Database Access with ClickHouse
The Teleport Clickhouse integration allows you to enroll ClickHouse databases with Teleport.
This guide will help you to:
- Install and configure a Teleport database agent.
- Set up Teleport to access your self-hosted ClickHouse database.
- Connect to your database through Teleport.
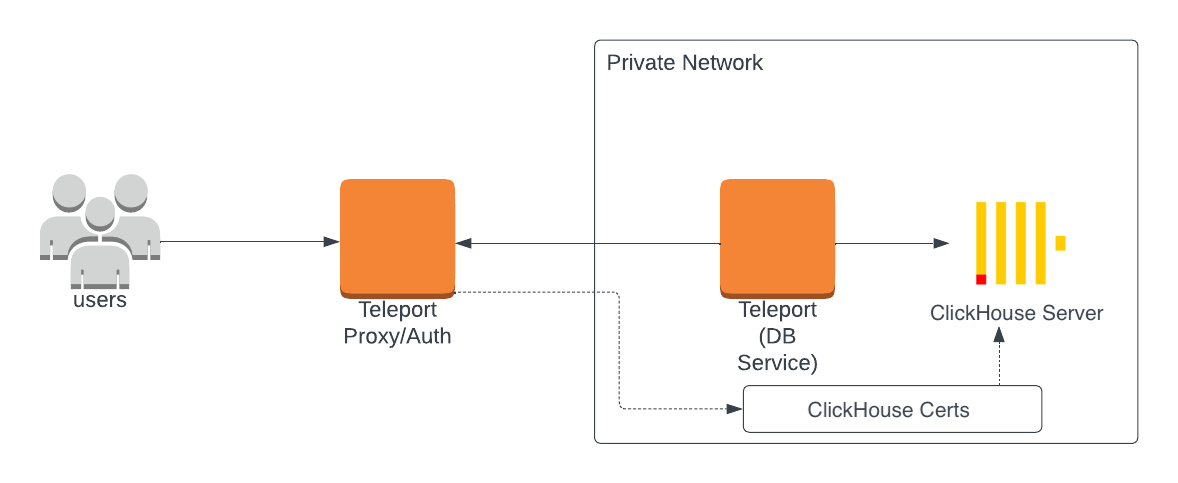
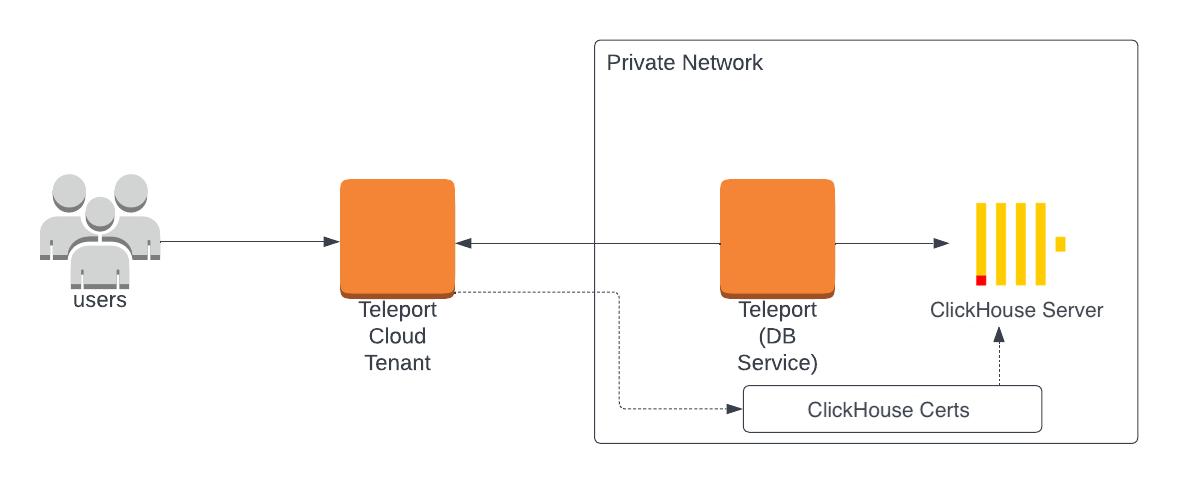
How it works
The Teleport Database Service authenticates to ClickHouse using x509 certificates, which are available for the ClickHouse HTTP and Native (TCP) interfaces. The Teleport Database Service can communicate in both the ClickHouse Native (TCP) and HTTP protocols, and you can select which protocol to use when configuring the Teleport Database Service.
Teleport audit logs for query activity are only supported for the ClickHouse HTTP interface. Teleport support for ClickHouse's native interfaces does not include audit logs for database query activity.
- Self-Hosted
- Teleport Cloud
Prerequisites
-
A running Teleport cluster version 15.4.22 or above. If you want to get started with Teleport, sign up for a free trial or set up a demo environment.
-
The
tctladmin tool andtshclient tool.On Teleport Enterprise, you must use the Enterprise version of
tctl, which you can download from your Teleport account workspace. Otherwise, visit Installation for instructions on downloadingtctlandtshfor Teleport Community Edition.
- Either a Linux host or Kubernetes cluster where you will run the Teleport Database Service.
You will also need the following, depending on the ClickHouse protocol you choose:
- HTTP
- Native (TCP)
- A self-hosted deployment of ClickHouse Server v22.3 or later.
- A self-hosted deployment of ClickHouse Server v23.3 or later.
- The clickhouse-client installed and added to your user's
PATHenvironment variable.
- Optional: a certificate authority that issues certificates for your self-hosted database.
Step 1/5. Create a Teleport token and user
The Database Service requires a valid join token to join your Teleport cluster.
Run the following tctl command and save the token output in /tmp/token
on the server that will run the Database Service:
$ tctl tokens add --type=db --format=text
abcd123-insecure-do-not-use-this
To modify an existing user to provide access to the Database Service, see Database Access Controls
- Teleport Community Edition
- Teleport Enterprise/Enterprise Cloud
Create a local Teleport user with the built-in access role:
$ tctl users add \
--roles=access \
--db-users="*" \
--db-names="*" \
alice
Create a local Teleport user with the built-in access and requester roles:
$ tctl users add \
--roles=access,requester \
--db-users="*" \
--db-names="*" \
alice
| Flag | Description |
|---|---|
--roles | List of roles to assign to the user. The builtin access role allows them to connect to any database server registered with Teleport. |
--db-users | List of database usernames the user will be allowed to use when connecting to the databases. A wildcard allows any user. |
--db-names | List of logical databases (aka schemas) the user will be allowed to connect to within a database server. A wildcard allows any database. |
Database names are only enforced for PostgreSQL, MongoDB, and Cloud Spanner databases.
For more detailed information about database access controls and how to restrict access see RBAC documentation.
Step 2/5. Create a certificate/key pair
Teleport uses mutual TLS authentication with self-hosted databases. These databases must be able to verify certificates presented by the Teleport Database Service. Self-hosted databases also need a certificate/key pair that Teleport can verify.
By default, the Teleport Database Service trusts certificates issued by a certificate authority managed by the Teleport Auth Service. You can either:
- Configure your self-hosted database to trust this CA, and instruct Teleport to issue a certificate for the database to present to the Teleport Database Service.
- Configure the Database Service to trust a custom CA.
- Use the Teleport CA
- Use a custom CA
To configure the database to trust the Teleport CA and issue a certificate for the database, follow these instructions on your workstation:
-
To use
tctlfrom your workstation, your Teleport user must be allowed to impersonate the system roleDbin order to be able to generate the database certificate. Include the followingallowrule in in your Teleport user's role:allow:
impersonate:
users: ["Db"]
roles: ["Db"] -
Export Teleport's certificate authority and a generate certificate/key pair. This example generates a certificate with a 1-year validity period.
db.example.comis the hostname where the Teleport Database Service can reach the Clickhouse server.$ tctl auth sign --format=db --host=db.example.com --out=server --ttl=2190hTTLWe recommend using a shorter TTL, but keep mind that you'll need to update the database server certificate before it expires to not lose the ability to connect. Pick the TTL value that best fits your use-case.
The command creates 3 files:
server.cas,server.crtandserver.key.
If the Clickhouse database already has a CA that it uses to sign certificates
, you only need to export a Teleport CA certificate for the database to
authenticate traffic from the Teleport Database Service. You do not need to
enable Db impersonation privileges.
-
Replace example.teleport.sh:443 with the host and web port of the Teleport Proxy Service in your cluster. Run the following command on your workstation:
$ tctl auth export --type=db-client --auth-server=example.teleport.sh:443 > db-client.casThe command creates 1 file,
db-client.cas. -
Append the contents of
db-client.casto your database's existing CA cert file, which this guide expects to be calledserver.cas. -
Generate
server.crtandserver.keyby retrieving a TLS certificate and private key from your existing database CA, signed for your database server. You will use these files later in the guide.
