Home - Teleport Blog - Rethinking Privileged Access Management for Cloud and Cloud-Native Environments
Rethinking Privileged Access Management for Cloud and Cloud-Native Environments
SSH was designed in 1995, LDAP was initially developed in 1993, and role-based access control was introduced in 1992. The concept of least privilege was introduced in 1975. With all of these existing technologies, when are modern privileged access management solutions necessary? This is a common question asked when we pitch the idea of modern privileged access management (PAM).
It is not surprising that access control solutions are often taken for granted. Many concepts and technologies we are using now were introduced a couple of decades ago, and in many cases, roles and privilege management are prebuilt within the software and platform providers. However, with the way businesses today depend on the modern computing environment as a primary tool for competitive advantage, there's an increased weight to the security risks these older technologies introduce.
Traditionally, IT environments and teams were mainly involved in supporting business operations. But now, every company is a software company! This means the way teams operate their compute infrastructure, workflows and the footprint of the underlying infrastructure has changed significantly. So although the concepts of secure access control are still the same, the significant changes in the underlying computing infrastructure and workflows require a novel set of approaches to privileged access management.
Below, let's explore the four major challenges which are present in the modern cloud and cloud-native environments.
Challenges to modern privileged access management
1. Increased sensitivity of privileged accounts
The power of abstraction and API-based interaction has increased the sensitivity of privileged accounts in modern environments. The cloud and cloud-native environments literally give superpowers to teams that want to manage highly available, consistent and scalable environments. These superpowers come with risks, however, and can also be misused by adversaries.
For example, the accidental execution of commands like rm -rf, drop db in routine operations could result in the deletion of server or database data. In a traditional non-cloud environment though, the damage would only be limited to a single database or a single server. Compare this situation with modern infrastructure where a single command such as kubectl delete namespace production environment can delete the entire environment. Now imagine the power a rogue user would have when these modern privileges are compromised.
2. Increased attack surface
Today, the responsibility of infrastructure management has shifted from IT departments to individual teams that deploy and manage their own infrastructure. According to this research by Productiv, there are on average 40-60 SaaS apps used per department and more than 200 different SaaS apps used by the company as a whole. That is a huge attack surface for privileged accounts. Compare that with traditional environments where the majority of security concerns consisted of managing privileged accounts in a handful of Windows and Linux servers, SharePoint, databases and hardware appliances, including router firewalls and switches.
For another example, let's look at an internal web development team. A typical workflow would probably include using tools such as source version management (GitHub, GitLab), design management (Figma, InVision), website deployment (Vercel, Gatsby), and planning (Asana, Trello), etc. In the distributed cloud-based world of today, even the Vercel account of a junior web developer should be treated as a sensitive, privileged account. A compromise here could compromise the entire website, allowing an attacker to deface the front page, or even spread malware to the site's users.
Additionally, the level of access that is shared with third-party apps and contractors in the supply chain is constantly growing, which is far more challenging to track and control.
3. Challenges keeping up with fast-paced and automated workflows
Another major difference between traditional and modern environments is how the workflows have evolved, with more focus on automation, machine-to-machine access, use of modern ChatOps tools for communication, and the level of automation. This means that a traditional centralized model of manual approval and assignment of privileged access is hard to scale in the modern workflow. Administrators often fall into the mispractice of assigning permissively scoped, long-standing and long-lived credentials to keep pace with modern workflows, which creates a very risky scenario prone to security compromise.
4. Mixed environments
Many enterprises, especially businesses that have been operating since the data center era, have mixed environments, using traditional self-managed or co-located data centers, cloud infrastructure and cloud-native infrastructure. It is challenging to consolidate privileged access management across different environments as many available PAM solutions are not designed to address the use cases of these environments at the same time.
