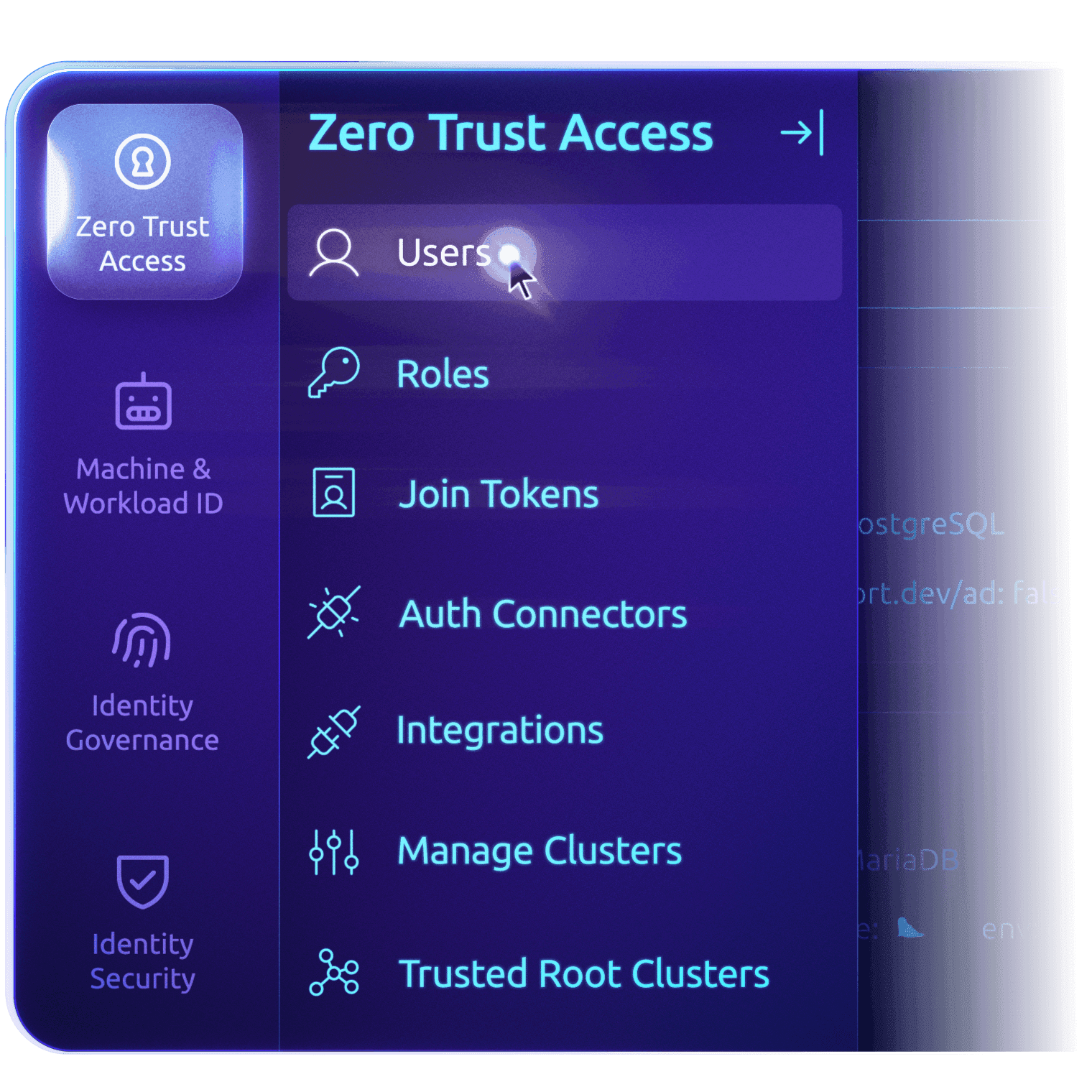
TELEPORT ZERO TRUST ACCESS
End Infrastructure
Complexity Chaos
Teleport gives your engineering teams and machine identities secure, identity-driven access to servers, databases, Kubernetes clusters, cloud consoles, internal applications, and MCP servers — without VPNs, passwords, or static credentials.
TRUSTED BY LEADERS


















ENGINEERING NEEDS IAM AT SCALE
Why Access Breaks
The modern threat landscape easily exploits credentials. Infrastructure complexity impedes engineers. At engineering scale, status quo identity and access models create security gaps, cumbersome audits, and cognitive overload for engineers.
Static credentials spread everywhere
VPNs and bastion hosts widen the attack surface
Standing privileges accumulate and persist
Device posture is unknown or ignored
Audit trails are fragmented or incomplete
Teleport Zero Trust Access
Improve resiliency, accelerate engineers
Teleport unifies identities and secures access for your entire infrastructure with:
Cryptographically-secured user, machine, and agent identities
Secretless authentication
Ephemeral privileges that expire
Session recording and audit trail
Eliminate secrets with cryptographic identity
Remove static credentials to eliminate the risk of credential theft and reuse, the #1 source of data breaches. Teleport locks down attack surfaces with cryptographic, phishing-resistant identities assigned to all users, machines and workloads, devices, resources, and AI (agents and LLMs).
User identities
Authenticate users without passwords leveraging biometric devices. Add Teleport as a security layer on top of your identity provider or use Teleport's SSO.
Machines & workloads
Issue and govern identities for your CI/CD automation systems, service accounts and microservices, and agentic AI and LLMs leveraging HSM and KMS.
Devices
Assign identities to enrolled TPM-equipped client devices (laptops, workstations, YubiKeys, and more).
Infrastructure
Assign a cryptographic identity to every application, server, database, and cloud resource. Supports SSH, RDP, databases, K8s, clouds, Model Context Protocol (MCP) and more.
Unify access control
Break access silos with a unified inventory of all infrastructure resources, eliminating the need for different access paths, passwords, shared secrets, vaults, or VPNs.
Teleport maintains a self-updating inventory of trusted computing resources, including servers, clouds, databases, Kubernetes clusters, web apps, MCP servers, and Git repositories, and enrolled client devices including laptops, workstations, YubiKeys, and more.
Reduce attack surface with ephemeral privileges
Enforce the practice of least privileged access and lower the operational overhead of managing privileges or enforcing policy.
Teleport replaces passwords, SSH keys, API tokens, and database credentials with ephemeral privileges, granted through short-lived certificates for all resources. These are bound to biometric devices and secure enclaves via Teleport's built-in certificate authority for X.509 and SSH certificates.
Eliminate VPN complexity with Teleport VNet
Teleport VNet connects identities to internal, non-browser TCP resources without VPNs, port forwarding, or custom DNS entries using familiar tools and workflows — eliminating exposure to the public internet.
Gain complete auditing and session visibility
Collect all events generated by humans, machines, and agents across your entire infrastructure in one place and export to any SIEM or threat detection platforms (including Teleport Identity Security) for further analysis.

Identity-Based Audit Events: Collect structured, detailed audit events for each session with identity, application and protocol data.
Dual Authorization: Require approval by multiple authorized team members for highly privileged actions (e.g., FedRAMP AC-3 & SOC 2).
Interactive Session Controls: Record, replay, join, and moderate interactive sessions for SSH and Kubernetes.
Session Sharing & Moderation: Require your highly privileged sessions to always include a moderator to prevent production and security incidents.
Live Sessions View: View every active authenticated connection across your entire infrastructure. Interfere if needed.
Session Recording & Playback: Record sessions for detailed review of who accessed what and what took place.
Accelerate Compliance: Teleport secures controls for FedRAMP, SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, NIS2, DORA, and more.
REDUCING INFRASTRUCTURE COMPLEXITY
Unify identity and access across all infrastructure resources
Teleport secures access for users, machines, and agents across cloud, code, and applications:
Servers
Databases
Kubernetes
Cloud consoles
Web apps
MCP servers
GitHub
BROAD STAKEHOLDER VALUE
Built for modern engineering teams
Security and platform engineering
- Enforce Zero Trust for identity, device, and access
- Eliminate credential and device risk
- Dramatically reduce attack surface
- Automate compliance enforcement
DevOps and SRE
- One workflow for everything
- No more managing SSH keys, VPNs, or bastions
- Fast onboarding/offboarding
- Faster incident response
Compliance and risk
AI teams
- Unified humans, machines & agents
- Unified access controls
- Built-in agentic AI and MCP security
- No technology silos
- Rapid innovation
Discover how GoTo, Indonesia’s largest digital platform, uses Teleport to modernize privileged access for faster engineering and reduced complexity across multi-cloud environments.

Trusted by teams building critical infrastructure.
Teleport is a strategic technology partner as they help our joint customers to scale their AWS resources in a secure manner. With Teleport’s Identity-Native Infrastructure Access solution, DevOps Engineers get a frictionless experience managing infrastructure that doesn’t require secrets while implementing zero trust architecture in AWS.
We use Teleport Access Requests in combination with Auth0 to easily manage access to our infrastructure. Prior to Teleport, we manually managed SSH keys and a bastion machine and it was an organizational nightmare.
We used to go through multiple steps just to access cloud resources, and now it happens almost instantly. Our engineers are really happy with the significant improvement in their workflow.
Teleport’s vision for Infrastructure Identity is a game-changer for securing hybrid infrastructure.
Teleport is a strategic technology partner as they help our joint customers to scale their AWS resources in a secure manner. With Teleport’s Identity-Native Infrastructure Access solution, DevOps Engineers get a frictionless experience managing infrastructure that doesn’t require secrets while implementing zero trust architecture in AWS.
We use Teleport Access Requests in combination with Auth0 to easily manage access to our infrastructure. Prior to Teleport, we manually managed SSH keys and a bastion machine and it was an organizational nightmare.
We used to go through multiple steps just to access cloud resources, and now it happens almost instantly. Our engineers are really happy with the significant improvement in their workflow.
Teleport’s vision for Infrastructure Identity is a game-changer for securing hybrid infrastructure.
With Teleport, we were even able to close the Kubernetes API without losing access for our engineers or automation tools. That alone was a huge win.
Teleport allows us to comply with the regulatory hurdles that come with running an international stock exchange. The use of bastion hosts, integration with our identity service and auditing capabilities give us a compliant way to access our internal infrastructure.
The Infrastructure Identity solution from Teleport offers a glimpse into the future of more secure, more resilient, and higher-velocity enterprise computing.
Teleport has made obtaining a FedRAMP-Moderate ATO that much more achievable via their FIPS 140-2 endpoints, ease in integration with our SSO and MFA , and the view into audit logs of remote connection sessions provide the appropriate insight for Continuous Monitoring.
Over the many years of using Teleport, it's been an essential piece of my infrastructure to help secure access, and centralize my infrastructure into one dashboard, without having to jump around… I'm not sure how I could go without it.
With Teleport, we were even able to close the Kubernetes API without losing access for our engineers or automation tools. That alone was a huge win.
Teleport allows us to comply with the regulatory hurdles that come with running an international stock exchange. The use of bastion hosts, integration with our identity service and auditing capabilities give us a compliant way to access our internal infrastructure.
The Infrastructure Identity solution from Teleport offers a glimpse into the future of more secure, more resilient, and higher-velocity enterprise computing.
Teleport has made obtaining a FedRAMP-Moderate ATO that much more achievable via their FIPS 140-2 endpoints, ease in integration with our SSO and MFA , and the view into audit logs of remote connection sessions provide the appropriate insight for Continuous Monitoring.
Over the many years of using Teleport, it's been an essential piece of my infrastructure to help secure access, and centralize my infrastructure into one dashboard, without having to jump around… I'm not sure how I could go without it.
Ready to Teleport?
Additional Resources
Teleport Zero Trust Access
Discover how Zero Trust Access works, including key concepts, use cases, and more.
Rush Street Interactive Levels Up Cloud Security
Learn how Rush Street Interactive eliminated standing access and open SSH ports while accelerating access provisioning 3x with Teleport.
Securing Identity in the Age of AI: A Buyer’s Guide to Teleport
Discover how Teleport solves AI identity risks with a platform built for the realities of AI-powered infrastructure.
Frequently Asked Questions
What is Teleport Zero Trust Access?
Teleport Zero Trust Access secures access to all your infrastructure (servers, databases, Kubernetes, cloud, and apps) using cryptographic identity, RBAC, and short-lived certificates instead of static credentials.
Is Teleport a VPN?
Teleport is not a VPN; it is an identity-based access platform that authenticates every connection with certificates and roles, and can connect clients to internal TCP and SSH services.
What is Teleport VNet, and how does it replace VPNs?
Teleport VNet proxies connections from a user’s machine to TCP apps and SSH servers behind Teleport’s proxy, so programs connect to internal resources without running a separate VPN tunnel.
Is Teleport a Zero Trust Network Access (ZTNA) software?
Teleport Zero Trust Access implements zero trust security for infrastructure by requiring strong identity and authorization for each session, applying the same principles as ZTNA to servers, databases, Kubernetes, and cloud consoles.
How do users log in if there are no passwords?
With Teleport, users authenticate via an external identity provider or passwordless methods (like WebAuthn hardware keys), and are issued short-lived certificates that they use to access infrastructure.