Step 3/5. Configure ClickHouse
Use the generated secrets to enable mutual TLS in your clickhouse-server/config.xml configuration file:
<openSSL>
<server>
<privateKeyFile>/path/to/server.key</privateKeyFile>
<caConfig>/path/to/server.cas</caConfig>
<certificateFile>/path/to/server.crt</certificateFile>
<verificationMode>strict</verificationMode>
</server>
</openSSL>
Restart the ClickHouse Server to enable this configuration. Additionally, your ClickHouse database user accounts must be configured to require a valid client certificate:
CREATE USER alice IDENTIFIED WITH ssl_certificate CN 'alice';
By default, the created user may not have access to anything and won't be able to connect, so let's grant it some permissions:
GRANT ALL ON *.* TO alice;
Step 4/5. Configure and start the Database Service
Install and configure Teleport on the host or Kubernetes cluster where you will
run the Teleport Database Service. Assign protocol to
clickhouse-http for the HTTP protocol and clickhouse for the native
ClickHouse protocol:
- Linux Server
- Kubernetes Cluster
Install Teleport on your Linux server:
-
Assign edition to one of the following, depending on your Teleport edition:
Edition Value Teleport Enterprise Cloud cloudTeleport Enterprise (Self-Hosted) enterpriseTeleport Community Edition oss -
Get the version of Teleport to install. If you have automatic agent updates enabled in your cluster, query the latest Teleport version that is compatible with the updater:
$ TELEPORT_DOMAIN=example.teleport.com
$ TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"Otherwise, get the version of your Teleport cluster:
$ TELEPORT_DOMAIN=example.teleport.com
$ TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/ping | jq -r '.server_version')" -
Install Teleport on your Linux server:
$ curl https://cdn.teleport.dev/install-v15.4.22.sh | bash -s ${TELEPORT_VERSION} editionThe installation script detects the package manager on your Linux server and uses it to install Teleport binaries. To customize your installation, learn about the Teleport package repositories in the installation guide.
The step below will overwrite an existing configuration file, so if
you're running multiple services add --output=stdout to print the config in
your terminal, and manually adjust /etc/teleport.yaml.
On the host where you will run the Teleport Database Service, start Teleport with the appropriate configuration.
Note that a single Teleport process can run multiple different services, for
example multiple Database Service agents as well as the SSH Service or Application
Service. The step below will overwrite an existing configuration file, so if
you're running multiple services add --output=stdout to print the config in
your terminal, and manually adjust /etc/teleport.yaml.
Run the following command to generate a configuration file at
/etc/teleport.yaml for the Database Service. Update
teleport.example.com:443 to use the host and port of the Teleport Proxy
Service:
$ sudo teleport db configure create \
-o file \
--token=/tmp/token \
--proxy=teleport.example.com:443 \
--name=example-clickhouse \
--protocol=protocol \
--uri=clickhouse.example.com:8443 \
--labels=env=dev
To configure the Teleport Database Service to trust a custom CA:
-
Export a CA certificate for the custom CA and make it available at
/var/lib/teleport/db.caon the Teleport Database Service host. -
Run a variation of the command above that uses the
--ca-cert-fileflag. This configures the Teleport Database Service to use the CA certificate atdb.cato verify traffic from the database:$ sudo teleport db configure create \
-o file \
--token=/tmp/token \
--proxy=teleport.example.com:443 \
--name=example-clickhouse \
--protocol=protocol \
--uri=clickhouse.example.com:8443 \
--ca-cert-file="/var/lib/teleport/db.ca" \
--labels=env=dev
Configure the Teleport Database Service to start automatically when the host boots up by creating a systemd service for it. The instructions depend on how you installed the Teleport Database Service.
- Package Manager
- TAR Archive
On the host where you will run the Teleport Database Service, enable and start Teleport:
$ sudo systemctl enable teleport
$ sudo systemctl start teleport
On the host where you will run the Teleport Database Service, create a systemd service configuration for Teleport, enable the Teleport service, and start Teleport:
$ sudo teleport install systemd -o /etc/systemd/system/teleport.service
$ sudo systemctl enable teleport
$ sudo systemctl start teleport
You can check the status of the Teleport Database Service with systemctl status teleport
and view its logs with journalctl -fu teleport.
Teleport provides Helm charts for installing the Teleport Database Service in Kubernetes Clusters.
Set up the Teleport Helm repository.
Allow Helm to install charts that are hosted in the Teleport Helm repository:
$ helm repo add teleport https://charts.releases.teleport.dev
Update the cache of charts from the remote repository so you can upgrade to all available releases:
$ helm repo update
Install a Teleport agent into your Kubernetes Cluster with the Teleport Database Service configuration.
Create a file called values.yaml with the following content. Update teleport.example.com:443 to use the host and port of the Teleport Proxy
Service and JOIN_TOKEN to the join token you created earlier:
roles: db
proxyAddr: teleport.example.com:443
# Set to false if using Teleport Community Edition
enterprise: true
authToken: JOIN_TOKEN
databases:
- name: example-clickhouse
uri: clickhouse.example.com:8443
protocol: protocol
labels:
env: dev
To configure the Teleport Database Service to trust a custom CA:
-
Export a CA certificate for the custom CA and make it available at
db.caon your workstation. -
Create a secret containing the database CA certificate in the same namespace as Teleport using the following command:
$ kubectl create secret generic db-ca --from-file=ca.pem=/path/to/db.ca -
Add the following to
values.yaml:
roles: db
proxyAddr: teleport.example.com:443
# Set to false if using Teleport Community Edition
enterprise: true
authToken: JOIN_TOKEN
databases:
- name: example-clickhouse
uri: clickhouse.example.com:8443
protocol: <protocol>
+ tls:
+ ca_cert_file: "/etc/teleport-tls-db/db-ca/ca.pem"
static_labels:
env: dev
+ extraVolumes:
+ - name: db-ca
+ secret:
+ secretName: db-ca
+ extraVolumeMounts:
+ - name: db-ca
+ mountPath: /etc/teleport-tls-db/db-ca
+ readOnly: true
Install the chart:
$ helm install teleport-kube-agent teleport/teleport-kube-agent \
--create-namespace \
--namespace teleport-agent \
--version 15.4.22 \
-f values.yaml
Make sure that the Teleport agent pod is running. You should see one
teleport-kube-agent pod with a single ready container:
$ kubectl -n teleport-agent get pods
NAME READY STATUS RESTARTS AGE
teleport-kube-agent-0 1/1 Running 0 32s
A single Teleport process can run multiple services, for example multiple Database Service instances as well as other services such the SSH Service or Application Service.
Step 5/5. Connect
Once the Database Service has joined the cluster, log in to see the available databases:
- HTTP
- Native (TCP)
Log in to Teleport and list the databases you can connect to. You should see the ClickHouse database you enrolled earlier:
$ tsh login --proxy=teleport.example.com --user=alice
$ tsh db ls
# Name Description Allowed Users Labels Connect
# ------------------------- ----------- ------------- ------- -------
# example-clickhouse-http [*] env=dev
Create an authenticated proxy tunnel so you can connect to ClickHouse via a GUI
database client, or send a request via curl:
$ tsh proxy db --db-user=alice --tunnel example-clickhouse-http
# Started authenticated tunnel for the Clickhouse (HTTP) database "clickhouse-http" in cluster "teleport.example.com" on 127.0.0.1:59215.
# To avoid port randomization, you can choose the listening port using the --port flag.
#
# Use the following command to connect to the database or to the address above using other database GUI/CLI clients:
# $ curl http://localhost:59215/
To test the connection you can run the following command:
$ echo 'select currentUser();' | curl http://localhost:59215/ --data-binary @-
# alice
To log out of the database and remove credentials:
# Remove credentials for a particular database instance.
$ tsh db logout example-clickhouse-http
# Remove credentials for all database instances.
$ tsh db logout
Log in to Teleport and list the databases you can connect to. You should see the ClickHouse database you enrolled earlier:
$ tsh login --proxy=teleport.example.com --user=alice
$ tsh db ls
# Name Description Allowed Users Labels Connect
# ----------------------- ----------- ------------- ------- -------
# example-clickhouse [*] env=dev
Connect to the database:
$ tsh db connect --db-user=alice example-clickhouse
# ClickHouse client version 22.7.2.1.
# Connecting to localhost:59502 as user default.
# Connected to ClickHouse server version 23.4.2 revision 54462.
#
# 350ddafd1941 :) select 1;
#
# SELECT 1
#
# Query id: 327cfd34-2fec-4e04-a185-79fc840aa5cf
#
# ┌─1─┐
# │ 1 │
# └───┘
# ↓ Progress: 1.00 rows, 1.00 B (208.59 rows/s., 208.59 B/s.) (0.0 CPU, 9.19 KB RAM)
# 1 row in set. Elapsed: 0.005 sec.
#
# 350ddafd1941 :)
To log out of the database and remove credentials:
# Remove credentials for a particular database instance.
$ tsh db logout example-clickhouse
# Remove credentials for all database instances.
$ tsh db logout
Next steps
- Learn how to restrict access to certain users and databases.
- View the High Availability (HA) guide.
- Take a look at the YAML configuration reference.
- See the full CLI reference.