Home - Teleport Blog - How To Use SSH ProxyJump and SSH ProxyCommand
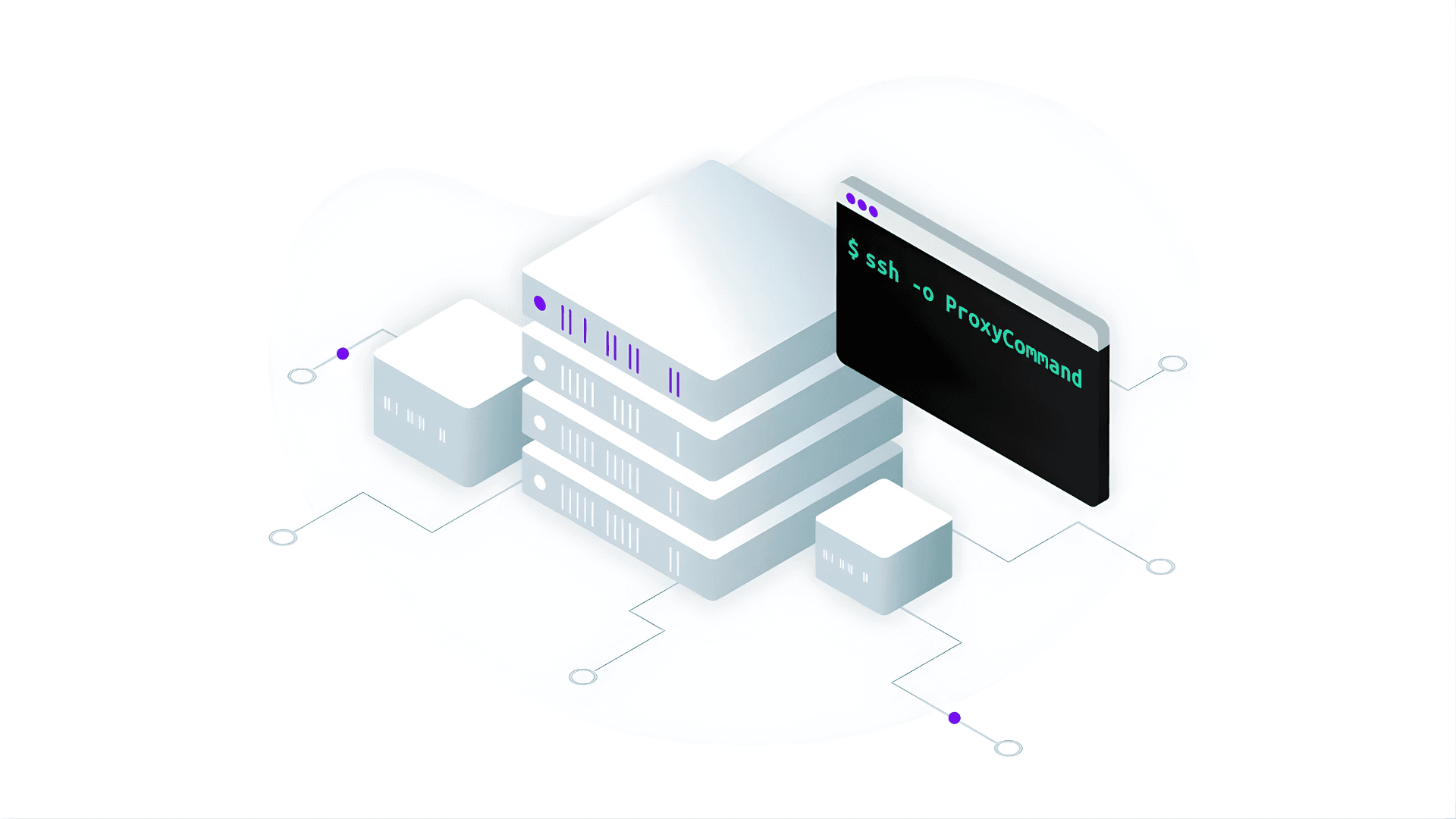
How To Use SSH ProxyJump and SSH ProxyCommand
Updated January 2026
OpenSSH ProxyJump and ProxyCommand directives both direct your SSH client on how to connect to a remote server via an intermediary server.
If you are new to jump servers, start by learning about jump servers and bastion hosts, read our tutorial on how to set up a jump server and learn some of the best practices to secure them.
What is SSH ProxyJump?
SSH ProxyJump is a feature introduced in OpenSSH 7.3 that allows a user to connect to a target server indirectly by routing the SSH connection through one or more intermediary servers, known as jump hosts or bastion hosts.
This creates a single, end-to-end encrypted SSH session from the client machine to the final destination, streamlining access to servers that are not directly reachable due to firewall rules or network segmentation
What is SSH ProxyCommand?
The ProxyCommand is an SSH directive that specifies an arbitrary local command to execute to establish the connection to the target server.
It works by forwarding standard input (stdin) and standard output (stdout) from your local machine through the intermediate jump or bastion host to reach a server that is otherwise not directly accessible.
ProxyJump vs. ProxyCommand
ProxyJump is the easiest and recommended way to jump between hosts because it ensures that traffic passing through the intermediate hosts is always encrypted end-to-end.