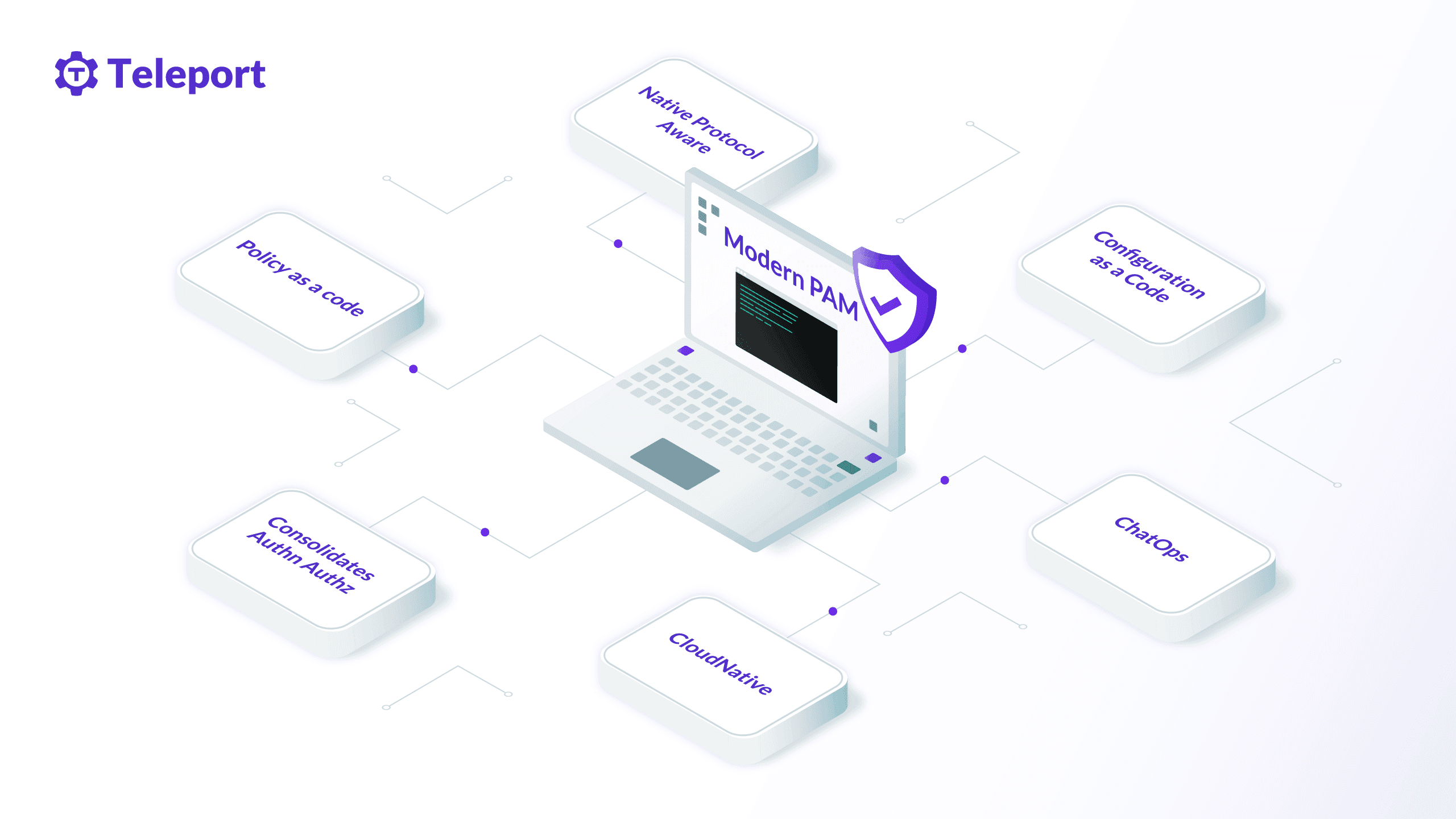
How to approach privileged access management in modern environments.
Following the newfound industry mantra for security, which tells organizations to "assume breach and optimize for resilience", privileged access management should also be treated similarly. Instead of forcing the traditional approach and focusing on monitoring privilege misuse, we should adapt to the modern infrastructure management workflow and consider how to minimize the security impact when privileged accounts are compromised.
Following are the four ways we should be approaching modern privileged access management for cloud and cloud-native environments.
1. Treat PAM as a first-class citizen
Just like how application security is treated as a first-class citizen in the software development process, privileged access management should be at the forefront of the infrastructure design process. Traditionally, teams design infrastructure, implement an access management solution and add privileged access control solutions. For maximum ROI in terms of security and cost, privileged access management solutions should be integrated with infrastructure operation workflows in a native manner, creating a seamless experience for users.
2. Consolidate privileged access across all environments
Enterprises should think about how to consolidate privileged accounts across all environments. Privileged access management is more challenging for teams that operate all three types of infrastructure: traditional co-located data centers, cloud infrastructure and cloud-native infrastructure. Without a proper consolidation of privileged accounts and access across all these environments, there is no way to standardize and enforce PAM best practices.
3. Adapt to modern infrastructure management workflows
The modern infrastructure management workflow comprised of infrastructure as code, GitOps and ChatOps for communication and alert makes it easy to enforce and standardize security management at scale. The level automation provided with API-based configuration makes it really handy to contain threats in the case of compromise of privileged accounts. The credential and access management process should also be automated and scriptable on demand. Innovations in DevSecOps like the principles of the DIE Triad (Distributed, Immutable, Ephemeral) are really promising, and privileged access management should be following the same path.
4. Assign zero standing privileges with auto-expiring credentials
Zero standing privilege (ZSP) reduces the window of potential misuse of sensitive accounts. You can further reduce this window by implementing auto-expiring credentials such as certificates with short TTL. Combining zero standing privilege with auto-expiring credentials is the recommended way to minimize the chance of account compromise and limit the blast radius of the compromised credentials.
Conclusion
Although technology and the concepts of access control remain the same, modern cloud and cloud-native environments require a new fresh approach to privileged access management. The increased attack surface of the privileged account, increased security risks of the privileged account, the need to keep up with modern, fast-paced workflows, and the hodgepodge landscape of traditional cloud and cloud-native environments all make it very challenging to implement traditional privileged access management solutions with higher security and cost ROI.
Teleport is a modern access platform that supercharges traditional access control technology with modern privileged access management requirements, which helps to consolidate access across all traditional, cloud and cloud-native environments. Learn how Teleport features address modern privileged access management requirements or talk to our representative today to understand how you can consolidate privileged access management across all traditional and modern environments using Teleport.
Table Of Contents
Teleport Newsletter
Stay up-to-date with the newest Teleport releases by subscribing to our monthly updates.
Tags

Subscribe to our newsletter