TELEPORT MACHINE & WORKLOAD IDENTITY
Secure Every Machine,
Workload, and Agent
Issue cryptographic identities to every bot, CI job, container, VM, and service for short-lived, zero-trust access and inter-service authentication across your infrastructure.
TRUSTED BY LEADERS


















THE NON-HUMAN IDENTITY CHALLENGE
Traditional credentials fail modern infrastructure
Modern infrastructure is automated. Servers, pipelines, containers, AI agents, and microservices now power most workloads — not humans.
In these environments, traditional credentials create unmanaged attack surface, operational burden, and compliance headaches.
Static credentials, keys, and tokens pile up and are left unrotated and over-privileged.
Secrets sprawl across CI/CD pipelines, clouds, and beyond, increasing risk.
Inter-service communication lacks identity accountability, logs, and control.
Agentic AI introduces autonomous actors without identity and guardrails.
Teleport Machine & Workload Identity
Prevent the agentic identity crisis by bringing unique, delegated, and visible identity to your AI agents.
Teleport Machine & Workload Identity brings identity-based security to non-human actors, transforming every machine into a first-class identity governed by policy and issued dynamically.
Eliminate static credentials like long-lived keys, tokens, or secrets.
Secure inter-service and cross-cloud authentication with mTLS, SPIFFE-compatible IDs, JWTs, and role-based cloud authentication.
Enforce least privilege and zero trust to grant only the access each workload needs, only when it needs it.
Unlock full audit and compliance visibility with every identity issuance, access, and renewal logged and traceable.
Secure non-human identities (NHIs) across your infrastructure
CI/CD pipelines & deployment automation
Replace hard-coded secrets with short-lived certificates scoped per job or pipeline.
Infrastructure-as-Code (IaC) workflows
Give Terraform, Pulumi, or Spacelift bots identity-backed access without manual key rotation.
Microservices and cloud-native workloads
Issue SPIFFE/X.509 identities for mTLS or JWT-based communication across services, clouds, or trust domains.
Hybrid and multi-cloud environments
Provide consistent identity across on-prem, cloud, containers, and VMs to simplify auth and policy.
AI agents and autonomous processes
Treat agents as identities and control permissions, audit access, and eliminate overly-broad credentials.
Protect your environment — on your terms
Teleport supports complementary architectural patterns, letting you adopt identity-based security in the method that fits your use case best.
Secure access
For workflows that need access to protected infrastructure (CI/CD, SSH, databases, Kubernetes, MCP, etc.) with RBAC, session auditing, and enforced policies.
Universal identity
For workloads that need identity across clouds and services (service-to-service mTLS, cloud APIs, service meshes), using open standards like SPIFFE, JWT, and X.509.
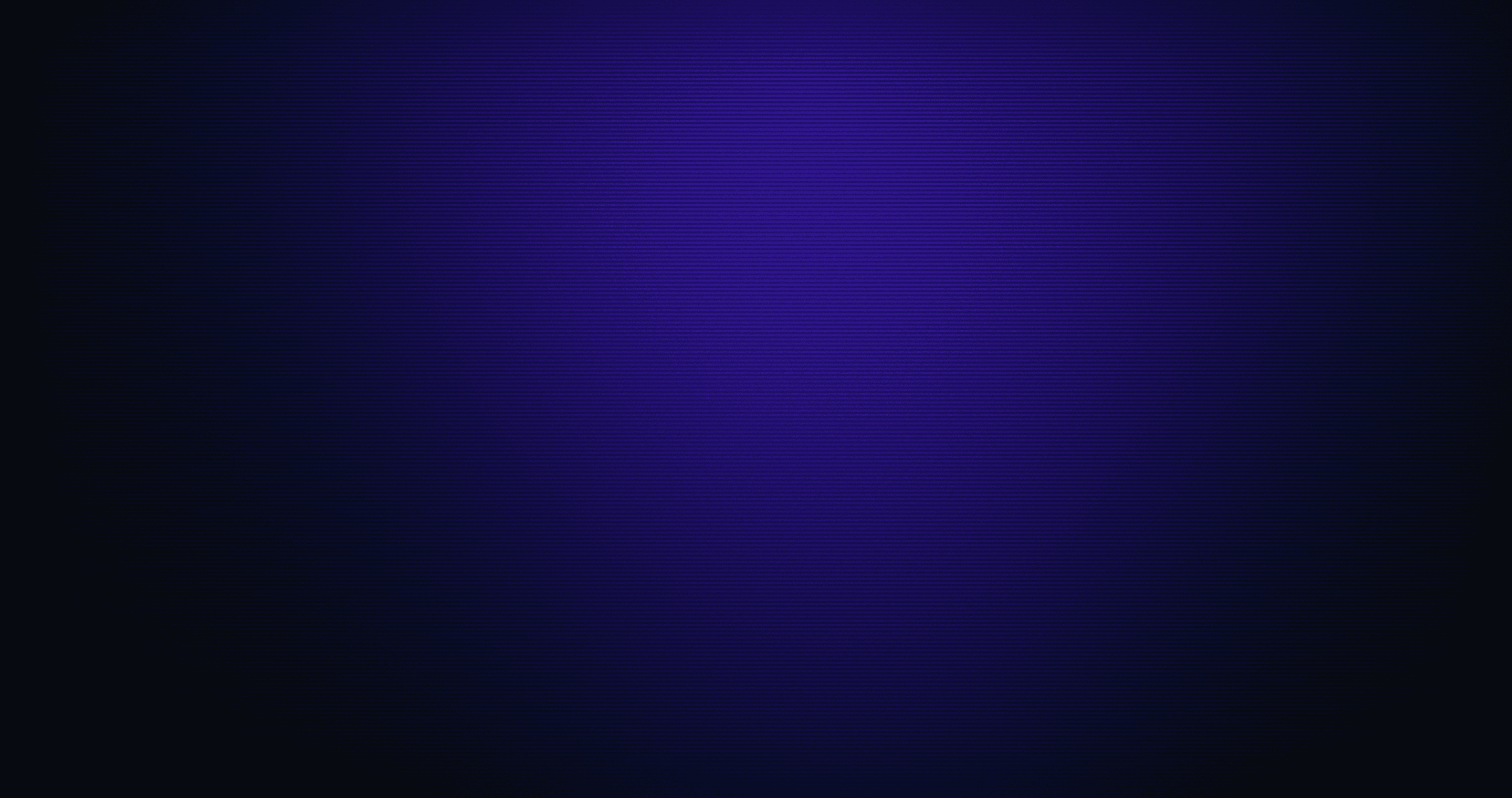
How Machine & Workload Identity works
- 1
Deploy tbot agent
Deploy on machines, containers, or in your orchestration environment. - 2
Request identity at runtime
tbot authenticates using a join method (token, metadata, cloud-federation, etc.) and is issued a short-lived certificate or token. - 3
Access resources or communicate securely
Workloads use the identity to access infrastructure or authenticate to internal or external services, and APIs via mTLS, JWT, or SPIFFE. - 4
Automatic renewal and rotation
Identities are renewed automatically and certificates expire automatically without manual secret rotation. - 5
Full audit and traceability
Every issuance, access, and session is logged for identity-aware compliance and forensic visibility.
Unify identity and eliminate secrets at scale
Unified infrastructure identity
Unified infrastructure identity
Manage human and non-human identities together from a single platform without vaults or secrets.
Ephemeral by design
Ephemeral by design
Issue short-lived certificates and tokens that expire quickly to prevent credential exhaustion and reduce exposure.
Audit & compliance ready
Audit & compliance ready
Sessions, identity issuance, and access events are logged to simplify compliance for SOC 2, HIPAA, PCI, and more.
Scales with your infrastructure
Scales with your infrastructure
Secure servers, containers, cloud VMs, Kubernetes clusters, CI/CD, and service-mesh workloads across multi-cloud/hybrid environments without redesigning your stack.
Supports open standards: SPIFFE, JWT, X.509
Teleport Machine & Workload Identity is compatible with the open-source Secure Production Identity Framework for Everyone (SPIFFE) standards and open standards like JWT and X.509 certificates to secure communication across clouds, runtimes, and vendors
SPIFFE
Provides out-of-the-box tooling for the SPIFFE ecosystem, pairing SPIFFE benefits with RBAC, MFA, device trust, audit logging, and more.
Developer tooling
Supports open-source policy agents and developer tool APIs, making a wealth of off-the-shelf tools and SDKs accessible to simplify integrations.
Bootstrapping trust
Supports bootstrapping trust by grounding root of trust in secure hardware environments.
AUTOMATION IS THE NEW ATTACK SURFACE
Securing Non-Human Identities at the Infrastructure Layer
Automation now powers nearly every critical system: environments are provisioned with code, software is deployed through pipelines, and workloads are scaled across distributed services and AI agents. But beneath this velocity lies an expanding attack surface that’s often invisible: non-human identities (NHIs).
Download this white paper to learn how to start securing NHIs at the infrastructure layer.

Trusted by teams building critical infrastructure.
Teleport is a strategic technology partner as they help our joint customers to scale their AWS resources in a secure manner. With Teleport’s Identity-Native Infrastructure Access solution, DevOps Engineers get a frictionless experience managing infrastructure that doesn’t require secrets while implementing zero trust architecture in AWS.
We use Teleport Access Requests in combination with Auth0 to easily manage access to our infrastructure. Prior to Teleport, we manually managed SSH keys and a bastion machine and it was an organizational nightmare.
We used to go through multiple steps just to access cloud resources, and now it happens almost instantly. Our engineers are really happy with the significant improvement in their workflow.
Teleport’s vision for Infrastructure Identity is a game-changer for securing hybrid infrastructure.
With Teleport, we were even able to close the Kubernetes API without losing access for our engineers or automation tools. That alone was a huge win.
Teleport allows us to comply with the regulatory hurdles that come with running an international stock exchange. The use of bastion hosts, integration with our identity service and auditing capabilities give us a compliant way to access our internal infrastructure.
The Infrastructure Identity solution from Teleport offers a glimpse into the future of more secure, more resilient, and higher-velocity enterprise computing.
Teleport has made obtaining a FedRAMP-Moderate ATO that much more achievable via their FIPS 140-2 endpoints, ease in integration with our SSO and MFA , and the view into audit logs of remote connection sessions provide the appropriate insight for Continuous Monitoring.
Over the many years of using Teleport, it's been an essential piece of my infrastructure to help secure access, and centralize my infrastructure into one dashboard, without having to jump around… I'm not sure how I could go without it.
Ready to Teleport?
Frequently Asked Questions
What is Teleport Machine & Workload Identity?
Teleport Machine & Workload Identity uses the tbot agent to issue and renew short-lived certificates and tokens for machines and workloads so they can authenticate to infrastructure and cloud providers without static secrets.
How does Teleport remove static credentials from CI/CD and services?
tbot runs alongside your CI/CD jobs and services, continuously writing short-lived credentials to use instead of hard-coded API keys or passwords to access Kubernetes, AWS, Azure, Bitbucket, CircleCI, GCP, GitLab, GitHub Actions, Jenkins, Linux, and more.
How is Machine & Workload Identity different from using a secrets vault?
Rather than storing long-lived credentials like a vault, Teleport Machine & Workload Identity replaces them with dynamically issued, short-lived X.509 certificates and JWTs that workloads use directly for authentication.
How do SPIFFE, JWT, and X.509 fit into this?
Teleport issues SPIFFE-compatible workload identities as JWT and X.509 SVIDs, following SPIFFE standards for encoding and validating these documents to secure service-to-service communication.