Before ProxyJump was released, ProxyCommand was the only way to jump hosts. ProxyCommand works by forwarding standard in and standard out (stdio) through an intermediate host. Internally, ProxyJump wraps the ProxyCommand in a secure and easy directive.
Below is a sample usage of the ProxyJump command. Note the shorthand -J.
$ ssh -J <jump server> <remote server>
Below is a sample usage of the ProxyJump command for jumping between multiple hosts.
$ ssh -J <jump server1>,<jump server2>,<jump server3> <remote server>
Below is a sample usage of ProxyCommand.
$ ssh -o ProxyCommand="ssh -W %h:%p <jump server>" <remote server>
If you’re using OpenSSH on a Windows machine, you must include the full SSH file path in the ProxyCommand directive. It should look similar to this:
ProxyCommand C:\Windows\System32\OpenSSH\ssh.exe -W %h:%p <bastion_host>
How to configure ProxyJump and ProxyCommand in the SSH client config file
It can be tedious to configure jump routes between each new SSH connection. Luckily, OpenSSH allows configuring ProxyJump or ProxyCommand via the SSH client config file (usually ~/.ssh/config).
In the example below, we will set up the SSH config file to jump to a single intermediary server (noted as "jumpserver"). Then we will log in to a host called "remoteserver" on port "2048" as a user named "dev".
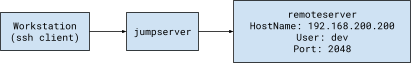
On the workstation where you want to initiate the SSH connection, open the OpenSSH client configuration file (~/.ssh/config) using your text editor of choice and add the following code:
Host remoteserver
HostName 192.168.200.200
User dev
IdentityFile ~/.ssh/<your_key>
Port 2048
## sample for ProxyJump
ProxyJump user@<jumpserver>
## sample for ProxyCommand
ProxyCommand ssh -W %h:%p <jumpserver>
We can now simply use the hostname "remoteserver" without the hassle of configuring the jump route each time you access "remoteserver".
$ ssh remoteserver
For further detail on using client config files, you can refer to our blog post on how to use SSH client config files.
How to configure conditional jumping using Match exec
Sometimes, we may need two different client configurations for the same host. For example, to jump through one intermediate server when working from the office ,but through two intermediate servers when working from home.
This requirement is also very common in a home lab setup. Lab owners often want direct access when they SSH from home, but need to jump through an intermediate server when they access from outside the home network.
OpenSSH supports Match exec directives, which can be used to configure jumping decisions based on given criteria.
What is Match exec?
Match exec is a conditional directive in your SSH client config that runs a local command and applies the corresponding configuration block only if that command succeeds or fails (when negated with !).
This allows you to switch SSH settings, like ProxyJump, based on client-side conditions such as network, IP address, or environment.
The following example shows using !exec to check if the IP address in network interface en0 is 192.168.100.10.
If grep returns a row, this command will succeed, and SSH will use ProxyJump. Otherwise, it will ignore this configuration block.
Match host server1 !exec "ifconfig en0 | grep 192.168.100.10"
ProxyJump user@<jump server>
Host server1
Hostname 192.168.100.20
What are the use cases for ProxyJump and ProxyCommand?
ProxyJump is most useful for:
- Reaching private servers that are not directly reachable by hopping through a bastion host.
- Chaining through multiple intermediaries for segmented networks or tightly restricted environments.
- Using conditional routing in
~/.ssh/config(Match exec) to pick a different jump path depending on where you are.
ProxyCommand is most useful when you need compatibility with older SSH clients or more custom connection logic than ProxyJump supports.
What are the pros and cons of ProxyJump?
Pros:
- Simple to use — One
-Joption replaces long ProxyCommand strings. - Easy to maintain — SSH config stays readable, even with multi-hop jumps.
- Built into OpenSSH — Works with standard SSH tooling and workflows.
Cons:
- Hard to scale in dynamic environments — Jump paths and hostnames change, and configs drift.
- Limited auditing — No built-in session recording or central reporting.
- Limited access control — Just-in-time (JIT) access and least-privilege workflows are harder to enforce because access is granted at the system user level.
Conclusion
This post explains what ProxyJump and ProxyCommand are, how to use them, and the differences between them. In summary, ProxyJump is a modern, easier alternative to ProxyCommand, but ProxyCommand provides greater route configuration flexibility.
While these commands are very helpful for SSH jumping in a small environment, the config file can become long and chaotic if you have a large fleet of SSH servers or require different jump configurations for different servers. This issue can be easily solved using a modern SSH server such as Teleport.
Teleport is open source, and you can use it as a drop-in replacement to OpenSSH. Teleport proxy and Teleport SSH client (tsh) intelligently configure routes for you so that you can manage access via jump servers for a large fleet of SSH servers without the hassle of maintaining a long list of SSH client config files.
Learn how Teleport works or try it for yourself today.
Related Resources
Table Of Contents
- What is SSH ProxyJump?
- What is SSH ProxyCommand?
- ProxyJump vs. ProxyCommand
- How to configure ProxyJump and ProxyCommand in the SSH client config file
- How to configure conditional jumping using Match exec
- What are the use cases for ProxyJump and ProxyCommand?
- What are the pros and cons of ProxyJump?
- Conclusion
- Related Resources
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter