Home - Teleport Blog - What is a VPN? Types of VPNs and How They Work
What is a VPN? Types of VPNs and How They Work
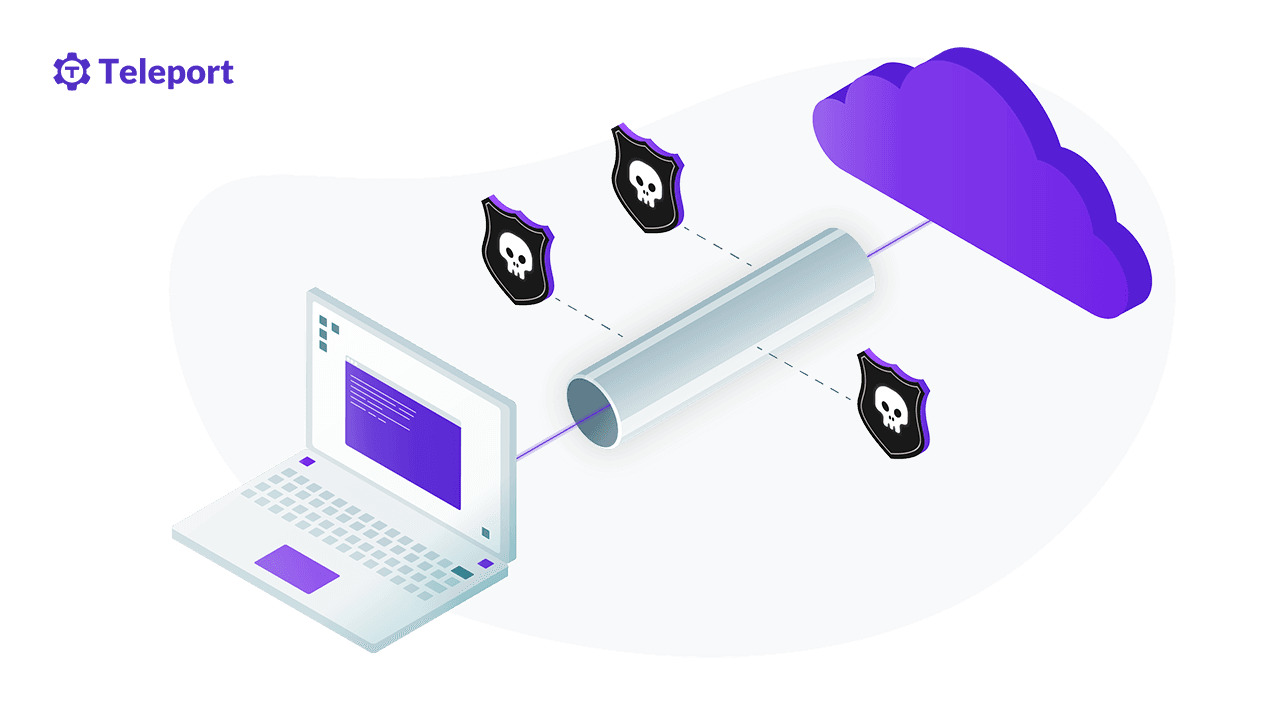
As the number of remote workers grows, virtual private networks (VPNs) are becoming a popular way to grant remote access to employees while hiding online activities from attackers. With a VPN, your organization can secure network traffic between your site and users by creating an end-to-end secure private network connection over a public network.
In this article, you will learn how a VPN works, what protocols are needed, what challenges are involved, and what alternatives are available. This will help you to decide whether a VPN is right for your organization.
What Is a VPN?
A virtual private network uses a public network like the internet to create a secured end-to-end private network connection. This connection uses dedicated circuits or tunneling protocols to transport traffic over public networks. The traffic involved is encrypted using VPN encryption protocols such as Internet Protocol Security (IPsec) or Secure Sockets Layer (SSL) / Transport Layer Security (TLS).
Different VPN services use different encryption processes to secure users’ traffic, with varying degrees of success. It is wise to consider the encryption mechanism used by a VPN provider when choosing a VPN.
VPN use cases
-
Protect online activities: A VPN uses advanced encryption and authentication protocols to provide a high level of security and confidentiality. Even if the network is breached, the attacker would see only encrypted data.
-
Access geo-restricted data: With a VPN, you can access geo-restricted content such as a website or application blocked to users in certain geographic locations. You can also bypass certain internet censorship laws.
-
Grant remote access to private networks: You can use a private network to access and download sensitive files as well as to securely access external servers. A VPN creates an encrypted tunnel between your organization’s devices on the network and your employee’s end device. This allows your team to work securely from anywhere, anytime using any device.
-
Stop ISP throttling: Internet service providers (ISPs) control the speed and quality of your service. Some ISPs have policies allowing them to throttle internet speed. With a VPN, you can mask your internet traffic, which makes throttling more difficult.
How VPNs work
A VPN uses a tunneling mechanism to hide your device’s Internet Protocol (IP) address and encrypt your data using an encryption protocol. When you connect to a network using a VPN, the VPN software installed on your device encrypts your data and sends it to the VPN server, which generates the key used to authenticate the connection and route your data to its destination.
The VPN acts as an intermediary as you connect to the internet. This means that your ISP and other third parties can’t access the websites you visited or the data you send or receive online.
Common VPN protocols
There are various VPN protocols available to determine how data is routed through a connection. These protocols determine how secure your connection is and offer different specifications depending on your needs. Following are some commonly used VPN protocols.
OpenVPN
OpenVPN is an open source VPN protocol that allows developers to access its underlying code to check for vulnerabilities and to use it in their projects. OpenVPN uses Advanced Encryption Standard-256 (AES-256) for key encryption, 2048-bit RSA authentication for client authentication, and SHA-1 160-bit hash algorithm for data integrity. This makes OpenVPN virtually impossible to break.
IKE2
Internet Key Exchange version 2 (IKEv2) is another commonly used VPN tunneling protocol developed by Microsoft and Cisco. This protocol provides a secret key exchange session, and it is frequently paired with IPsec for data encryption and authentication. It is good at re-establishing connections in the event of connection loss and excels at switching connections across networks. This makes it good for mobile VPN solutions.
SSTP
SSTP stands for Secure Socket Tunneling Protocol. Unlike OpenVPN, SSTP is a proprietary protocol developed by Microsoft, so developers do not have access to its source code. SSTP uses 2048-bit SSL/TLS certificates for authentication and a 256-bit SSL key for encryption. It offers significant support for third-party clients.
WireGuard
WireGuard is the newest open source VPN protocol, known for its simplicity. When compared to common VPNs, WireGuard offers a simple codebase, and it is easier to set up with support for a wide range of encryption protocols. Unlike other VPN protocols, WireGuard consumes fewer device resources, such as RAM, ROM and device battery.
L2TP/IPsec
Layer 2 Tunneling Protocol is a VPN protocol that does not provide any form of encryption, but it is commonly paired with IP security standard RFC 2401-2412, which defines how a VPN can connect securely across IP networks. The IPsec framework provides confidentiality, integrity and origin authentication for your connection, using various Diffie-Hellman algorithms for secure key exchange.
PPTP
The Point-to-Point Tunneling Protocol is an obsolete method for implementing virtual private networks. First developed by Microsoft, PPTP is now deprecated and replaced by L2TP.
Types of VPNs
There are multiple types of VPNs available. Following are some of your options.
Remote-Access VPN
A remote-access VPN allows workers to securely connect to corporate data centers, intranet, applications, and networks by encrypting users’ traffic. It does this by creating a tunnel between an organization’s network and the remote user’s device using IPsec or SSL.
With a remote VPN, the user must initiate remote access using either a clientless or client-based VPN.
With a clientless VPN connection, the user establishes the connection using a web browser SSL/TLS, which is mostly used to protect HTTP traffic and other protocols such as POP3.
For a client-based connection, a remote user will need to install VPN software on the end device and then use the VPN client to start the connection. The destination VPN gateway then authenticates this connection.
Site-to-site VPN
In a site-to-site VPN, the user’s end device sends encrypted TCP/IP traffic through a VPN terminating device. This device encapsulates and encrypts the traffic and transports it over a public network to another VPN terminating device at the destination. The VPN terminating device at the destination decrypts this traffic and sends it to end devices. A VPN termination device can be — for example — a router, firewall or VPN connector.
For a remote-access VPN, traffic is encrypted from one end device to another, but for a site-to-site VPN, traffic from end devices is sent without encryption to a VPN gateway. The gateway encrypts the traffic and transports it over a public network to another VPN gateway, which decrypts it and sends it to end devices. This means that between your end devices and the VPN gateway, network traffic can be compromised.
Extranet-based site-to-site VPN
An extranet-based site-to-site VPN is used between partnering companies to provide privileged access to specific information while still maintaining a high level of security. These partners can be vendors, customers or third-party applications.
GRE Over IPsec
Generic Routing Encapsulation (GRE) is a VPN tunneling protocol used to encapsulate various network-layer protocols. The site-to-site protocol supports multicast and broadcast network traffic. However, GRE is not secured because it does not support encryption by default.
GRE can be paired with IPsec to provide security for network traffic. IPsec on its own supports unicast traffic, not broadcast or multicast. GRE over IPsec allows you to encapsulate a GRE packet into an IPsec packet, which can be forwarded securely from a VPN source gateway to the destination VPN gateway.
VPN shortcomings
With all the advantages that VPNs offer, they still have some limitations. These include the following:
-
Can’t offer complete anonymity: VPNs are usually marketed as providing online anonymity, but this is really not true. Against techniques and services such as fingerprinting, web trackers, and cookies, even the best VPNs can’t guarantee anonymity. Your name, geographic location, and other small pieces of data can be used to identify your online presence.
-
Can’t protect against infected or compromised devices: A good VPN will protect your device from malicious code injection during man-in-the-middle (MITM) attacks and from eavesdropping; however, it can’t protect you from malware such as viruses and ransomware.
-
Can’t provide granular access: With a VPN, users’ IP addresses are hidden. This makes it almost impossible to set access control policies that provide granular access to your organization’s resources.
-
Easy to compromise: Most VPN clients only require a username and password for authentication. If these credentials fall into the wrong hands, your organization’s data can be compromised. The credentials can be exposed through VPNs that log users’ activity.
Risks of VPN providers
Hosted VPN providers can also increase your security risk, due to the following factors:
-
Impossible to verify if they keep logs: One of the key reasons for using VPNs is to avoid exposing your data to unwanted individuals. However, your VPN provider can log your online activities. You should check a VPN’s logging policy before using it. Most providers will claim that they do not log users’ data, but this claim is impossible to verify because it is in the provider’s interest to log users’ data in case of a legal battle.
-
User activity shared with advertisers: If VPN service providers log your personal data, such as demographics, location, frequently searched items, and search keywords, they can sell or share this data with third parties for advertising purposes.
Alternatives to VPN
Due to the above limitations, alternatives to VPNs have been developed for various use cases to help improve your online security and privacy. Following are some use cases and their alternatives:
-
Remote access to internal systems: If you need to grant remote access to your organization’s internal systems, you can use proxy servers like Teleport. These servers serve as a gateway between you and the internet. Teleport offers various levels of functionality to ensure security and privacy.
-
Need for anonymity: If you need complete anonymity online that can’t be provided by VPNs, consider using the Tor browser or DuckDuckGo search engine.
-
Fine-grained services for users: If you need to fine-grain your organization’s services that a remote user can access, consider Zero Trust Network Access (ZTNA) tools. They allow you to define access control policies for secure remote access to applications and services.
Conclusion
The increase in remote work and the need for online privacy have led to the growth in demand for VPNs. These networks provide a certain degree of security and privacy, but they’re not designed to meet the needs of today’s DevOps ecosystem. Though you can take care to select a VPN and provider with appropriate policies, you can also seek out alternatives.
Teleport, an open-source solution, grants users access to resources running on devices located anywhere in the world. Teleport can provide you secure access to a Kubernetes cluster, web app, PostgreSQL, MySQL database, and SSH or RDP host behind NAT. With a deep focus on the security protocols, Teleport is designed to work with every tool in today’s DevOps ecosystem, ensuring secure access for your organization.
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter