Home - Teleport Blog - Investigate Amazon EKS Audit Logs with Teleport Identity Security
Investigate Amazon EKS Audit Logs with Teleport Identity Security
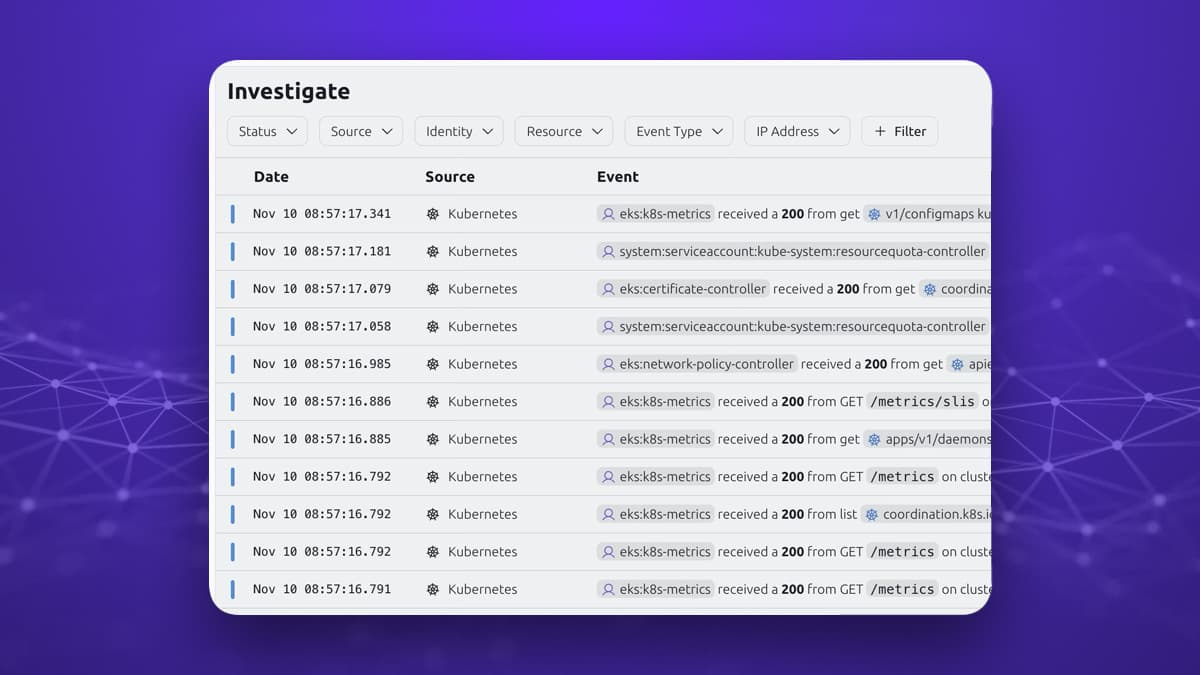
In Teleport 18, we’ve added official support to import Amazon EKS Audit Logs into Teleport Identity Security. This capability allows teams to have visibility into actions performed on Amazon EKS clusters when those actions were not executed via Teleport.
Amazon EKS Audit Logs in Teleport Identity Security will be generally available in Teleport 18.3, coming November 2025.
Investigating Shadow Access in Amazon EKS
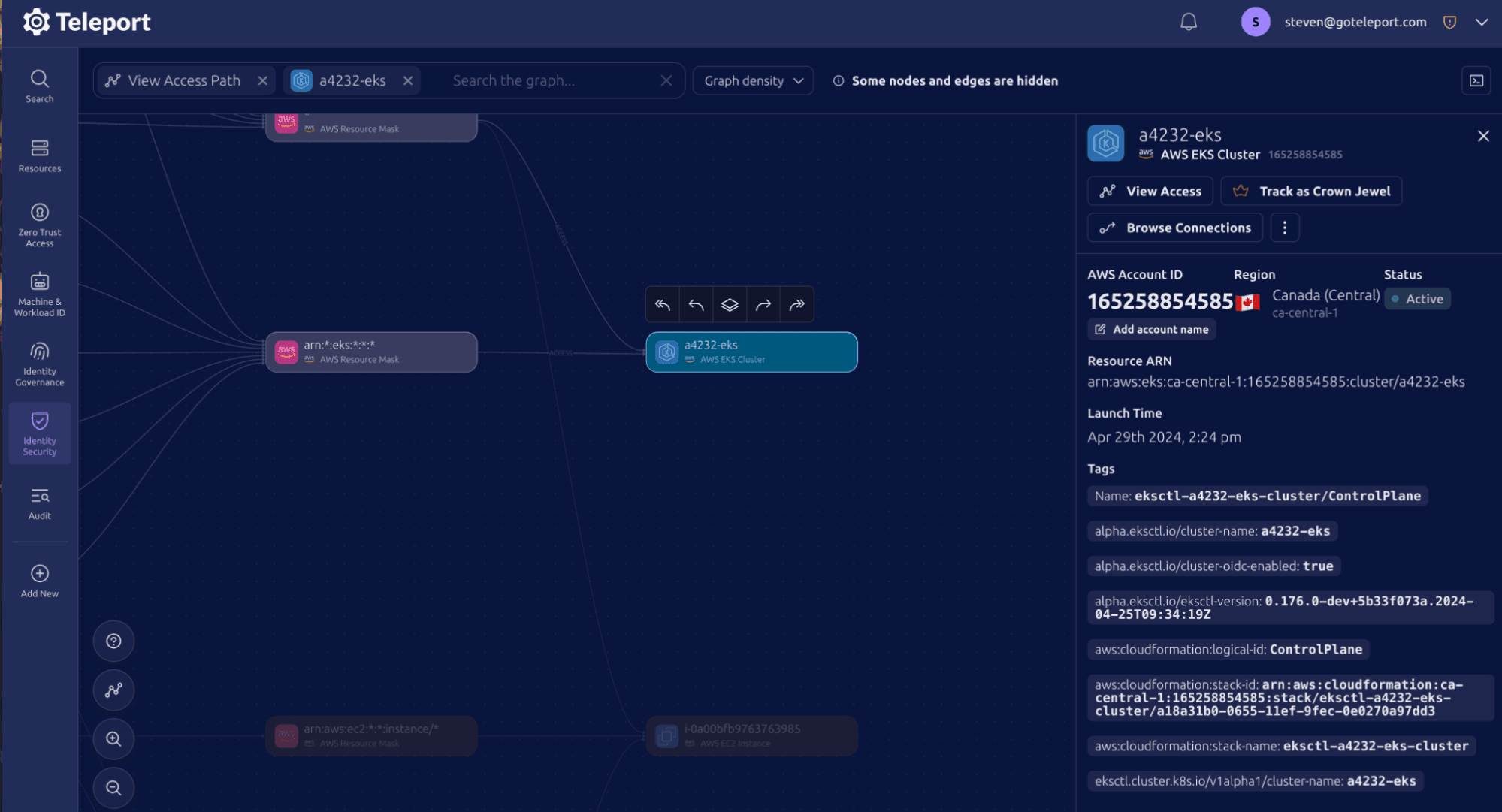
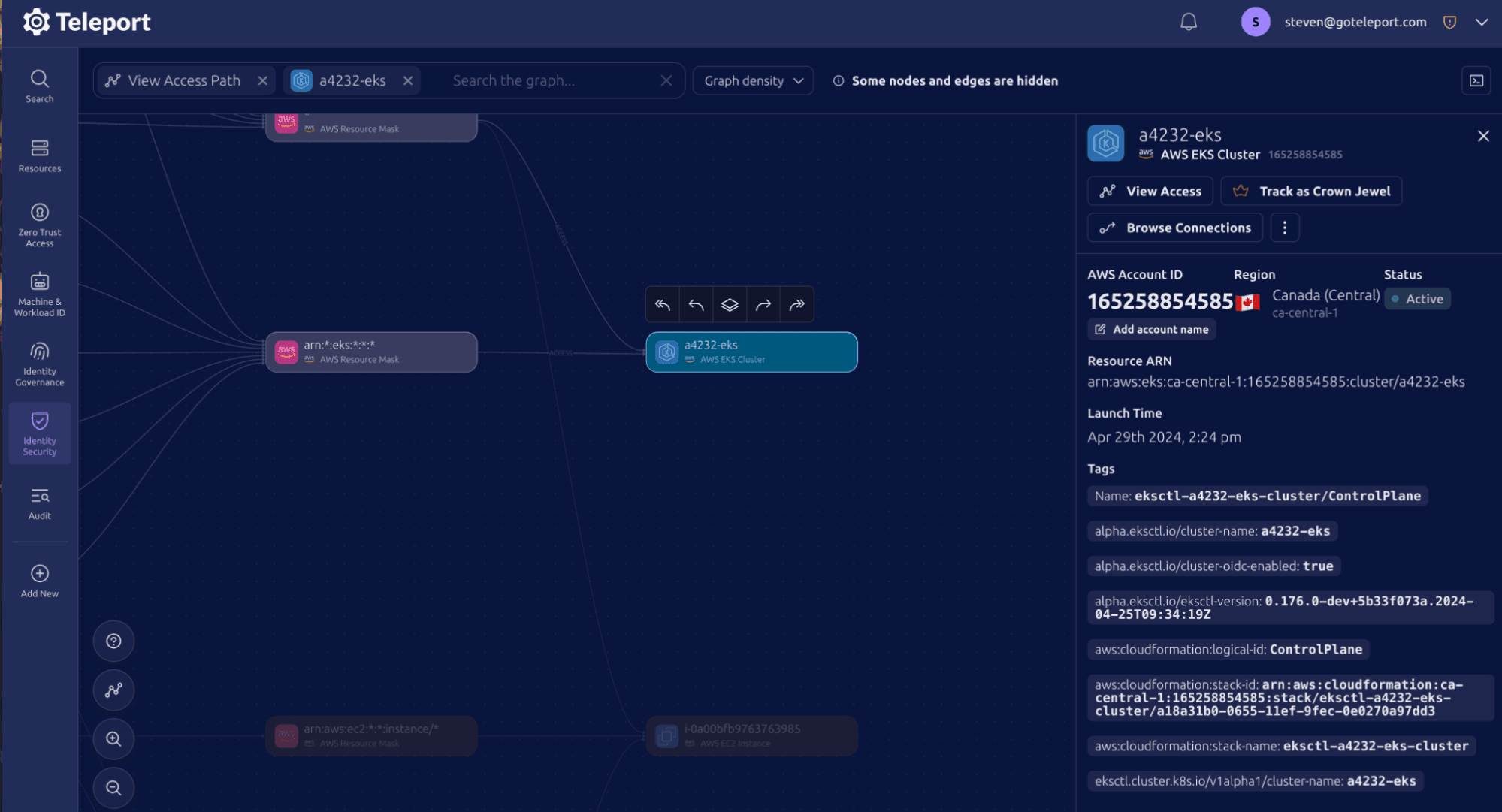
Earlier this year the Teleport Identity Security team conducted a red-blue team exercise to test Teleport Security Investigation capabilities, launched in Teleport 18. A snippet of the video is below, starting at 7:45 to understand the issue. The TLDR: Once a malicious user has a valid Kubernetes EKS cert, they were able to hop around the name space and eventually added a reverse shell to circumvent Teleport. Without the EKS logs, we lacked visibility into this shadow access. Teams can now view access from Teleport, Service Accounts and IAM Roles from one unified view. This new addition makes it easier to track down suspicious activity.
Teams can track actions from authentication to workloads.
Once the Amazon EKS Audit log addition has been added, it’s now possible to correlate activity from Teleport Kubernetes Access to activity on the EKS node.
Setting Up Amazon EKS Audit Log in Teleport Identity Security
To set up Amazon EKS Audit Log we recommend following the official documentation, but these are the steps you can expect:
- Configure EKS to export audit logs
- (Optional but recommended) Add EKS nodes into Teleport using our Amazon AWS integration.
- Add Amazon EKS Audit Log integration
- Start a test session.
tsh kube login, thenkubectl get pods
Demo Video
Key Capabilities
Audit Log Collection & Analysis
- Real-time streaming of Kubernetes API server audit logs from EKS clusters via CloudWatch Metrics
- Automatic discovery and monitoring of EKS clusters in your AWS environment
- Processing and storage of audit events in Teleport Identity Security for analysis
Enhanced Visibility
- Track all API interactions within EKS clusters, including kubectl commands, service account activities, and API calls and requests
- Monitor user access patterns and identify potential security risks
- Know who’s kubectl exec into Pods
- Support for impersonated user tracking (when available in audit logs)
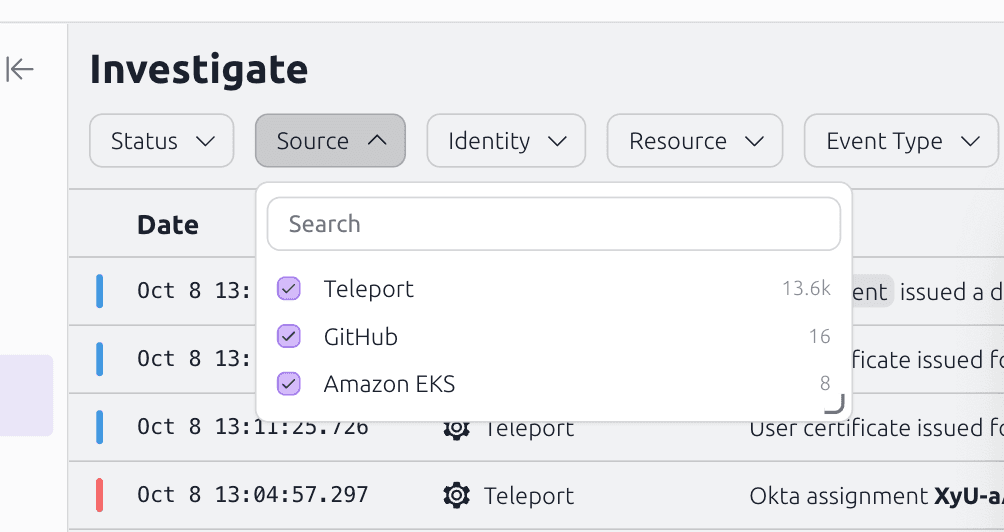
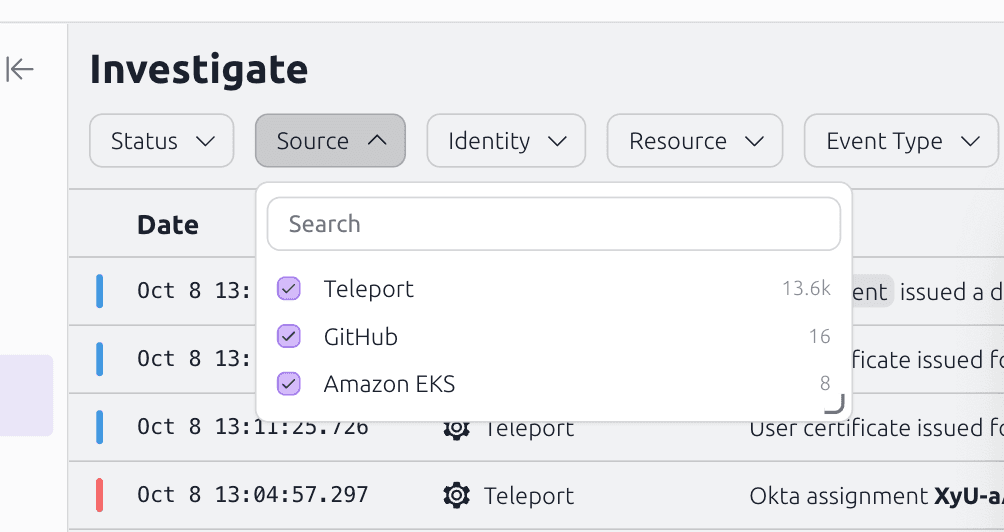
- Easily group Teleport EKS activity with Amazon EKS Audit Logs
- Correlate EKS logs alongside CloudTrail
Try Amazon EKS Audit Logs in Teleport Identity Security
This feature is available in Teleport 18 for customers with Teleport Identity Security. It’s coming soon to Teleport Enterprise Cloud. If you would like a demo, please reach out to us.
To get started with Teleport Identity Security, you can start a free trial of Teleport Enterprise or reach out to our sales team.
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter