Home - Teleport Blog - Why DevSecOps is Going Passwordless
Why DevSecOps is Going Passwordless
I talk to a lot of engineers every day. SREs. Systems Architects. Security Engineers. What I am hearing from them is that they are moving away from passwords — both in their personal lives, opting for more secure forms of authentication like biometrics and second factors, and at work. It just doesn’t make sense anymore to protect your personal bank with a second factor, but to share around an SSH key to access critical server infrastructure.
Passwords are still the leading way to grant access to infrastructure, even though stolen or hacked credentials are the number one cause of data breaches.
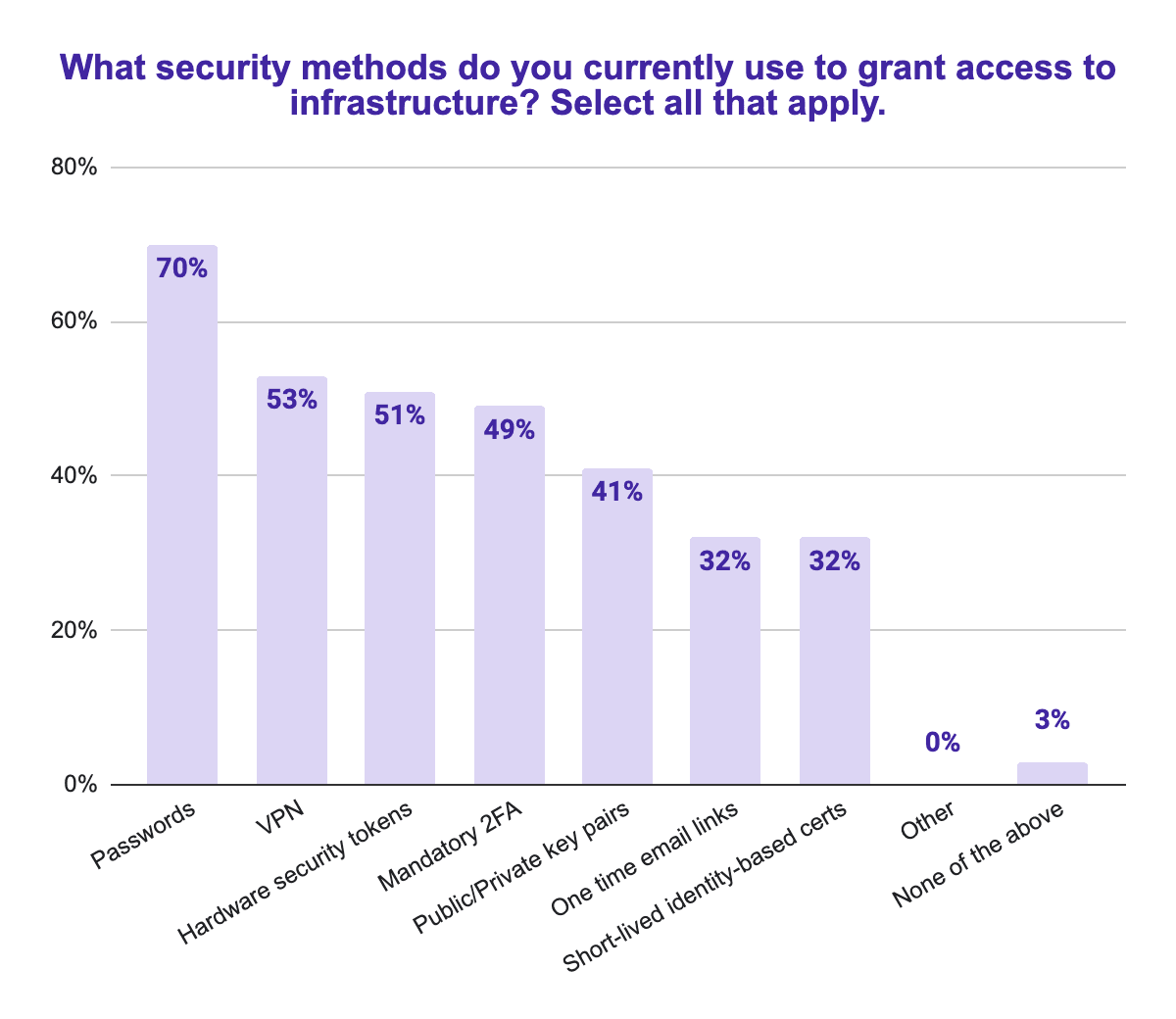
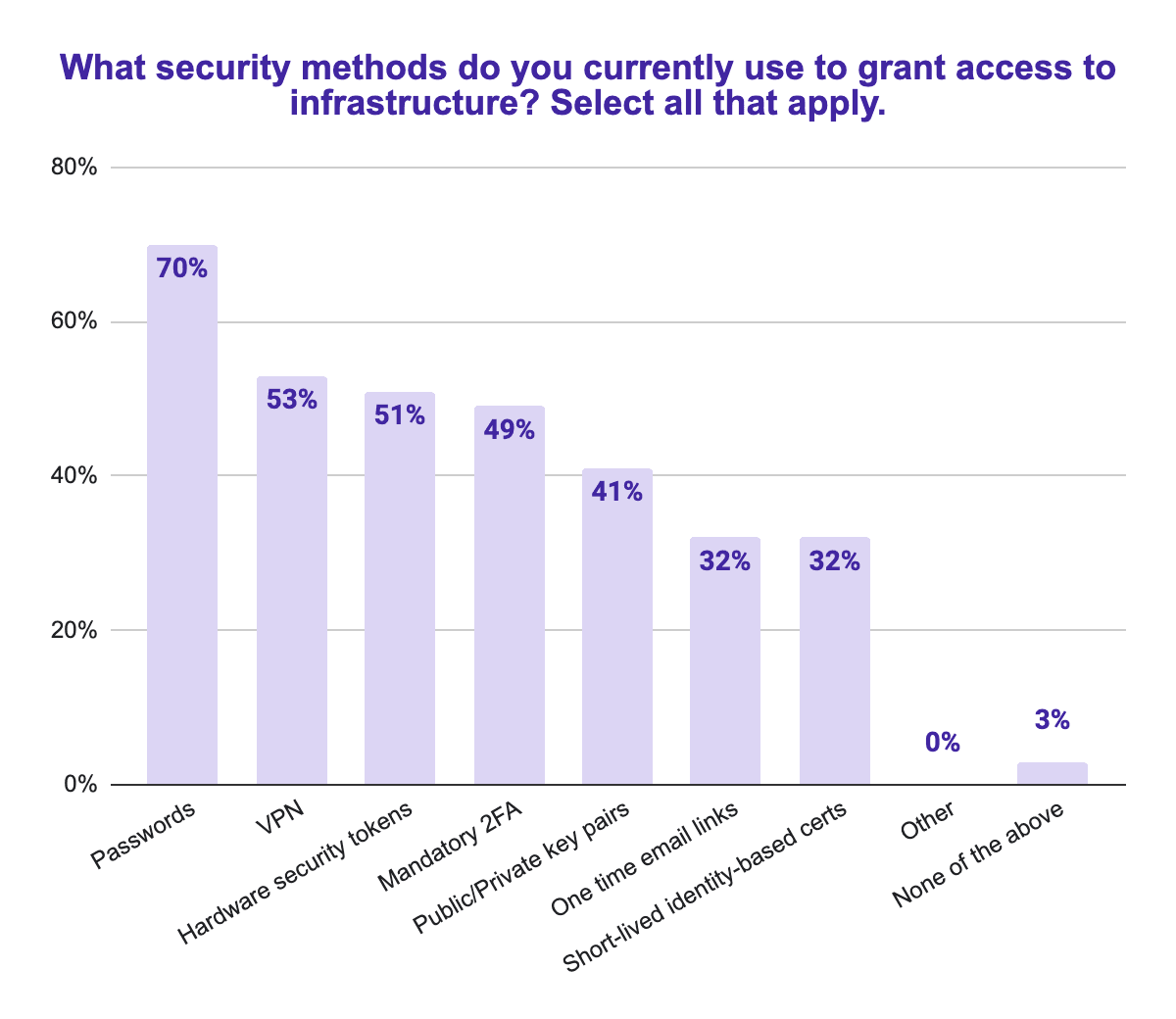
But this is changing. Look at the 32% of respondents in our recent The State of Infrastructure Access & Security Report 2021. We surveyed 1000 IT, DevOps and Security professionals to find out what they were thinking about some of the most important security issues at the moment.
Short-lived identity-based certificates are a small part of the overall security toolkit today, but they are rightly seen as superior to SSH keys and other shared credentials that are just passwords by another name.
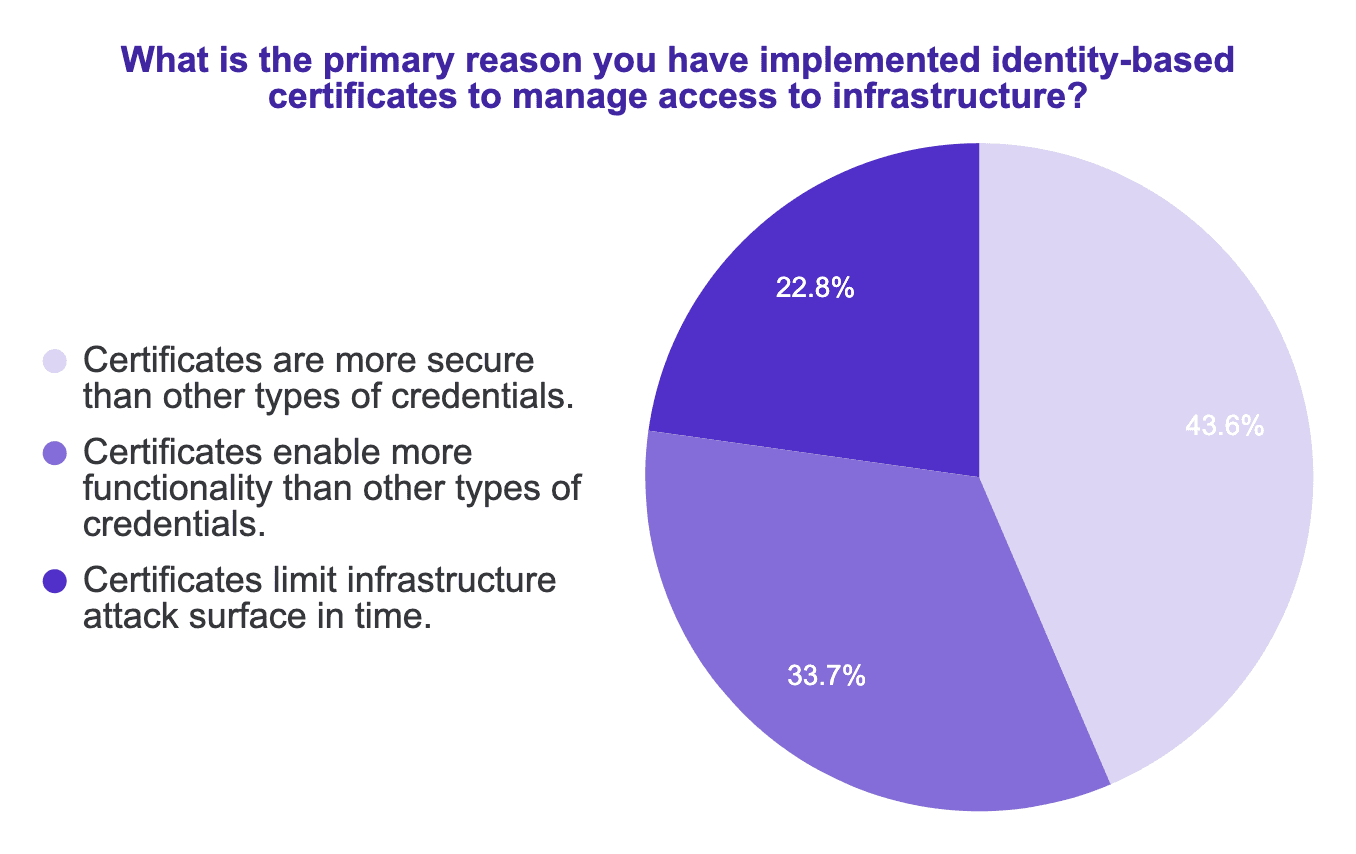
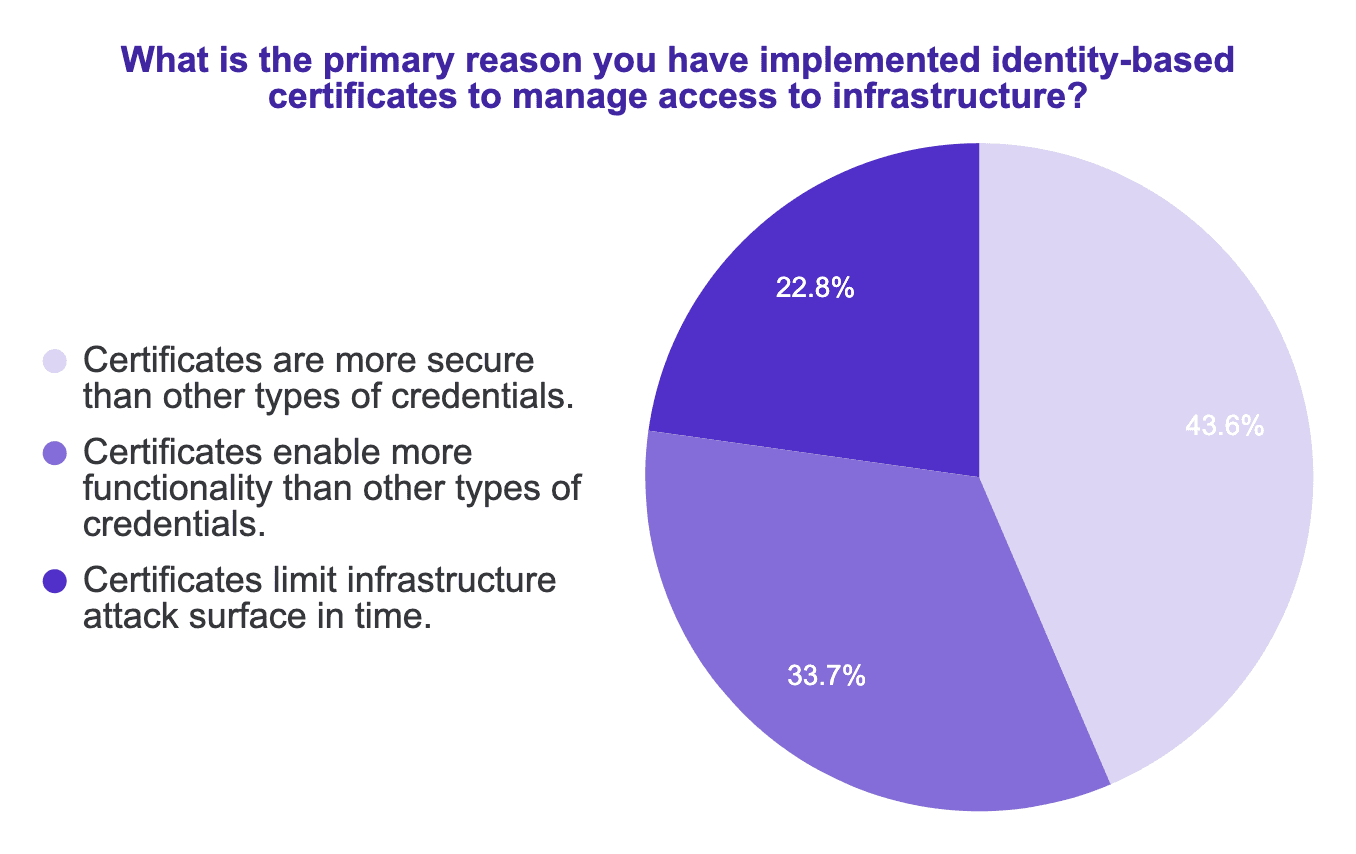
When asked why they had implemented certificates, people said that they were more secure, more feature-rich, and limited the attack surface in time.
Teleport cybersecurity blog posts and tech news
Every other week we'll send a newsletter with the latest cybersecurity news and Teleport updates.
All of this is why 77% of companies view moving towards a passwordless infrastructure as “very important” or “important”. In case you are wondering, they are also adopting zero-trust networks (86%) and just-in-time infrastructure access (89%).
Are you currently implementing passwordless access for your infrastructure? If so, we’d love to help. Reach out and one of our expert solution engineers will help you architect the solution in a way that is not only more secure, but also more agile.
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter