of Vulnerability and Impact
→ Broad infrastructure usage and support needs
→ Requirements for agility, responsive and infrastructure-as-a-code
→ Infrastructure now an adversarial attack vector
Infrastructure today is not limited to on premises physical servers, with outsourced maintenance contracts. Data processing, security and connectivity infrastructure is abstracted using multiple levels of service delivery - supporting an array of applications, APIs and business-led functions. These functions are based upon foundations located in cloud service providers (CSP), containerization environments such as Kubernetes (K8) as well as a range of historically significant approaches using virtualization and *nix operating systems.
The management of such a diverse array of components requires expertise in a wide body of tools, frameworks and technologies. This can lead to inconsistencies in delivery time, risk management and integration functions. This inconsistency is providing a foundation for external adversarial activity in their aims to leverage this infrastructure as a major attack vector. An attack vector used for future lateral movement, data exfiltration and denial of service campaigns.
Complication: Point solutions of PAM & NHI
→ Legacy PAM becomes isolated and difficult to utilise
→ NHI focused on more specialised use cases
→ DIY becomes difficult to scale repeatably
The secure management of core infrastructure is not new. Privileged Access Management (PAM) has a long history of providing capabilities such as credential vaulting, session monitoring, request workflows and auditing for a range of systems such as databases, core directories, FTP and other point-services.
However PAM can often be isolated in its design paradigm - especially as more recent changes in how infrastructure is delivered do not always fit into specific on premises resource-centric ways of thinking. PAM integrations are complex and were often designed for proprietary system integration, with rigid provisioning flows and access principles. PAM wasn’t designed to scale rapidly or assume concepts like non-human access, API-first interactions or cloud-deployed services.
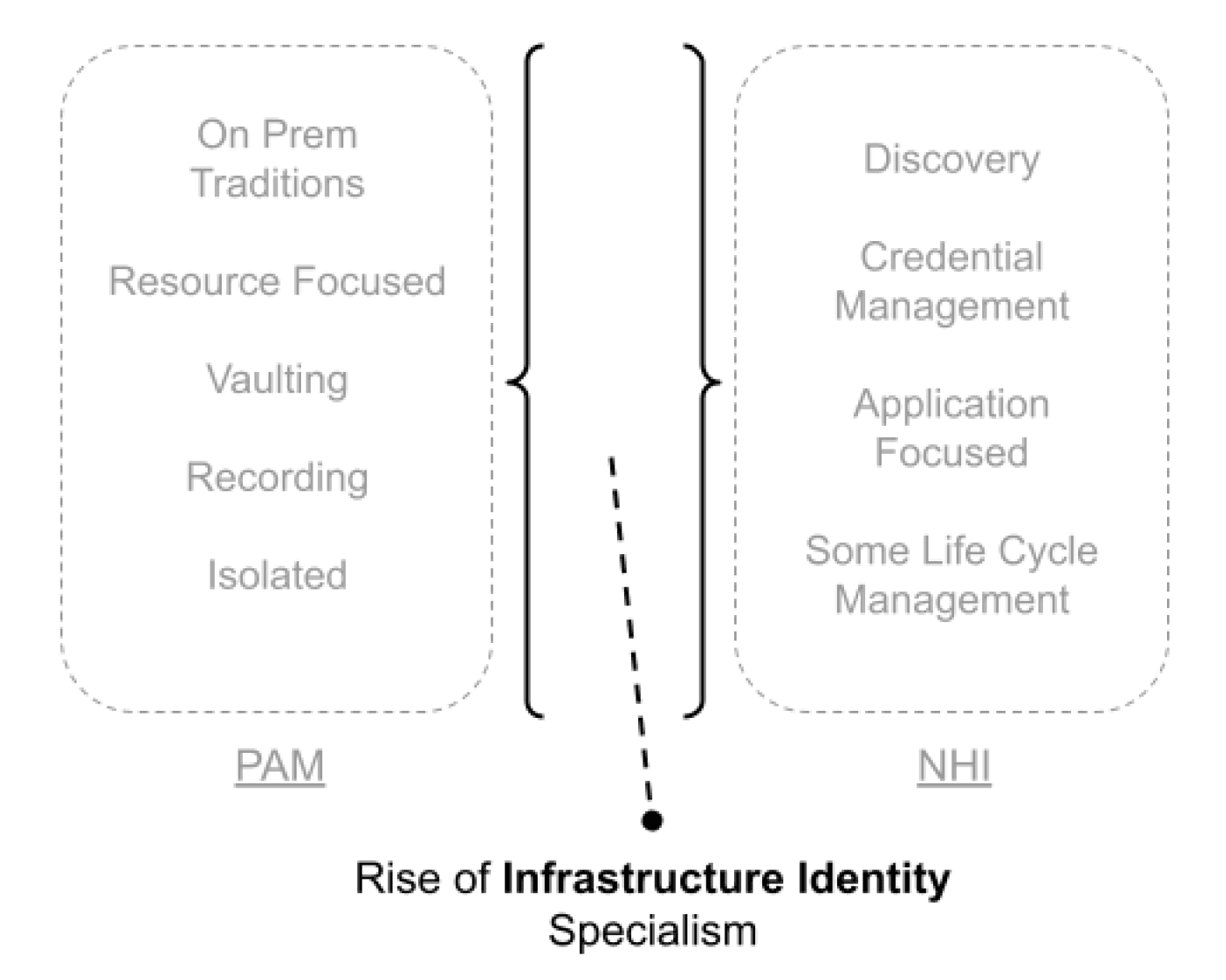
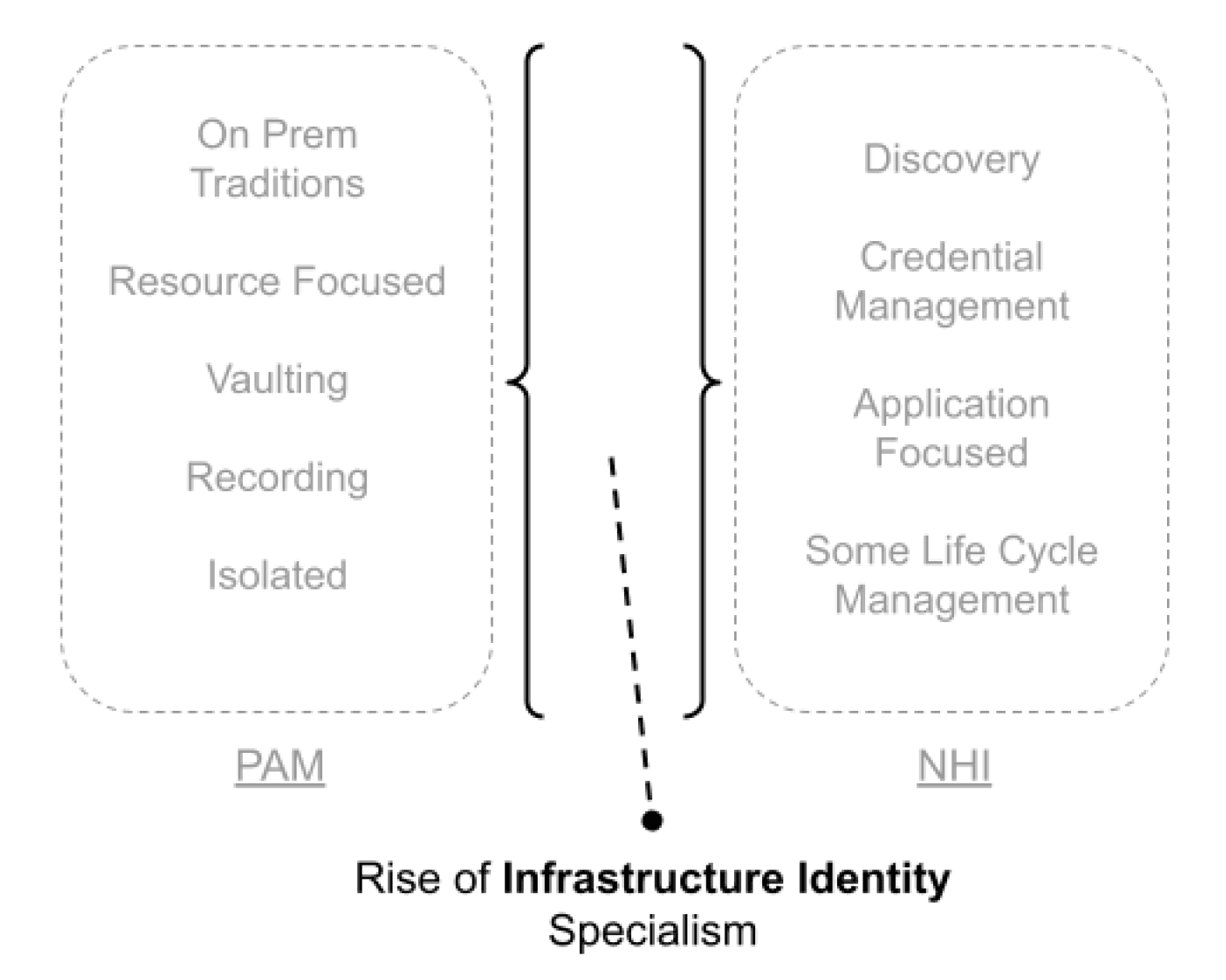
The rise in programmatic access, workloads and non-human identities (NHI) has seen the emergence of a dedicated sector - with discovery, credential management and governance all becoming rapidly available. As PAM products may have significant weakness when it comes to managing NHIs, NHI platforms may themselves be not primarily-focused on the specific needs of infrastructure identity management.
Just as dedicated platforms have developed in the past decade to manage the risk and usability of external customer identity, so too are we seeing the need for platforms and features that support specific infrastructure identity use cases.
Implication: Productivity Reduced & Risk Increases
→ Engineering effort increases
→ Audit efficiency and security reduced
→ Business agility reduced
The increased reliance on concepts such as infrastructure-as-code and remote access to third-party cloud-delivered components has introduced new personae to this management head-ache - each with different challenges and metrics for success.
From engineering to system administration, security to cloud operations, more effort is needed to deliver infrastructure components in both a resilient and secure manner. By having multiple isolated systems - be they DIY, PAM or NHI focused, siloes develop which not only impacts security and risk management, but also introduces inefficiency from an architecture, support and management point of view. Separate solutions - even without consideration for custom designs - will impact the ability to view holistically the audit and compliance posture.
Who has access to what? Who accessed what? When and why were root-level permissions issued and what was performed with them? Can those journeys be easily linked to malicious behaviour or data exfoliation cases? Audit, compliance and forensics investigations are all hampered by this and will likely spend wasted effort on producing usable data and reports.
But these core infrastructure systems for data storage, network routing, compute power, AI support tools and serverless functions are essential. They are not “nice to haves” and ineffective ways of delivering them to applications that rely upon them, will have a tangible impact on business agility and service delivery.
Solution: Infrastructure Risk as a Spectrum
→ What
⬩ Assurance of all infrastructure access paths
⬩ Identities for People, Machines and Workloads
⬩ Removal of anonymous interactions
⬩ Consistent across all infrastructure components
→ How
⬩ Identification of access, identities and routes
⬩ Consistent strong authentication for people and workloads
⬩ Design and enforcement of policy
⬩ Broad coverage of integration - proxies, native protocols
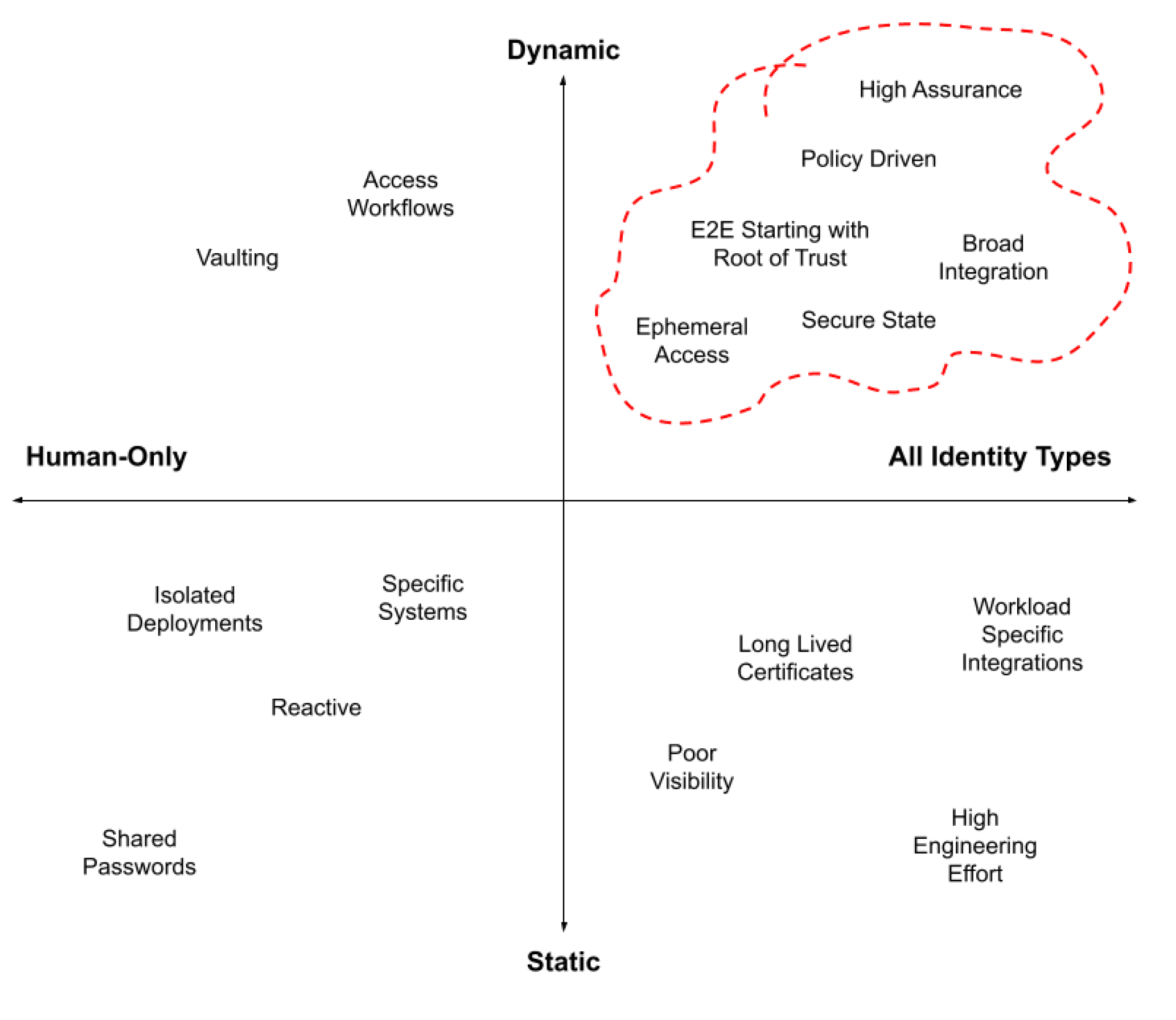
The traditional view of PAM was to target specific high risk users, systems and the associated access paths. In environments that were more controlled, with fewer deployment options and only human-centric identities this delivered a modicum of success. Today, however, we need to take those initial design wins, enhanced with concepts from zero trust and identity security such as consistent policy, strong authentication and continuous verification to deliver a broader and more risk-led infrastructure management approach.
End-to-end assurance for all entry points into all infrastructure components requires specialist tools and frameworks. A movement from static and reactive models of managing access is taking place that incorporates multiple identity types including workloads and programmatic access. It is important to be able to discover and understand the location and origin of requests into the infrastructure management plane - including identity types, access needs and the associated ways in which credentials and permissions are managed. Once identified they can be secured - authenticated using cryptographic identities and software that is attested using a root of trust.
A policy based approach that supports consistent assurance across a range of protected systems allows for simpler ways to respond to change - be that change with respect to business applications, infrastructure needs and the identities making those changes. The end goal is a secure running environment that can only be changed by the appropriately approved entry points into those environments by a gatekeeper model.
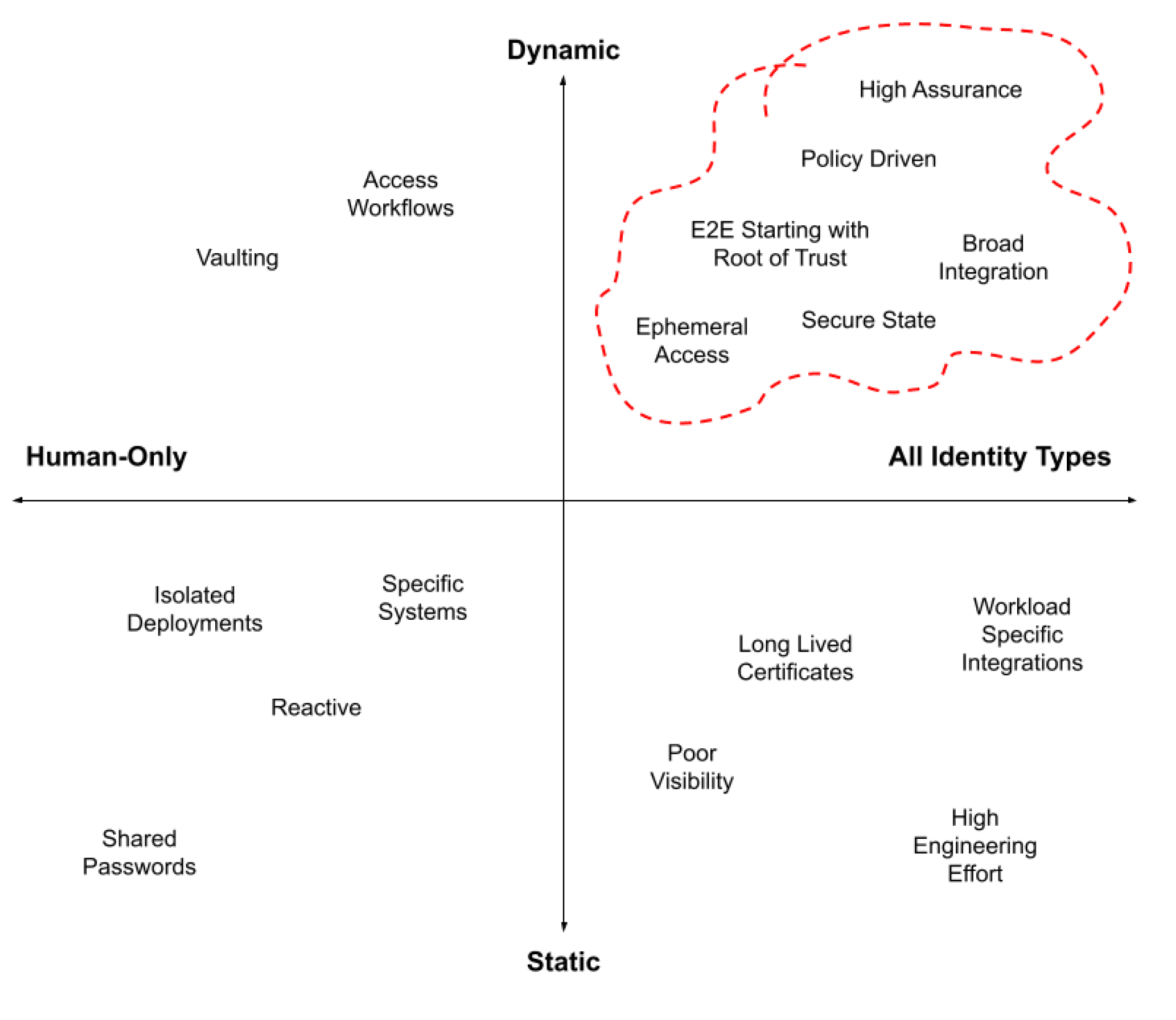
Benefits: Delivery of Flexible Trusted Computing
As with concepts such as zero trust and identity security, a broader integration coverage model that includes multiple identity types and specialist object protection will result in higher security and reduced risk. We start to move to a continuous security approach where all interactions are firstly known and understood, but secondly the appropriate controls and friction can be applied - irrespective of whether the access is based on human-centric or machine based interactions.
Ephemeral access principles for both credentials and also permissions reduces the blast radius of any “breach” but also helps move towards a reduction in operational overhead. Policy-by-design improves risk visibility and allows stakeholders from engineering, operations and infrastructure to transfer both effort and risk to a central specialist function.
→ Security Increases
⬩ ZT for infrastructure
• Continuous control and reduced blast radius
• Least privileged and ephemeral access
• Risk visibility increases
→ Productivity Increases
⬩ Engineering effort reduces
⬩ Access request/review process automated
⬩ Audit and compliance streamlined
→ Improved Business Agility
⬩ Tooling consolidation
⬩ More responsive to change
Getting Started
Moving to an infrastructure-identity model requires a good understanding of the current problem statement, before designing a target profile. What tools are in place currently? What identity types are involved? Where are they located and what permissions and credentials are currently being used?
The analysis of the existing environment will require stakeholder engagement with engineering, security and operations teams. As with any transformation that involves the creation of new categories, process, technology and people will be required to change. Start small and build a strategic vision of what infrastructure security goals need delivering.
→ Understand problem statement
⬩ Visibility, assessment, tools, process
→ Stakeholder discussions
⬩ Engineering, Security & Cloud Operations
→ Start small and expand
⬩ Time and progress adoption
⬩ Leverage standards, cryptographic identities, root of trust
About The Author
Simon Moffatt has nearly 25 years experience in IAM, cyber and identity security. He is founder of The Cyber Hut - a specialist research and advisory firm based out of the UK. He is author of CIAM Design Fundamentals and IAM at 2035: A Future Guide to Identity Security. He is a Fellow of the Chartered Institute of Information Security, a regular keynote speaker and a strategic advisor to entities in the public and private sectors.
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter